v1.6 https://dwaves.de/software/familypicshare.de_v1.6.tar.gz https://dwaves.de/software/familypicshare.de_v1.6.tar.gz.sha512sum.txt released: improvements: thumbnail generator thanks to ImageMagick PHP extension can now also resize large image files (10MBytes and more) for slideshow it now uses resized versions of 1024px instead of the original file (which might be too […]
it is remarkable, that even the most simple tool, like exiftool seems to have (had?) a serious security problem: “Improper neutralization of user data in the DjVu file format in ExifTool versions 7.44 and up allows arbitrary code execution when […]
Yes! Being amongst the stars, exploring new worlds, is a great adventure… … even better if one brings some friends. and with mods… imho Kerbal Space Program is more than a game… it is a simulation and as such, it […]
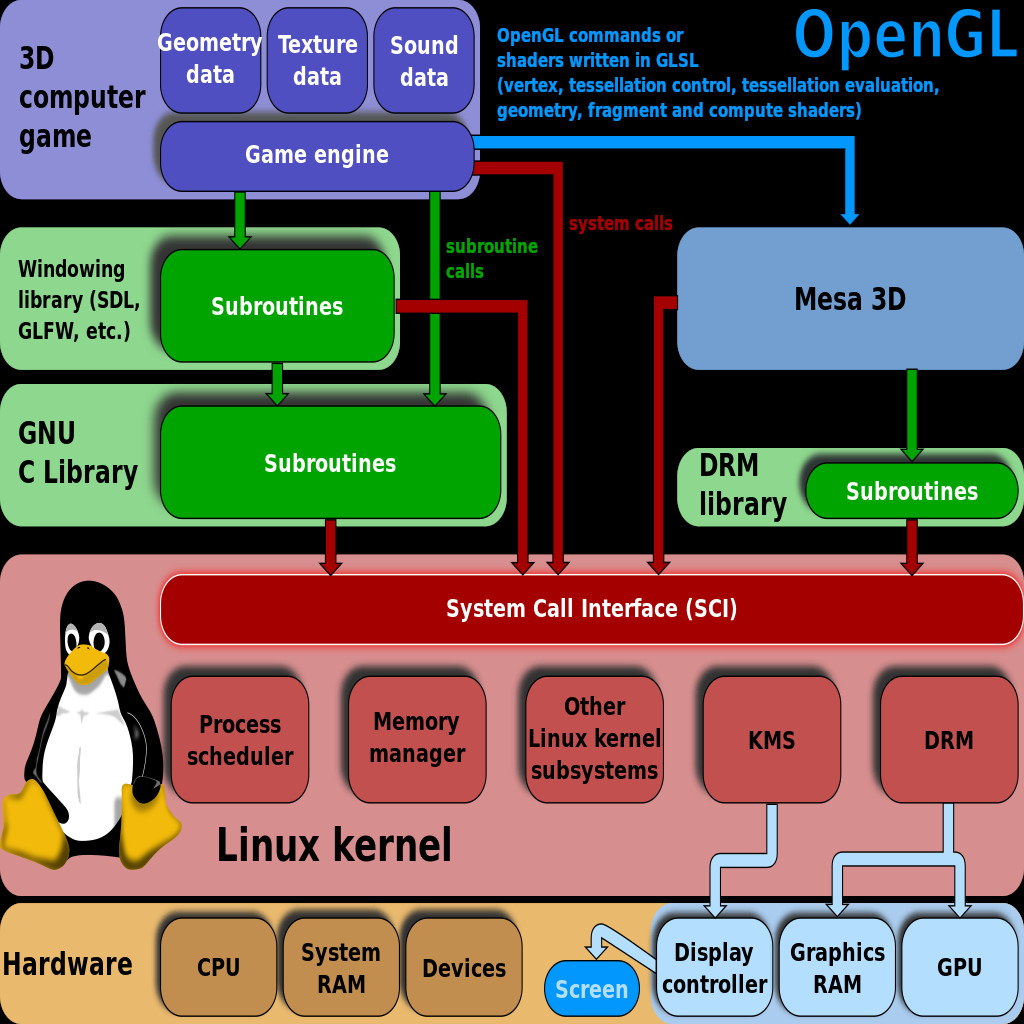
Why Hybrid? “Most hybrid kernels start as monolithic kernels and begin moving components into user land, primarily as security to support 3rd-party components and drivers which may be malicious or buggy. An example of a hybrid kernel design may keep […]
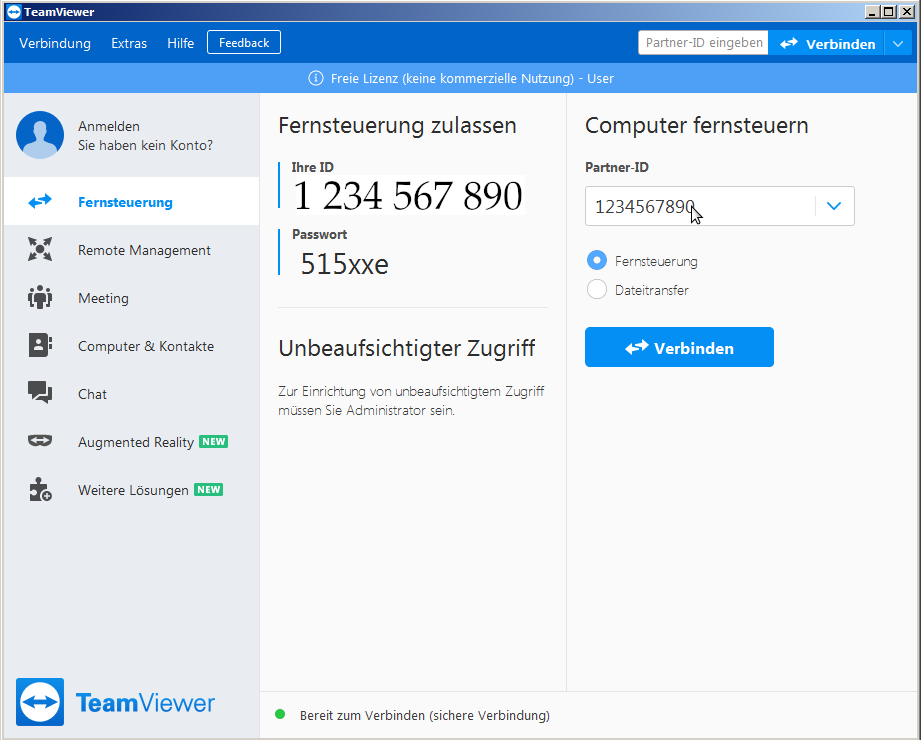
convenience vs security problem: remote support via internet in COVID19 pandemic days is basically a must for many companies, but does it have to run non-stop on computers that control sensitive machines and systems such as energy and water-supply? ABSOLUTELY […]
not sure if the news rang through… the Amazon Cloud (AWS) guy will be the new CEO of Amazon. What cloud? Amazon “cloud” Hetzner “cloud” cloud (centralized digital infrastructure) can be designed / implemented in different ways. from: the user/admin […]
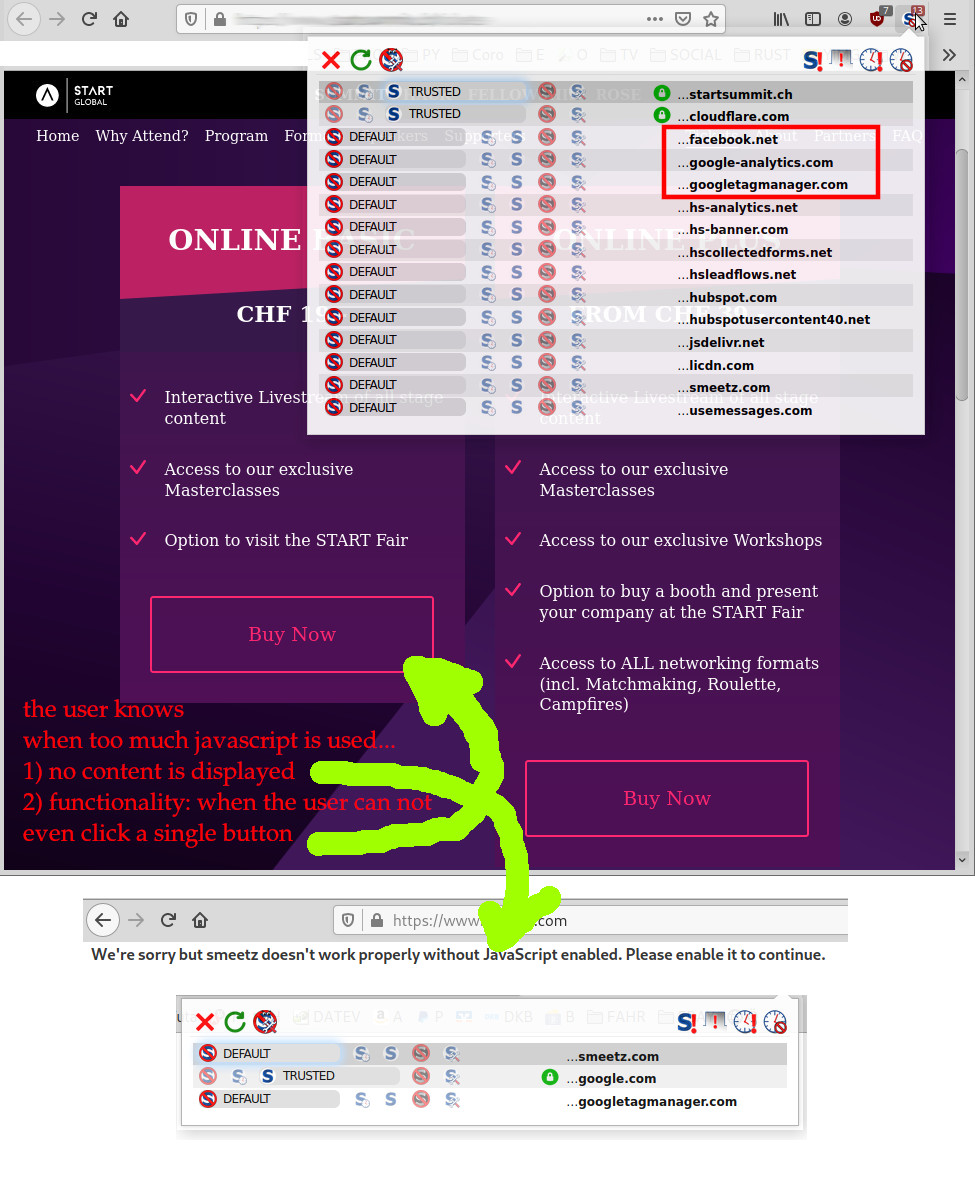
everyone wants a functional website is secure loads within max 10sec (absolute maximum imho) that actually works (menu is working, links not dead…) is rich in high quality content can be found via search engines a beautiful website (but not […]
what it is: it is a very detailed, tedious, noice physics, nice graphics voxel based build-stuff space, universe and planets simulation not like kerbal space program but equally tricky so definitely more aimed at the tech savvy engineer than at […]
BeyondCorp Google’s new Approach to Security – we need to know EVERYTHING about the user – in order to trust the user – The Age of Surveillance Capitalism first of… the good about JavaScript is (always say something positive […]
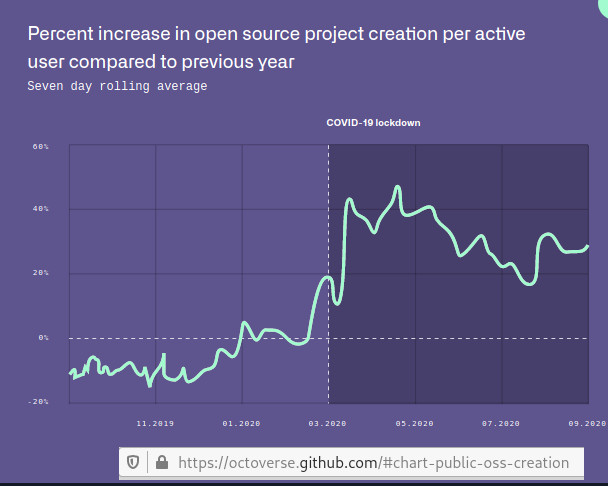
vs activity on StackOverflow: https://insights.stackoverflow.com/survey/2020#technology-most-loved-dreaded-and-wanted-languages-loved comment: there is a saying “never trust a chart, that you did not fake yourself” X-D (which probably just means: the data will never be a perfectly representation of reality (because some users block JavaScript […]
SecurityLab, [03.12.20 11:15] Vulnerabilities in open source software can go undetected for more than four years before being discovered. According to the GitHub State of the Octoverse annual report, the use of open source projects, components, and libraries is more […]
accroding to BleepingComputer: “zero-day vulnerability in their VPN products” (so not FallOut of SolarWinds-orion-auto-update-software-supply-chain) “…have information about hacking of a well-known firewall vendor and other security products by this they are silent and do not release press releases for their […]
update: 2024-04: having problem connecting to camera with vlc? (rstp not well documented or not working at all? try this: easy camera stream identification with ONVIF: it is a DAMN hussle, because EVERY camera vendor does it’s own rstp://user:password:ip.ad.dr.ess:/some/url/stream and […]
“floating point arithmetic is considered an esoteric subject by many people” (src: What Every Computer Scientist Should Know About Floating Point Arithmetic – David Goldberg 1991.pdf) some even do “transcendental calculations” (src) make no mistake: computer make mistakes too! not […]
SecurityLab, [02.11.20 11:52] The 50-year-old businessman (Hunter Biden?) in April 2019 brought his device to the IT store Mac Shop in Delaware for repair, but never returned to pick it up. The device was soon seized by the FBI. According […]
DNS servers are the “yellow pages” “phone book” of the internet. whoever is running DNS servers get’s to know all queries send (what client is requesting and probably connecting to what address… basically: what websites the user have visited, this […]
contains advertisement. to be honest, it is hard to keep up the speed at which cyber incidents are reported. here is the latest take on “Russian IT Sec Updates”. have phun! SecurityLab, [28.09.20 08:20] Last month, TikTok developers rolled […]
data google tries to collect from users: BeyondCorp Google’s new Approach to Security – we need to know EVERYTHING about the user – in order to trust the user – The Age of Surveillance Capitalism (it is probably only the […]
SecurityLab, [14.07.20 15:35] The Electronic Frontier Foundation (EFF) has unveiled a new database demonstrating how and where us law enforcement agencies use tracking technologies. A map of the use of tracking technologies in the United States is presented (https://www.securitylab.ru/news/510018.php) SecurityLab, […]
All SmartPhones are spies! that’s why Merkel keeps the Nokia from 1995 (even if that device is spied on as well, because it can not end2end encrypt sms or phone calls (*FAIL*! X-D)) Putin does not have a mobile phone […]
because of unprofessional journalism (no sources given to the origin of the pictures) it is not clear if those pictures are real pictures taken by a space probe and send back to earth or some CGI 3D renderings! SHAME ON […]
SecurityLab, [04.06.20 15:05] The Chinese-language cybercrime group Cycldek (also known as Goblin Panda or Conimes) has developed the malicious tool USBCulprit to carry out attacks on physically isolated systems and steal confidential data. Cycldek APT has developed a malware for […]
this age of mass surveillance… … who is observing “the observers”? guess with it-security and internet-security (internet = roads, cars = computers that users use every day) it is like with real-life-security – there is no 100% security. all users […]
“The primary reason for the ‘Tainted:‘ string is to tell kernel debuggers if this is a clean kernel or if anything unusual has occurred. Tainting is permanent: even if an offending module is unloaded, the tainted value remains to indicate […]
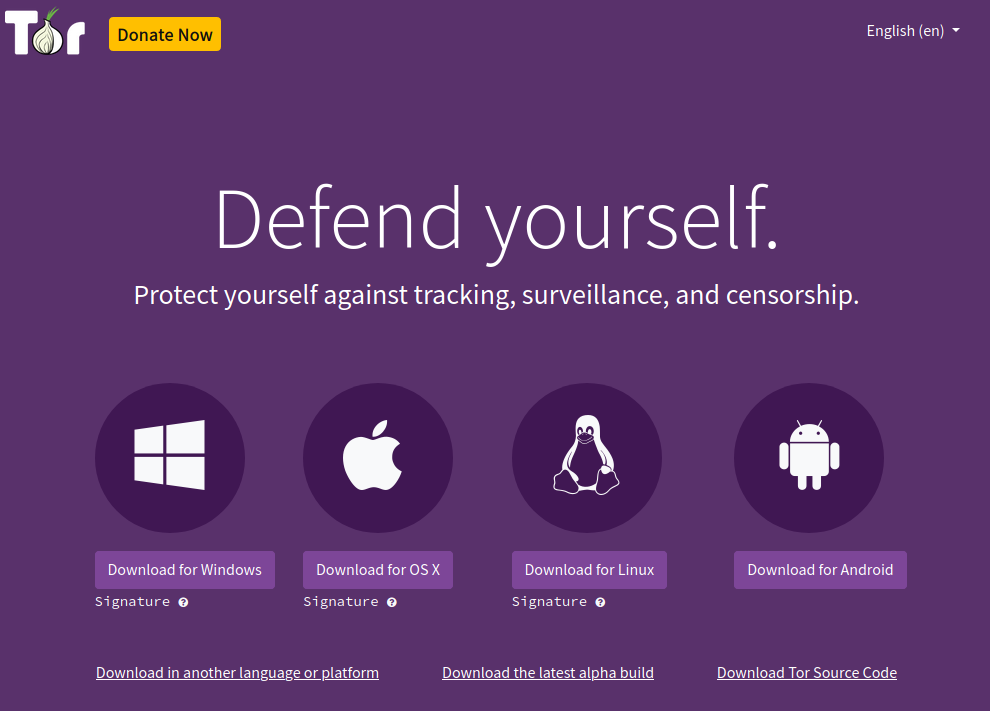
Tor is easier to use than ever superb usability! Tor is now super easy to use! (thanks all involved!) just get the tor bundle – it is tor bundled with firefox https://www.torproject.org/download/ Tor visualized: most users are legit: but criminals […]
home of git’s git repo: https://git-scm.com/ # to clone git’s git repo git clone https://git.kernel.org/pub/scm/git/git.git # as can be seen there, it is STILL under active development written in primarily in C, with GUI and programming scripts written in Shell […]
Julia Reda: control copyright Das nächste Kapitel von #SaveYourInternet: Vor einem Jahr sind wir alle gegen #Uploadfilter auf die Straße gegangen – mit meinem @freiheitsrechte-Projekt #ControlC gehen wir für die Kommunikationsfreiheit auch vor Gericht. Sei dabei! https://t.co/dhC7tD0oPm pic.twitter.com/iPNnXLLsfY — Felix […]
SecurityLab, [26.03.20 08:10] The largest free hosting provider on the darknet, Daniel’s Hosting, was hacked for the second time in 16 months, and stopped working on Wednesday, March 25. Unknown attackers deleted the entire database of the hosting provider, as […]
As with all hot debated topics: Linus Torvald’s “show me the source” in this case, the source of one’s informations (always give the source!) is IMPORTANT for the information’s credibility. It is absolutely vital in science to give all sources […]
SecurityLab, [24.12.19 10: 05] An attempt by Chinese farmers to fight drones infecting pigs with African plague has disabled the navigation systems of some aircraft. According to the South China Morning Post, an unauthorized GPS signal jamming device was installed […]