SecurityLab, [03.12.20 11:15]
Vulnerabilities in open source software can go undetected for more than four years before being discovered.
According to the GitHub State of the Octoverse annual report, the use of open source projects, components, and libraries is more common than ever.
https://www.securitylab.ru/news/514535.php
SecurityLab, [04.12.20 08:30]
About 8% of Android apps available in the official Google Play Store contain vulnerabilities in the popular Android library.
According to experts from Check Point, the problem is in older versions of Play Core, a Java library that developers can embed in their applications to interact with the official Play Store portal.
https://www.securitylab.ru/news/514557.php
SecurityLab, [04.12.20 09:25]
Former US intelligence officer Edward Snowden addressed Donald Trump via Twitter with a call to pardon the founder of the WikiLeaks portal Julian Assange, while Trump still holds the post of US president.
https://www.securitylab.ru/news/514558.php
(but to no avail… new hopes are that Biden will step up and pardon Snowden & Assange (fingers crossed))
SecurityLab, [04.12.20 10:25]
Fraudsters have armed themselves with a new strategy to extort bank card data from Russians.
The attackers send out fake notifications about debts for housing and communal services, which allegedly appeared during the quarantine and the transition to remote operation.
This was told to RBC by a representative of VTB.
https://www.securitylab.ru/news/514559.php
SecurityLab, [04.12.20 13:40]
A team of specialists from GoSecure, Trend Micro and Stratosphere Laboratory spoke about the new service, which operates on the business model “obfuscation-as-a-service” (obfuscation-as-a-service) and is a vivid example of the sustainability of the cybercrime economy in terms of meeting the demand in the cybercrime market.
In this case, enterprising hackers have developed a fully automated service platform to protect Android malware APKs from detection by antivirus solutions.
https://www.securitylab.ru/news/514563.php
SecurityLab, [04.12.20 15:50]
Researchers of the Dutch company Sansec have discovered skimming malware for stealing payment data, which cybercriminals hide in the most visible place – in the icons of popular social networks.
Details:
According to the researchers, the attackers are hiding the payload in the buttons “Share”, disguised as Facebook, Twitter and Instagram. Skimming SOFTWARE is JavaScript code embedded by Magecart groups in checkout forms on compromised e-Commerce sites. Once uploaded to the hacked site, the script automatically steals payment and personal information entered by users and transmits it to servers controlled by the attackers.
Malware for collecting payment data uses a trick with a double payload structure – the source code of the skimmer script is hidden in the “Share” icon on social networks, uploaded as an HTML svg element with the path element as a container.
The syntax for masking the skimmer source code as a social network button perfectly mimics an svg element named using social media names (for example, facebook_full, twitter_full, instagram_full, youtube_full, pinterest_full, and google_full). A separate decoder deployed on the server of the e-Commerce site is used to extract and execute the code.
This tactic increases the chances of cybercriminals avoiding detection. Even if one of the two components of malware is identified, its true purpose may escape a cursory analysis, since the loader will not necessarily be stored in the same place as the payload.
This case is not the first time that attackers have used skimmers hidden by steganography. However, it is the first time that malware is hidden in a “perfectly authentic image,” the researchers note.
“As a result, security scanners can no longer find malware by simply checking the valid syntax,” Sansec explained.
https://www.securitylab.ru/news/514564.php
Payment skimmer hides in social media buttons
src of src: https://sansec.io/research/svg-malware
SecurityLab, [05.12.20 11:00]
A hacker group from Iran has published a video showing the process of compromising the automated control system of a water supply facility in Israel.
https://www.securitylab.ru/news/514568.php
SecurityLab, [05.12.20 11:15]
Unknown hackers attacked the network of PickPoint postamats, as a result of which there was a failure in their work.
https://www.securitylab.ru/news/514569.php
SecurityLab, [07.12.20 08:10]
In the capital of Kazakhstan, Nur-Sultan, cyber training was held, in which citizens had to install a national security certificate on their devices.
https://www.securitylab.ru/news/514583.php
SecurityLab, [07.12.20 09:08]
The experts of “Jet Infosystem” will analyze in detail the information security functionality available in Microsoft 365.
https://www.securitylab.ru/news/514581.php
SecurityLab, [07.12.20 11:10]
Between December 2018 and October 2019, more than 20 million Gionee phones were intentionally infected with Trojans.
The Chinese authorities found that Beijing Baice Technology and Shenzhen Zhipu Technology (a subsidiary of Gionee) introduced malware into the phones of Gionee users by updating the Story Lock Screen app. The software was updated automatically on infected Gionee devices without the users ‘ knowledge.
https://www.securitylab.ru/news/514592.php
SecurityLab, [07.12.20 12:15]
Italian law enforcement officials have arrested two suspects in the theft of confidential data from a large Italian engineering holding company Leonardo using malware.
https://www.securitylab.ru/news/514591.php
hint: Leonardo is an italian hightech weapons company
SecurityLab, [07.12.20 12:20]
Users of the MetaMask cryptocurrency wallet have become victims of an ongoing phishing campaign, in which criminals use Google ads to steal money.
The victims lost their savings after clicking on a fraudulent ad promoted in a search query as the MetaMask site.
https://www.securitylab.ru/news/514600.php
SecurityLab, [07.12.20 15:55]
Companies wishing to organize a hackathon should take this very seriously, so as not to repeat the sad experience of the Australian travel agency Flight Centre.
According to The Register, three years ago during a hackathon in the company there was a data leak, and it happened through the fault of the developer.
Details:
In March 2017, the travel Agency held an event, the so-called “design jam”, with the aim of “creating a technological solution for travel agents that can improve customer support in the sales process.” During the hackathon, 16 teams with a total of 90 people gained access to 106 million rows of data containing 6,121,565 customer records.
Flight center was sure that they had cleaned up the data set provided to the hackathon participants, deleting sensitive information and leaving only dates of birth and reservation information. The company’s specialists checked the top 1 thousand lines in each file, but, as it turned out, this was not enough. Each file contained 28 million lines, and when the hackathon participants began to study them in detail, they found credit card numbers in a free text field.
https://www.securitylab.ru/news/514615.php
SecurityLab, [07.12.20 16:05]
A Paris court found Alexander Vinnik guilty of aggravated money laundering.
The Russian was sentenced to five years in prison and ordered to pay a fine of 100,000€ including compensation to the affected parties.
This was reported by the TASS news agency.
https://www.securitylab.ru/news/514616.php
Background: Alexander Vinnik (Russian: Александр Винник) is a Russian computer expert. From 2011 to 2017, he worked at BTC-e, a Russian cryptocurrency exchange. He is currently awaiting trial in France on charges of money laundering and extortion.
On July 25, 2017, Vinnik was arrested in Greece at the request of the U.S. on suspicion of laundering $4 billion through BTC-e.[6] Vinnik has denied the charges.[7]
In late July 2017, the U.S. requested Vinnik’s extradition from Greece.[8] In early October 2017, his extradition was requested by the Prosecutor General of Russia.[9] In late June 2018, France requested his extradition, accusing him of fraud.[10] In early July 2018, Russia submitted a new extradition request, reportedly based on a confession to additional hacking offenses.[11]
In November 2018, Vinnik went on a three-month hunger strike in protest of his detainment in Greece.[12]
In January 2020, Vinnik was extradited to France.[13] In June 2020, New Zealand Police announced the seizure of $90 million from WME Capital Management, a company in New Zealand registered to Vinnik.[14][15]
(src: Wiki)
SecurityLab, [08.12.20 08:35]
A team of CyberNews Investigation specialists conducted a study of what are the most popular words people use when creating passwords.
In total, the experts were able to analyze 15.2 billion passwords, of which 2.2 billion were unique, and divided them into different categories of terms used.
https://www.securitylab.ru/news/514620.php
Why IoT devices without automatic regular updates are a bad idea:
SecurityLab, [08.12.20 09:00]
Forescout, a company specializing in the security of IoT devices, has discovered 33 vulnerabilities in open-source Internet protocols, making millions of embedded devices open to cyber attacks, including information interception, denial of service, and taking full control.
The list of affected devices includes smart home sensors, including those for lighting control, barcode scanners, industrial network equipment, and even automated process control systems.
They are very difficult, if not impossible, to update, and attackers can take advantage of these vulnerabilities as an entry point to many networks.
https://www.securitylab.ru/news/514621.php
advertisement:
SecurityLab, [08.12.20 11:39]
In 2020, 500+ specialists began their journey in cybersecurity with the intensive
“Pentesting: Level 0”
Take the first step and you! Take part in conferences with an experienced pentester and get:
— Structured basic knowledge about exploiting vulnerabilities — Experience hacking a web application — Understanding how to use pentest skills for career development — Meeting top hackers and HackerU experts — First CTF and bonuses for admission to the main program
The cost of participation until the new year is only 2300 RUB
Make yourself a gift in the form of new knowledge and community-sign up for intensive: https://is.gd/ypIov0
Holy CRAP! Micro$oft just screwed up AGAIN!
SecurityLab, [08.12.20 11:45]
Security researcher from Evolution Gaming Oskars Vegeris (Oskars Vegeris) discovered a remote code execution vulnerability in the Microsoft Teams corporate platform, which does not require user participation.
Exploiting the vulnerability allows an attacker to execute arbitrary code by sending a specially crafted chat message and compromise the victim’s system.
https://www.securitylab.ru/news/514622.php
SecurityLab, [08.12.20 11:50]
The US National Security Agency has issued a warning that Russian hackers are exploiting a recently discovered vulnerability in VMware products to install malware in the networks of organizations in order to steal confidential information.
What group is behind the attacks, and when these attacks began, the NSA does not specify.
https://www.securitylab.ru/news/514623.php
SecurityLab, [08.12.20 15:10]
The Ministry of Digital Development, Communications and Mass Media of the Russian Federation analyzed about 100 different applications from software manufacturers and formed a list of domestic programs recommended for pre-installation on new mobile devices.
https://www.securitylab.ru/news/514631.php
SecurityLab, [08.12.20 15:25]
Thirteen European countries, including Germany, France and Spain, have joined forces to invest in the production of processors and semiconductors.
The states intend to develop their semiconductor technologies, including technologies that are key to the production of interconnected devices and data processing, to compete with the United States and Asian countries.
Details:
Thirteen European countries, including Germany, France and Spain, have joined forces to invest in the production of processors and semiconductors.
The States intend to develop their semiconductor technologies, including technologies that are key to the production of interconnected devices and data processing, in order to compete with the United States and Asian countries.
Currently, the share of European countries in the global semiconductor market is only 10%.
Moreover, European manufacturers rely on foreign-made chips.
According to Reuters, dependence on foreign semiconductor manufacturers has become particularly acute during the coronavirus pandemic.
Moreover, European manufacturers have become increasingly concerned about the safety of foreign technologies.
In connection with all the above, a group of European countries decided to join forces to get rid of dependence on foreign-made chips used in the automotive industry, the production of medical and network equipment, mobile devices, etc.
Earlier this year, the European Union agreed to allocate 145 billion euros to support digital projects – a fifth of the funds intended for the recovery of the European economy after the pandemic.
Thirteen countries will work together to increase Europe’s presence in the global electronics market.
The group will reach out to various companies to create industrial alliances for research and investment for future projects and find additional sources of funding.
https://www.securitylab.ru/news/514632.php
SecurityLab, [08.12.20 18:35]
Microsoft and Sberbank have created a robot that can handle objects almost like a human.
As follows from the presentation video of the Sberbank Robotics Laboratory division, the robot can interact with objects that change their physical shape, for example, with bags with loose contents.
In contrast to grabbing something solid, manipulating such objects due to an unstable center of gravity requires constant calculation of the changing position and orientation of the gripper in each individual case.
https://www.securitylab.ru/news/514643.php
SecurityLab, [08.12.20 18:45]
Eugene Kaspersky announced the upcoming release of smartphones under its own brand in 2021.
The gadgets will be equipped with a new OS that will provide users with protection from hacker attacks.
https://www.securitylab.ru/news/514644.php
SecurityLab, [08.12.20 21:55]
The company explained that the PickPoint team managed to save most of the orders from a hacker attack.
Within 20 minutes from the moment of hacking, the developers deactivated about 80% of the 2,732 infected posts, so that the cell doors did not open.
By December 7, the company managed to restore the operation of the affected points by 95%.
In addition, new software is installed on the pedestals.
The general director of PickPoint Nadezhda Romanova said that she appealed to the police with a request to open a case on the theft of parcels.
https://www.securitylab.ru/news/514645.php
SecurityLab, [09.12.20 08:15]
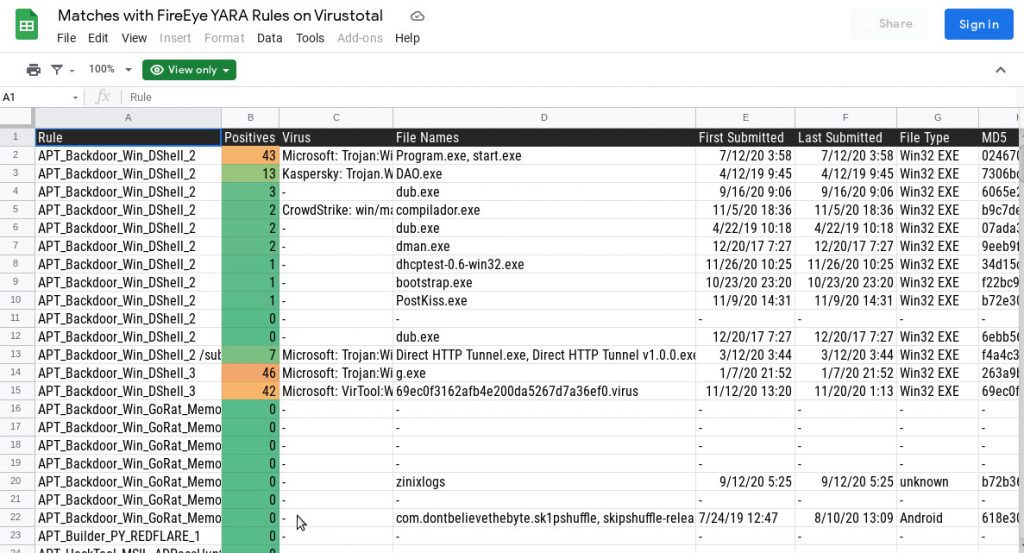
For many years, government organizations and private companies around the world have turned to the American information security company FireEye for help in the case of the most complex cyber attacks carried out by highly skilled hackers.
Now, it seems, these hackers have decided to take revenge on her.
Details:
On Tuesday, December 8, the company reported a cyberattack on its systems by “a state with offensive capabilities of the highest level.” With the help of” innovative techniques”, the attackers managed to steal FireEye tools, probably with the aim of using them in further attacks on targets around the world. It’s like robbers robbing a Bank of every penny, and then stealing tools to investigate a robbery.
On Tuesday evening, just after the stock market closed, FireEye contacted the FBI. Although the company does not specify who exactly is behind the attack, the description of the incident and the fact that the FBI has turned the case over to its specialists in Russia, leaves no doubt who is the main suspect, reports the New York Times. It is also quite obvious that the attackers were interested in tools for the so – called “red teams” – replicas of the most sophisticated hacking tools in the world, used by FireEye (of course, only with the client’s permission) to search for vulnerabilities in their systems. Most of these tools are stored in a highly secure digital vault.
In the attack on FireEye, hackers went to extraordinary lengths to circumvent detection-they created several thousand IP addresses (many of them located in the United States) that had never been used in attacks before. The use of these locations has allowed attackers to reliably hide your location.
The incident is the largest theft of cybersecurity tools since 2016, when cybercriminals calling themselves ShadowBrokers stole malware and exploits from the national security Agency’s Arsenal. For months, ShadowBrokers published the stolen tools, providing cybercriminals and “government” hackers with what one former NSA employee called ” keys to the digital Kingdom.”
NSA malware is much more effective than FireEye tools, as it was created to perform certain tasks, and FireEye tools are based on malware used in various attacks. But using stolen tools, “government” hackers can hide their true origin.
FireEye has published key elements of its stolen tools so that users around the world can detect the approach of attacks.
https://www.securitylab.ru/news/514688.php
SecurityLab, [09.12.20 08:25]
Adobe has released the latest planned update for Adobe Flash Player.
As previously announced, Flash Player will be supported until the end of December 31, 2020.
Moreover, Adobe itself will block the launch of Flash content in Flash Player after January 12, 2021, so users will not be able to use it.
https://www.securitylab.ru/news/514689.php
advertisement:
SecurityLab, [09.12.20 09:04]
Our chat rooms
https://t.me/ngfw_russia -we invite you to participate in the discussion of any issues related to ngfw. representatives of vendors, integrators, and customers are present in the chat.
https://t.me/secwaf -the chat discusses the configuration and operation of modern WAF systems.
SecurityLab, [09.12.20 11:15]
The Moscow authorities intend to spend almost 59.9 million rubles on the introduction of a special function in the city’s video surveillance system that allows you to recognize people by silhouettes.
The relevant tenders of JSC “Electronic Moscow”, owned by the Property Department, are posted on the public procurement website.
https://www.securitylab.ru/news/514697.php
advertisement:
SecurityLab, [09.12.20 11:59]
Do you work with Reverse and Pentest? Come for advanced skills in demo lessons.
A demo session will be held on December 17
“Windows AD information gathering, privilege escalation. Exploits and vulnerabilities of the last 5 years”. Together with Alexander Kolesnikov.
To register for the class, take the entrance test: https://otus.pw/u9W7/
16 Dec demo lesson “Analysis shellcode”. Together with Artur Pakulov, you will analyze a sample of the malware, which is a compressed piece of silkcode.
To register for the class, take the entrance test: https://otus.pw/oSsZ/
SecurityLab, [09.12.20 14:40]
Cloudflare and Apple engineers have created a new Internet protocol designed to fill one of the most serious gaps in Internet security, the existence of which many do not even know.
The protocol, called Oblivious DNS-over-HTTPS, or ODoH for short, will make it much more difficult for Internet service providers to track user activity on the Network.
https://www.securitylab.ru/news/514696.php
SecurityLab, [09.12.20 15:05]
Files (Excel, Word, JPG) with personal data of Muscovites who have had a coronavirus infection (COVID-19) are now freely available.
The Network turned out to have an archive of about 940 MB in size, containing 362 files.
Details:
Links to Google Docs and closed Telegram chats of hospitals and clinics were also publicly available.
Moscow authorities have confirmed the leak of personal data of Muscovites who have had COVID-19.
“During the verification of information about leaks of personal data of Muscovites who had been ill with coronavirus, it was established that there were no hacks or any other unauthorized interference in the work of the information systems of the Moscow Government. The leak was caused by a human factor: employees who were engaged in processing official documents allowed the transfer of these files to third parties. The audit continues, and measures will be taken based on its results,” said Eduard Lysenko, head of the Moscow information technology Department.
https://www.securitylab.ru/news/514700.php
SecurityLab, [09.12.20 15:40]
Smart speakers like Google Home and Amazon Echo can be used by hackers to steal PIN codes or passwords typed on the screen of nearby mobile devices.
This conclusion was made by experts from the University of Cambridge based on the results of the study.
https://www.securitylab.ru/news/514701.php
SecurityLab, [09.12.20 21:35]
The FBI detained Russian Kirill Firsov at JFK Airport in New York in March of this year.
After that, in a court in California, he was charged with managing the online platform deer on the darknet, which sold stolen user credentials — from Netflix, Hulu, Facebook, Twitter, Vkontakte and other platforms.
https://www.securitylab.ru/news/514709.php
SecurityLab, [10.12.20 08:05]
Facebook Instagram and WhatsApp, the U.S. Federal Trade Commission, along with a coalition of attorneys general from 48 states and territories, filed two separate antitrust lawsuits against Facebook on Wednesday, December 9, affecting the company’s largest acquisitions, Instagram and WhatsApp.
The plaintiffs accuse it of unfair competition and demand legal protection, which could lead to the court obliging Facebook to sell both applications.
https://www.securitylab.ru/news/514713.php
wow! what a news!
but to really make a difference in 1984 terms, what would have to change/reforms needed:
- WhatsApp should become a foundation: a independent (by the users?) elected team of people should run it
- the complete WhatsApp infrastructure should become Open Source
- true end-2-end encryption witha publicly known “good” cypher would need to be implemented (also storage of messages & data on the server need to be encrypted)
- users should be able to chose:
- collect and sell data (make transparent what data is collected and sold to whom and how much was paid)
- to pay for the service
SecurityLab, [10.12.20 08:25]
The creators of the WhatsApp messenger opposed Apple’s requirements for app developers to provide users with information about the collected data.
According to representatives of WhatsApp, this behavior is anti-competitive, since the applications of the tech giant itself are initially pre-installed on the iPhone and do not require downloading from the App Store, where new privacy shortcuts will be displayed.
https://www.securitylab.ru/news/514714.php
SecurityLab, [10.12.20 09:15]
The European Medicines Agency (EALA), which is responsible for the certification of vaccines against COVID-19, has been subjected to a cyber attack of an unknown nature.
According to a notice on the EALS website, the agency is currently investigating the incident together with law enforcement agencies.
https://www.securitylab.ru/news/514715.php
SecurityLab, [10.12.20 10:15]
The new season of the Magic People IT Channel Awards 2020 – the business awards about people who create additional value in IT-has started.
Vendor Categories
Best PSA/RMM Vendor of the Year
Winner: Barracuda MSP
Best COVID-19 Responder
Winner: IGEL
Best Managed Security Services Offering
Winner: Sophos
Security Innovation Award
Winner: Darktrace
Artificial Intelligence Innovation Award
Winner: FastFetch Coroporation
Cloud Partner Program of the Year
Winner: Sherweb
Cloud Innovation Award
Winner: Red Hat
Security Partner Program of the Year
Winner: WatchGuard
Vendor Innovation Award
Winner: LogicMonitor
Security Vendor of the Year
Winner: FireEye
Partner Program of the Year
Winner: Cohesity
Vendor of the Year
Winner: Vertiv
Channel Chief of the Year
Winner: Mark Porter, High Wire Networks
Security Channel Chief of the Year
Winner: Chris Carter, FireEye
New Channel Chief of the Year
Winner: Ernest Jones, Red Hat
MSP Categories
Best Place to Work
Winner: Iuvo Technologies
Customer Satisfaction Award
Winner: 2nd Watch
Best COVID-19 related initiative of the year
Winner: Logicalis US
Innovative Project Award
Winner: Mejeticks
MSSP of the Year
Winner: Success
Industry Specialist Award
Winner: Radix
MSP of the Year
Winner: Cascadeo
Cloud Services Provider of the Year
Winner: ClearScale
Independent Expert Council – 15 representatives of the IT sector, including CRN/RE, https://Anti-Malware.ru, IDC-will select the finalists and winners of the award based on the results of 2020.
One of the nominations is dedicated to projects in the field of information security.
Preliminary applications are accepted on the website it-channel-awards.ru until February 15, 2021.
https://www.securitylab.ru/news/514720.php
SecurityLab, [10.12.20 10:20]
More than 85,000 SQL databases are sold on the hacker portal in the darknet at a price of $550 per database.
Cybercriminals use the portal as part of an increasingly popular extortionate scheme with databases, writes ZDNet.
https://www.securitylab.ru/news/514721.php
SecurityLab, [10.12.20 16:00]
The National Commission for Information Technology and Human Rights (Commission nationale de l’informatique et des libertés, CNIL) fined Google 100 million euros for violating the rules on the use of cookies.
Tech giant Amazon was also fined, but only 35 million euros.
https://www.securitylab.ru/news/514730.php
SecurityLab, [10.12.20 19:05]
This concept is outlined in the document “Creating a conversational chatbot of a certain person”, posted on the website of the US Patent and Trademark Office (USPTO).
According to the idea of Microsoft specialists, a virtual clone could not just reproduce the voice of the deceased, but exactly imitate his manner of communication.
https://www.securitylab.ru/news/514739.php
advertisements:
SecurityLab, [11.12.20 05:54]
[Forwarded from Announcements of the best information security events]
CROC and Cisco invite you to the online meetup ” Service Model in Business Strategy 2021: New Challenges and Opportunities”
The meetup will take place on December 15 at 16:00 Moscow time. Using real-world case studies, the speakers will tell you what the hybrid service model gives businesses.
Managing geographically distributed branches poses complex challenges for IT. Together with the business, the responsibility for the reliable operation of the infrastructure is growing. It is important to reduce equipment downtime and provide 24/7 centralized technical support.
On December 15, leading service experts CROC and Cisco will talk about how the transition to a hybrid service model will help optimize technical support costs and avoid losses associated with equipment failures.
You will find out:
● What is the service model and what services are included in it
● What does it give to a geographically distributed business?
● What are the advantages and difficulties of implementing this approach?
● How to quickly put new branches into operation
● What tasks do Russian companies set for service support?
Visiting the online meetup will be interesting for employees and managers of service and IT departments.
Duration of the event: 1 hour (+30 minutes) Q & A session)
Participation is free of charge
SecurityLab, [11.12.20 08:20]
The European Union will oblige major technology companies such as Facebook and Amazon to take more responsibility for controlling content on the Internet, otherwise they will face fines.
This is reported by journalists of the Financial Times, who got acquainted with the new bill, which will be published next week.
https://www.securitylab.ru/news/514744.php
SecurityLab, [11.12.20 09:40]
Microsoft has warned about a new malicious campaign targeting users of Google Chrome, Microsoft Edge, Mozilla Firefox and Yandex.
Browser on Windows PCs.
According to the researchers, at least since May of this year, unknown cybercriminals have been distributing a family of browser modifiers called Adrozek, which mainly embed ads in search results pages.
https://www.securitylab.ru/news/514746.php
SecurityLab, [11.12.20 11:35]
Critical vulnerabilities were discovered in the main network library that provides the functionality of Valve’s online games, the exploitation of which allowed attackers to remotely cause video games to malfunction and even take control of affected third-party game servers to execute arbitrary code.
Details:
Critical vulnerabilities were discovered in the main network library that provides the functionality of Valve online games, the exploitation of which allowed attackers to remotely cause video games to crash and even take control of affected third-party game servers to execute arbitrary code.
The vulnerability (CVE-2020-6016, CVE-2020-6017, CVE-2020-6018 and CVE-2020-6019) was discovered in the library Game Networking Sockets (GNS) or Steam from Valve Sockets network library with open code, which provides “basic transport-level games”, allowing the combination of features of UDP and TCP with encryption support, greater reliability and peer-to-peer connection (P2P).
The attack is related to a problem in the package reassembly mechanism (CVE-2020-6016) and an error in the implementation of C++ iterators for sending a group of malicious packages to the target game server and triggering a stack buffer overflow, which ultimately causes the server to crash.
According to experts from Check Point, although the fix for these vulnerabilities was released back in September of this year, some third-party game developers have not yet updated their clients.
https://www.securitylab.ru/news/514745.php
SecurityLab, [11.12.20 14:40]
Many modern smartphones have a fingerprint scanner for authorizing access to the device, logging in to an account, confirming payments, and other transactions.
The scanner is designed for secure authentication, but researchers have discovered new ways to manipulate it for malicious purposes.
Security researchers from the Chinese University of Hong Kong and the company Sangfor Technologies have presented a user interface-based attack technique aimed at scanning fingerprints in Android applications.
https://www.securitylab.ru/news/514752.php
SecurityLab, [11.12.20 15:35]
Israeli manufacturers of tracking tools collect large amounts of geolocation data from mobile applications.
According to Forbes, one of these companies is the top-secret startup Bsightful, partially owned by the multibillion-dollar American company Verint Systems.
The second is a recognized player in the Israeli market for tracking technologies, Rayzone, whose Echo tool is designed to “mass collect data from all Internet users in the country.”
https://www.securitylab.ru/news/514757.php
SecurityLab, [12.12.20 15:00]
After the elections in Belarus, blocking the Internet has become a familiar part of the life of citizens of the country.
During mass protests, mobile Internet may be unavailable for several hours.
https://www.securitylab.ru/news/514764.php
SecurityLab, [13.12.20 21:40]
Hackers backed by a foreign government stole data from the U.S. Treasury Department and the National Telecommunications and Information Administration (NTIA).
At the same time, information about which country’s authorities are considered to be involved in the incident is not provided.
“The U.S. government is aware of these reports, and we are taking all necessary measures to identify and address any possible issues related to this situation,” White House Security Council spokesman John Ulliot told the agency.
https://www.securitylab.ru/news/514767.php
Worst-Case-Scenario for servers providing Updates: (those servers need to be 1000% secured!)
SecurityLab, [14.12.20 08:05]
Hackers funded by a foreign government broke into the computer networks of the American software manufacturer SolarWinds and implemented a malicious update for its Orion software in order to infect the networks of government and commercial organizations using it.
This was announced on Sunday, December 13, by the information security company FireEye.
https://www.securitylab.ru/news/514774.php
SecurityLab, [14.12.20 08:43]
[Forwarded from SecurityLab.ru the best materials]
In many urban areas, GPS doesn’t work very well. Buildings reflect GPS signals among themselves, creating interference for phones, as a result of which most modern devices determine their own location using a scattering of different techniques, including nearby Wi-Fi networks.
Using the SkyLift device and the ESP8266 family microcontroller, you can simulate fake networks, and as a result, the smartphone will “think” that it is in a completely different place.
Wi-Fi networks are a reliable way to determine the location of devices with limited access to GPS.
Attackers can exploit the vulnerability by spreading broadcast signals as if coming from known networks.
This technique does not work if there are many other Wi-Fi networks or a strong GPS signal nearby, but it has proven itself well in places where devices are forced to use the aGPS system.
https://www.securitylab.ru/analytics/514617.php
SecurityLab, [14.12.20 09:50]
A former Cisco engineer was sentenced to 24 months in prison for unauthorized access to the networks of an ex-employer and the destruction of servers that hosted the infrastructure of the Cisco Webex Teams application.
https://www.securitylab.ru/news/514776.php
another wordpress plugin exploited:
SecurityLab, [14.12.20 10:25]
Cybercriminals reset passwords from administrator accounts on sites running WordPress.
To do this, they exploit a zero-day vulnerability in the popular Easy WP SMTP plugin, which allows site owners to configure SMTP for outgoing emails.
https://www.securitylab.ru/news/514778.php
SecurityLab, [14.12.20 11:10]
The credentials of a number of medical institutions for connecting to a closed IT system leaked to the Network via the Yandex search bar.
https://www.securitylab.ru/news/514784.php
advertisements:
SecurityLab, [14.12.20 13:28]
[Forwarded from Announcements of the best information security events]
The Standoff: results of the team of defenders from Innostage Group of companies participating in the cyber battle
On December 17 (Moscow time) at 14:00 we invite you to take part in the webinar
Exactly one month has passed since the end of the world’s largest cyber battle, The Standoff, where teams of defenders ensured the security of the infrastructure of the digital metropolis from hacker traffic. Our team recorded 49 incidents during the exercise and conducted more than 20 hours of investigations. In addition, we have received a large base for analytical work and are now ready to share our results and conclusions.
Here’s what we’ll tell you :
– basic tactics and techniques used by hackers
– our actions to repel attacks and investigate the implementation of business risks
– the tools that we used to fight the attackers
-our actions that did not bring the desired effect
– general conclusions about what needs to be done for effective protection
Speakers-members of the CyberTatars and MoscowMasters (CT&MM) team of defenders):
Alexey Lobzin, Head of Cyberart Cyber Defense Services Promotion, Innostage Group
Anton Kalinin, Head of the group of analysts of the center for monitoring information security and responding to computer incidents CyberART, Innostage Group
At the end of the webinar, we will answer your questions.
Participation is free!
The webinar recording will be available to all registered participants at the end of the event.
SecurityLab, [14.12.20 15:00]
On Monday, December 14, users around the world faced problems with access to YouTube and Google services.
https://www.securitylab.ru/news/514798.php
same same every year: New Year Phone scam calls (expensive call backs to Ukraine)
SecurityLab, [14.12.20 16:05]
“Phone scammers are traditionally activated before the New Year, so it is very important to remind them once again about how to resist them.
A hundred, a thousand times to remind-never superfluous, if only people realized that this can happen to anyone, and could do the right thing in the event of such a call.
The regulator and banks should now do everything possible to protect people’s savings, which they often did not give easily, ” says Dmitry Skobelkin, Deputy Chairman of the Bank of Russia.
https://www.securitylab.ru/news/514802.php
especially: phone companies should not allow for expensive “hotline” numbers to be exploitable in that way (and maybe inform the user before calling “this phone call costs you 100€ per minute, does the user really want to proceed?”)
SecurityLab, [15.12.20 08:10]
In a statement filed with the U.S. Securities and Exchange Commission (SEC), software maker SolarWinds attempted to downplay the impact of a recent cyberattack on its systems.
https://www.securitylab.ru/news/514826.php
SecurityLab, [15.12.20 08:20]
Scammers send spam emails to users all over the world.
Information security experts fear that cybercriminals are testing a new malicious tool that is destined to become a serious threat to businesses and consumers in 2021.
Details:
Scammers send spam emails to users all over the world. Cybersecurity experts fear that cybercriminals are testing a new malicious tool that is destined to become a serious threat to businesses and consumers in 2021.
Experts from Vade Secure have recorded a sharp increase in the number of spam emails entering users ‘ mailboxes in Italy, France, Denmark and the United States. One company received about 300,000 spam emails in just one day, forcing it to disable the affected accounts and reset its credentials.
The wave of spam is not easy, because emails are placed in the Inbox folder, bypassing security levels. Vade Security suspects that criminals are using a tool called Email Appender, which was first discovered by Gemini Advisory in October 2020 and is sold on the darknet by subscription.
The Email Appender app allows cybercriminals to verify the credentials of a compromised account, configure a proxy server to avoid IP address detection, and create malicious emails. Using Email Appender assumes that you have a list of compromised credentials. By sorting through usernames and passwords, the program tries to log in to the email server, open the victim’s mailbox, and add your malicious email to it.
The tool has a user interface that allows a hacker to set up email by changing the display name of the sender’s address and creating an address for the response.
“The distribution of Email Appender on a subscription basis is a warning sign of what is to come in the field of cybercrime-as-a-service. Illegal services available on the darknet allow low-tech criminals to conduct successful ransomware attacks. If Email Appender and other similar tools continue to be successful, They can become very popular in the cybercrime community. In the past, we’ve seen hackers test their methods in the consumer market before moving into the business market. Consumers are sometimes less knowledgeable about security issues than businesses, which means that they are a relatively easy target and allow criminals to learn new methods, ” the experts explained.
https://www.securitylab.ru/news/514827.php
SecurityLab, [15.12.20 10:00]
The Federal Trade Commission (FTC) has announced an investigation into the privacy policies of some of the world’s largest technology companies and social media platforms.
https://www.securitylab.ru/news/514832.php
SecurityLab, [15.12.20 11:45]
The number of IoT devices and SCADA systems connected to the Network without appropriate security measures continues to increase, making critical devices vulnerable to potential attacks and hacking attempts.
A&O IT Group researchers reported that despite a number of high-profile attacks on SCADA systems, most devices and protocols do not have reliable protection.
https://www.securitylab.ru/news/514840.php
SecurityLab, [15.12.20 15:35]
Sophos and ReversingLabs announced the release of the SoReL-20M database, consisting of 20 million Windows Portable Executable files.
Of these, 10 million files are malware images.
https://www.securitylab.ru/news/514855.php
home office rule #1: don’t tweet during work hours:
SecurityLab, [15.12.20 19:45]
Data from social networks can become the basis for the beginning of an administrative investigation against organizations that violated the rules of work in the context of the coronavirus pandemic, said the head of the capital’s Glavcontrol Yevgeny Danchikov on the air of Channel One.
https://www.securitylab.ru/news/514860.php
SecurityLab, [16.12.20 08:10]
Security researchers at CybelAngel have discovered unprotected, sensitive patient data that is available to criminals for blackmail, fraud, or other malicious purposes.
More than 45 million medical images, as well as related identity data, were made available online due to unsecured technologies used to store, send, and receive medical data.
Details:
CybelAngel security researchers have discovered unsecured confidential patient data available to criminals for blackmail, fraud, or other malicious purposes. More than 45 million medical images, as well as related identity data, were made available Online due to insecure technologies used to store, send and receive medical data.
A six-month study conducted by CybelAngel specialists revealed a large-scale data leak. The aim of the study was to determine the level of security of network storage (NAS) and communication using the DICOM (Digital Imaging and COmmunications in Medicine) Protocol, a standard that medical institutions use for data transmission and processing.
The leaked data includes confidential medical records, x-ray CT scans, and MRI scans that anyone can access online.
CybelAngel experts scanned about 4.3 billion IP addresses and found 2,140 unsecured servers in 67 countries, including the United States, great Britain, France and Germany.
Medical images contained up to 200 lines of metadata per record, including the patient’s name, date of birth, and address, as well as their height, weight, diagnosis, and so on.
In most cases, access to this information did not require credentials, and on portals that provide registration, you could log in without filling in the login and password fields.
https://www.securitylab.ru/news/514863.php
SecurityLab, [16.12.20 08:15]
Thousands of organizations are at risk of cyberattacks due to the uncorrected URGENT/11 and CDPwn vulnerabilities affecting operating technology (OT) and IoT devices, respectively.
https://www.securitylab.ru/news/514864.php
advertisement:
SecurityLab, [16.12.20 09:35]
[Forwarded from Announcements of the best information security events]
[ Photo ]
How to build an effective security system?
Dozens of HackerU students in 2020 started their careers in the ranks of BlueTeam large companies
Start your journey and you are on the intensive ” CyberSecurity: Level 0»
Take part in conferences with an experienced information security specialist and get:
– Basic knowledge of the principles of building a corporate network infrastructure
– Experience in conducting attacks on the network layer and building a system to detect incidents
– Understanding how to apply your BlueTeam skills in your career
– Meet top security engineers and HackerU experts
– Bonuses for admission to the main program
The cost of participation until the new year is only 2300 RUB
SecurityLab, [16.12.20 10:00]
Microsoft and a number of other major antivirus software vendors have responded to a security researcher’s disclosure of a method to remotely disable their security solutions using Windows Safe Mode. Researcher Roberto Franceschetti (Roberto Franceschetti) published in his blog a video and PoC code for exploiting the vulnerability, which allows you to disable antivirus products from Microsoft (Windows Defender), Avast, Bitdefender, F-Secure and Kaspersky Lab»
https://www.securitylab.ru/news/514867.php
SecurityLab, [16.12.20 15:34]
Reports of problems with Telegram began to arrive at 15: 49 Moscow time. At 16: 18, the service recorded 23,000 error reports.
In 90% of cases, people can’t connect to Telegram.
The rest complain about the inability to send a message.
Most of the messenger users who left a complaint could not connect to the app or send a message to the other person.
The failure occurred on the territory of Russia, Ukraine, Kazakhstan, Italy, Spain, Great Britain and other countries.
By 16: 17 Moscow time, the number of complaints exceeded 17,000.
https://www.securitylab.ru/news/514885.php
SecurityLab, [16.12.20 15:45]
The manufacturer of tools for hacking mobile devices, the Israeli company Cellebrite, said that it is now possible to use its tools to hack the “Signal” application, which is considered protected from outside interference.
Cellebrite’s hacking tools are used by law enforcement and intelligence agencies around the world.
In addition , as recently revealed, Cellebrite’s customers also include several school districts in the United States.
The company has been repeatedly accused of selling surveillance technology to totalitarian regimes and countries found to be violating human rights.
After media reports that Cellebrite’s technology was used by Chinese authorities to track Hong Kong activists, the company promised not to sell its products to China again.
SecurityLab, [16.12.20 16:00]
The European Commission and the High Representative of the Union for Foreign Affairs and Security Policy have presented a new EU cybersecurity strategy.
The goal of this strategy is to increase Europe’s collective resilience to cyber threats and to ensure that all citizens and businesses can take full advantage of trustworthy and reliable services and digital tools.
This includes an ever-increasing number of connected and automated facilities in homes, offices, and factories.
SecurityLab, [16.12.20 20:05]
The Moscow Mayor’s Office has ordered for 76.8 million rubles the modernization of the “Moscow Assistant” system, with which you can now complain about parking violations.
https://www.securitylab.ru/news/514893.php
SecurityLab, [17.12.20 08:15]
A developer under the pseudonym ggerganov has published on GitHub a set of command-line software tools and a graphical user interface (GUI) for capturing and analyzing audio data.
The most interesting ones are keytap and keytap2.
https://www.securitylab.ru/news/514895.php
SecurityLab, [17.12.20 08:20]
A few years before the SolarWinds computer network hack, which compromised the networks of several federal government agencies, a well-known hacker tried to sell access to the company’s computers on underground forums.
https://www.securitylab.ru/news/514896.php
SecurityLab, [17.12.20 09:45]
Dutch authorities have found a hacker who hacked into a Twitter account belonging to US President Donald Trump, successfully matching the password “maga2020!”.
However, Victor Gevers ,who is not a cybercriminal but a security researcher, will not face any punishment, the BBC reports.
https://www.securitylab.ru/news/514898.php
SecurityLab, [17.12.20 11:55]
A group of cybercriminals used mobile emulators to simulate thousands of mobile devices, allowing them to steal millions of dollars in a matter of days.
https://www.securitylab.ru/news/514912.php
SecurityLab, [17.12.20 14:55]
Information security specialists continue to investigate the cyberattack on the internal network of SolarWinds, as a result of which a malicious update was introduced for its Orion software in order to infect the networks of government and commercial organizations using it.
https://www.securitylab.ru/news/514933.php
SecurityLab, [17.12.20 16:00]
The attorneys General of ten US states have filed a class-action lawsuit against Google, accusing it of violating antitrust laws regarding advertising on the Internet.
https://www.securitylab.ru/news/514940.php
SecurityLab, [17.12.20 19:45]
Twitch has announced a change in its policy on harassment and hate speech.
According to the new rules on the platform from January 22, it will be impossible to use the words “virgin” (virgin), “simp” (simp) and “incel” (incel) for insults, which are popular on Twitch.
https://www.securitylab.ru/news/514947.php
SecurityLab, [18.12.20 08:20]
A dangerous authentication bypass vulnerability (CVE-2020-28052) has been discovered in the popular open source cryptographic library Bouncy Castle. Its operation allows an attacker to gain access to the accounts of users or administrators.
https://www.securitylab.ru/news/514949.php
SecurityLab, [18.12.20 08:25]
Microsoft has discovered malware in its networks, adding to the list of companies affected by the hacking of the Texas software manufacturer SolarWinds.
https://www.securitylab.ru/news/514950.php
SecurityLab, [18.12.20 10:15]
Security researchers at Menlo Labs have reported an increase in the number of so-called drive-by attacks (downloading without the user’s knowledge) using a highly active structure, dubbed SocGholish for its extensive use of social engineering tools and techniques.
https://www.securitylab.ru/news/514954.php
SecurityLab, [18.12.20 10:30]
During the police operation, law enforcement officers managed to partially disrupt the work of the most popular trading platform, where cybercriminals sell and buy stolen data. This is evidenced by the reports of the resource administrators and sources who had access to it, according to the information security company Digital Shadows.
https://www.securitylab.ru/news/514955.php
SecurityLab, [18.12.20 15:05]
Hackers funded by a foreign government broke into the computer networks of the city of Austin, Texas. As reported by The Intercept, hackers carried out the attack in mid-October of this year and used the network as an infrastructure for carrying out cyber attacks. By hacking into Austin’s network, criminals could theoretically gain access to confidential information about the police, city government, and elections, and even to water and power networks.
https://www.securitylab.ru/news/514961.php
SecurityLab, [18.12.20 20:40]
In Russia, there will be a police unit that investigates crimes on the Internet. This was stated by Deputy Interior Minister Igor Zubov.
https://www.securitylab.ru/news/514967.php
SecurityLab, [19.12.20 09:10]
DJI — the world’s largest and most popular drone company-has been added to the U.S. Department of Commerce’s list of banned organizations. In other words, the Chinese company was considered a risk factor for US national security, and any US companies or businesses operating in the US are prohibited from exporting technology for DJI.
https://www.securitylab.ru/news/514985.php
SecurityLab, [19.12.20 10:35]
Microsoft has repeatedly spoken out against the use of passwords and now it seems that it intends to take the drastic step and completely abandon them in its products.
https://www.securitylab.ru/news/514986.php
SecurityLab, [20.12.20 07:55]
A large-scale hacker attack that affected US government departments affected at least 200 different structures around the world.
https://www.securitylab.ru/news/514992.php
SecurityLab, [20.12.20 08:20]
Microsoft is developing its own processors based on the ARM architecture to reduce dependence on Intel technologies.
https://www.securitylab.ru/news/514994.php
SecurityLab, [20.12.20 16:45]
“It is extremely important to take a step back and assess the significance of these attacks in their full context. This is not ” ordinary espionage” even in the digital age. On the contrary, it represents an act of recklessness that has created a serious technological vulnerability for the United States and the world. In fact, this is an attack not only on specific targets, but also on the trust and reliability of critical global infrastructure in order to promote the intelligence service of one country. While the latest attack appears to reflect a particular focus on the United States and many other democracies, it is also a powerful reminder that people in virtually every country are at risk and need protection regardless of the government under which they live,” Smith said.
https://www.securitylab.ru/news/514995.php
SecurityLab, [21.12.20 06:45]
The team of Joe Biden after his inauguration as president of the United States will consider different options for punishing Russia for a large-scale cyber attack on American government agencies, Reuters reports, citing sources. According to them, among the possible options may be both new economic sanctions and retaliatory hacker attacks on the Russian infrastructure.
An anonymous source told the agency that Washington intends to take actions that will result in serious economic, financial and technological losses for Moscow. At the same time, the United States intends to act in such a way as to avoid an escalation of the conflict between the countries
https://www.securitylab.ru/news/514998.php
SecurityLab, [21.12.20 08:25]
Apple has teamed up with other browser developers Google, Microsoft and Mozilla to block the root HTTPS certificate, which was used by the government of Kazakhstan to monitor its citizens. This was reported by the publication ZDNet.
https://www.securitylab.ru/news/514999.php
SecurityLab, [21.12.20 08:30]
Cybercriminals who hacked into Texas-based software manufacturer SolarWinds carried out a trial attack last year to test their capabilities. They started distributing third-party files from SolarWinds networks back in October 2019-five months before the victims downloaded malicious updates for the Orion platform. These files were sent out on October 10 and did not contain any backdoors.
https://www.securitylab.ru/news/515000.php
SecurityLab, [21.12.20 09:35]
A list of dozens of online stores hacked by a web-skimming group was accidentally leaked through the Remote access Trojan installer (RAT).
https://www.securitylab.ru/news/515002.php
SecurityLab, [21.12.20 10:30]
At least 36 journalists, producers, executive directors and TV presenters of the international TV company Al Jazeera, as well as journalists of the London-based TV channel Al Araby TV, were victims of hackers who broke into their iPhone through a zero-day vulnerability in the iOS app iMessage.
https://www.securitylab.ru/news/515003.php
SecurityLab, [21.12.20 13:45]
Employees of the IT department of the youth department of the Vyborg Diocese of the Russian Orthodox Church have developed the” first Orthodox antivirus software ” Labarum. The program is designed to protect religious users from scammers who collect donations under the guise of priests.
https://www.securitylab.ru/news/515005.php
SecurityLab, [21.12.20 19:40]
The Wall Street Journal analyzed that malicious code was installed in systems including Intel, NVidia, Cisco Systems, VMware, Belkin and Deloitte. The magazine claims that the perpetrators gained access to the California Department of Public Hospitals and Kent State University.
https://www.securitylab.ru/news/515022.php
SecurityLab, [22.12.20 08:20]
Analyzing the artifacts obtained during the investigation of the attack on the supply chain that began with SolarWinds, experts have identified another backdoor, apparently used by another cybercrime group.
https://www.securitylab.ru/news/515029.php
SecurityLab, [22.12.20 09:00]
Full disk encryption is one of the main methods of modern endpoint protection, allowing you to effectively protect confidential data from physical theft. To gain access to the encryption key, various attacks were used, based on sniffing the interface of the Trusted Platform Module (TPM) or direct Memory Access (DMA). But experts from F-Secure told about another method of attacks-sniffing the SPI interface of the TPM using publicly available tools. In addition, experts have released a tool that allows you to extract the BitLocker key from stolen SPI traffic.
https://www.securitylab.ru/news/515030.php
SecurityLab, [22.12.20 09:20]
Dozens of boxes of electronic mail of the Ministry of Finance of the USA have been compromised as a result of large-scale cyber attacks on U.S. government organizations. According to the Associated Press, the attackers broke into systems used by high-ranking officials of the Ministry of Finance. On Monday, December 21, US Senator from Oregon Ron Wyden provided new details about the attack.
https://www.securitylab.ru/news/515031.php
liked this article?
- only together we can create a truly free world
- plz support dwaves to keep it up & running!
- (yes the info on the internet is (mostly) free but beer is still not free (still have to work on that))
- really really hate advertisement
- contribute: whenever a solution was found, blog about it for others to find!
- talk about, recommend & link to this blog and articles
- thanks to all who contribute!