not sure if the news rang through… the Amazon Cloud (AWS) guy will be the new CEO of Amazon.
What cloud?
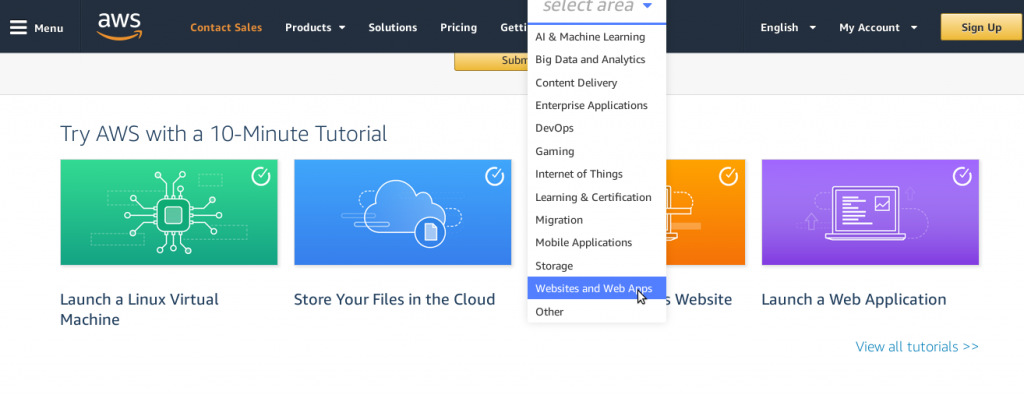
Amazon “cloud”
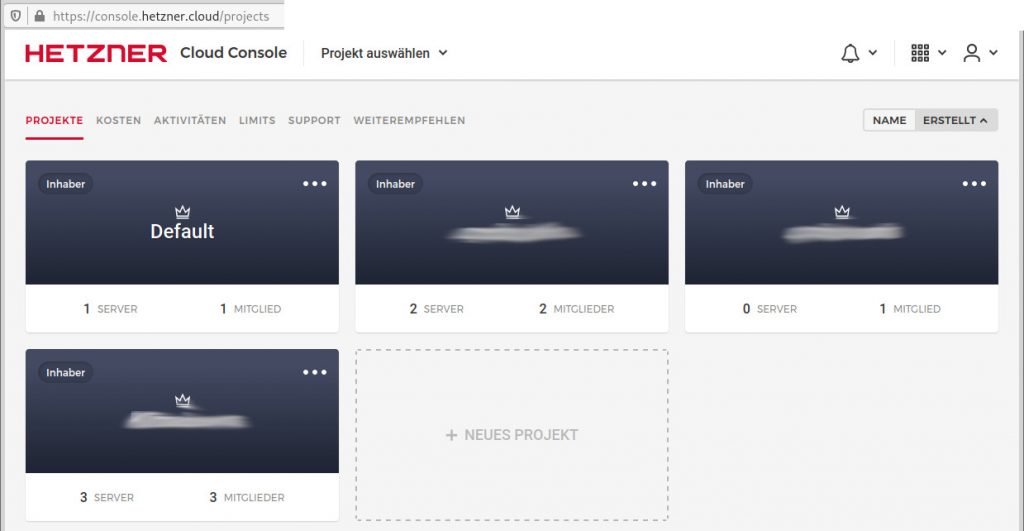
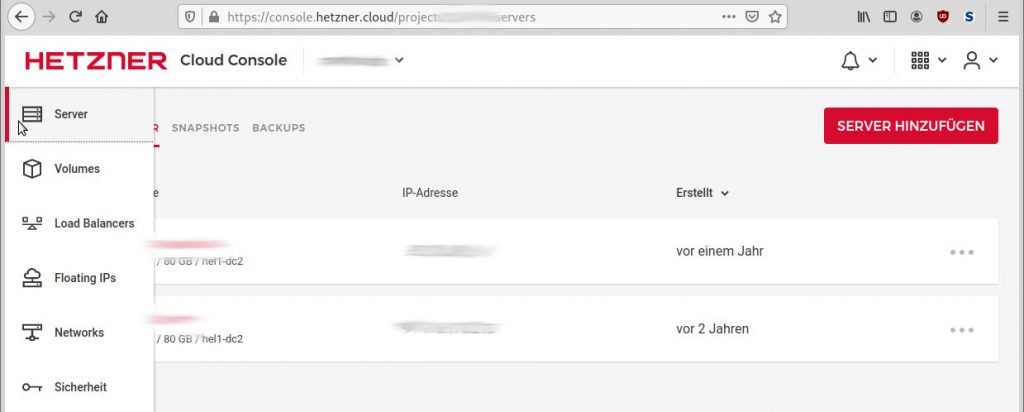
Hetzner “cloud”
cloud (centralized digital infrastructure) can be designed / implemented in different ways.
from: the user/admin will have to setup their own servers (VirtualPrivateServer) to “just upload your app to our dedicated php/java/python server”
Why cloud?
comment:
imho computer systems are ever developing, ever evolving, ever adapting… from centralized (mainframe)… to decentralized (personal computer) … to again centralized (cloud).
imho one can not say “this or that” is better.
it very much depends on the kind of service, if decentralized and disconnected makes sense…
or centralized and fully connected with all ports open makes sense…
the answer usually is something in between…
- a publicly available webserver of course needs to be directly accessible from the internet
- anything that needs to be centralized accessible from anywhere
- it is probably nonsense to completely re-create a company.net “in the cloud” (with every client and every server X-D)
- it might be a bad idea to move a software with highly sensitive data (e.g. company administration) to a cloud-datacenter
- telefone and fax machine “in the cloud” (as software on central server) https://www.sipgate.de/ has some appeal… if privacy is not a problem
- this is basically “infrastructure in software”… same as virtual machines… virtual nics… virtual phones… virtual fax machines… virtual harddisks… even virtual switches are now possible (connecting virtual servers) what else can be virtualized?
collecting data…
What makes Google so valuable?
The idea of people trading stocks, that data is the new gold.
Google, Microsoft & Amazon deal not only with physical but with virtual goods … data… BigData… and the more BigData (the more profiles with a lot of details) they can get their hands on… the more valuable is their BigData, that they will AI-analyze and re-sell to whoever wants it.
it-security nightmares: manipulated automatic updates & hacked update servers
security wise is everything that is directly connected to the internet at threat of being hacked or DDoSSed (denial of service).
so when a company moves all it’s digital assets to the cloud… it is basically completely dependent for that server to be available and the internet connection to work FAST.
so without fast internet… the cloud (cloud actually being just a new fancy word for datacenter that scales well) won’t start to fly.
just imagine a time… when IT security becomes so bad… that the company might decide to not go back to pen and paper, but to disconnect the company.net from the internet completely… (in order to keep functioning (and not ransomware sacked/disrupted/destroyed))… updates will have to be shipped via postal and CD (some companies still use CDs to send out updates).
it could happen.
if the user’s data is in the cloud… then the user will probably want to migrate it back to one’s own server and disconnect that one from the internet completely.
Also if the user is running a company that does cutting-edge research (military? biotech vaccine development?) from a privacy point of view… it would probably “pay off” to
- let the critical networks disconnected
- have all DVD/CD-Drives and USB-Ports blocked
- have a non-trivial BIOS password and BIOS settings that prevent booting from USB or other connected devices
- and also not let employees carry CDs or sticks or laptops or phones in and out of the facility
so automatic updates, yes or no?
the answer is not a simple yes or no, actually it should be like this:
- vendor of product or software:
- there needs to be a 100% secure way to authenticate updates
- a combination of
- PGP signed updates (like with PGP where a private key can be protected with a password… this password is super super sensitive, should have complexity to it and may only be known by the CEO of the company)
- the software vendor will announce the update on it’s official website & even call critical customers in advance to announce the update
- phone call could go like this: “hello can i speak to admin z from company x, please note: we will upload/ship out a new update tonight, please call me when the update has reached you, it will come with PGP checksum and we will send you sha512sum checksum in an separate mail, please verify and then install and then check the software according to your test-documentation.”
- a combination of
- there needs to be a 100% secure way to authenticate updates
- administrators of product or software:
- regular and timely updates are necessary to all devices that are directly connected to the internet (routers, modems, firewalls, switches, servers) or that receive & download messages (mails, telegram, whatsapp) from the internet (see Jeff Bezos IPhone hacked via Video.mp4 via WhatsApp)
- all this messaging needs to be done outside the company-net on a physically SEPARATE network (would not even trust a VLAN)
- usually with software-wise very minimalistic systems (routers, firewalls) that follow the KISS principle (“Keep it Simple”) are good to automatic updates
- in this field Google’s Android and Apple’s IPhone fails massively, the first being a highly modified GNU Linux, that often does not receive any updates at all, Apple should guarantee updates for their devices at least 10x years after release (anything else is massive waste of resources and pollutes the planet)
- automatic updates via internet is convenient but it comes at the downside of increased threat of it-security (hacked update servers with manipulated updates)
- in the case of Win 10, disabling updates is not even possible (catastrophic! so only way is to block all but some white-listed IPs via firewall)
- automatic or not the procedure should be like this:
- backup the system & all of it’s data to a USB harddisk, that then get’s PHYSICALLY disconnected (so a ransomewared-update has no access)
- download & store the update on the system
- disconnect all networking (LAN, in highly sensitive areas the device should not even have a wifi or UMTS modem installed)
- apply the update
- run all tests according to documentation (what worked before, should still work… in the best case, faster and more secure and with more functionality and hopefully minimal changes to the gui)
- observe any strange network traffic
- if all is well… reconnect the system to the LAN
- regular and timely updates are necessary to all devices that are directly connected to the internet (routers, modems, firewalls, switches, servers) or that receive & download messages (mails, telegram, whatsapp) from the internet (see Jeff Bezos IPhone hacked via Video.mp4 via WhatsApp)
Science Fiction? it happened to Lockheed Martin and the F-35…
SecurityLab, [15.11.20 08:24]
“The cost of the program to develop a modern f-35 fighter jet has increased significantly after the PRC compromised the software manufacturer in the Lockheed Martin supply chain, which led to the need to rewrite a potentially vulnerable system from scratch.
This was stated by a specialist at the Center for strategic and international studies, James Lewis, during a meeting on cyber defense of the British army.
According to Lewis, China compromised the systems of a subcontractor involved in the development of the F-35 and allegedly infected software designed for the fighter.
The specialist did not specify what kind of software was in question, and whether it was possible to prevent infection.
“Lockheed Martin has done an excellent job of protecting its systems [ … ], but going lower down the chain, not everyone provides the level of security you need.
So this is an allegation-through a subcontractor, China was able to access [the systems].
We don’t know what they could have done, the vulnerability was closed, and the software was mostly rewritten from scratch,” the Register quoted Lewis as saying.
In the past, Lewis has referred to this incident as a rumor, partly explaining the high cost of the F-35.
Apparently, this attack is not related to the 2017 incident, when attackers penetrated the computer network of the US air force and stole materials related to the F-35, including several gigabytes of data related to the design and electronic systems of the fighter.”
https://www.securitylab.ru/news/514065.php
yes… Lockheed Martin is “not to blame” it (probably) was a evil software update from hacked SolarWinds.
“The hack was apparently orchestrated via a malicious software update from SolarWinds Inc., a Texas-based network management company.
Defense contractor Booz Allen Hamilton and Lockheed Martin, as well as the U.S. Secret Service, National Security Agency, Defense Department, and Federal Reserve, all use SolarWinds products.” src: https://www.nationalreview.com/news/russian-intelligence-suspected-in-cyberattack-on-federal-agencies/
Worst-Case-Scenario: compromised Update-Servers
SecurityLab, [14.12.20 08:05]
Hackers funded by a foreign government broke into the computer networks of the American software manufacturer SolarWinds and implemented a malicious update for its Orion software in order to infect the networks of government and commercial organizations using it.
This was announced on Sunday, December 13, by the information security company FireEye.
https://www.securitylab.ru/news/514774.php
of course with critical cutting-edge research like this… not only needs it to be completely offline… then even a faulty update would not have been able to “call home” (but ransomware would still encrypt-destroy all data… but then there are (of course) still disconnected backups ey?).
With research as critical as this… of course the secret services also have to help protecting this critical research from
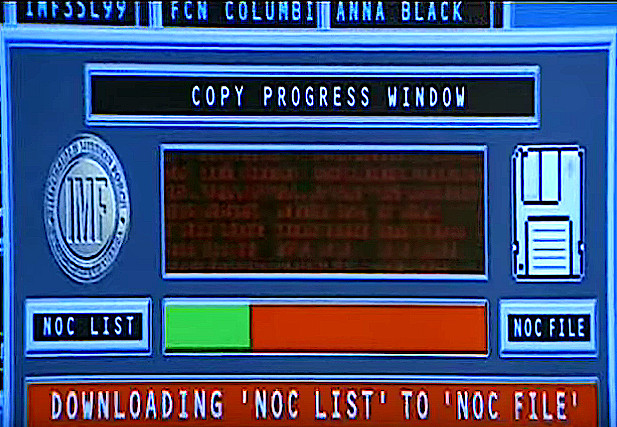
“Tom Cruises coming down per rope from the ceiling with an USB stick” (or even worse… an device-with-antenna that establishes a link to the outside… aka a backdoor… but then it is probably a high-security emp-proof datacenter with double-and-triple-shielding of all sorts of frequencies).
and some data should not exist in the first place… like that NOC list.
of course…
sharing resources makes sense.
For big companies that need massive computational resources to pay rent in a shared (with other companies) datacenter – such as AWS makes sense – especially if the demand needs to scale well.
(high demand = more resources = pay more, low demand = low resource use = pay less)
The probably only thing that AWS does maybe better than other datacenter-VPS-service providers is the scaling.
resume:
if big companies with cutting edge hight-tech research are having all their sensitive data stored “in the cloud”, then they might as well release all their results and patents (as Tesla does) as “Open Source”! 🙂
example: mp3 patent… yes, a hand full of top-notch scientists developed this codec… and instead of releasing it as “Open Source”, a hacker stole it and released it to the public and users and vendors have been using it in more or less legally authorized ways.
“On 7 July 1994, the Fraunhofer Society released the first software MP3 encoder, called l3enc.[57] The filename extension .mp3 was chosen by the Fraunhofer team on 14 July 1995 (previously, the files had been named .bit).[1] With the first real-time software MP3 player WinPlay3 (released 9 September 1995) many people were able to encode and play back MP3 files on their PCs. Because of the relatively small hard drives of the era (≈500–1000 MB) lossy compression was essential to store multiple albums’ worth of music on a home computer as full recordings (as opposed to MIDI notation, or tracker files which combined notation with short recordings of instruments playing single notes). As sound scholar Jonathan Sterne notes, “An Australian hacker acquired l3enc using a stolen credit card. The hacker then reverse-engineered the software, wrote a new user interface, and redistributed it for free, naming it “thank you Fraunhofer””.[58]
Fraunhofer example implementation
A hacker named SoloH discovered the source code of the “dist10” MPEG reference implementation shortly after the release on the servers of the University of Erlangen. He developed a higher-quality version and spread it on the internet. This code started the widespread CD ripping and digital music distribution as MP3 over the internet.[59][60][61][62]” (src)
This was a very “disruptive” moment for the music industry (Sony, EMP & Co).
Nowadays… nobody really makes “a fuss” out of it. (there have been quiet many such leaks in the past)
The ability to compress audio in MP3, OGG and AAC is considered a “common good”, the world has become for all (except the music industry) with mp3.
Links:
https://www.ionos.com/digitalguide/server/know-how/iaas-infrastructure-as-a-service/
liked this article?
- only together we can create a truly free world
- plz support dwaves to keep it up & running!
- (yes the info on the internet is (mostly) free but beer is still not free (still have to work on that))
- really really hate advertisement
- contribute: whenever a solution was found, blog about it for others to find!
- talk about, recommend & link to this blog and articles
- thanks to all who contribute!