lately this blog gets bombarded with queries like these: which decoded are Korean SPAM? which translates as: iptables / firewalld seem not to work and have to really really figure out why. until then this is a little workaround, it […]
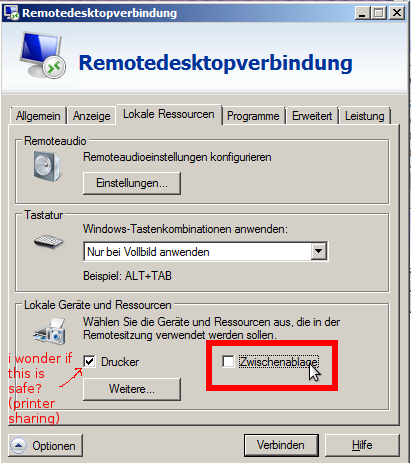
CheckPoint Security found security problems in OpenSource and closed source rdp clients/servers – the product vendors including MS have been informed and everybody except MS will update their products. X-D a hacked rdp server can “attack” the client – in […]
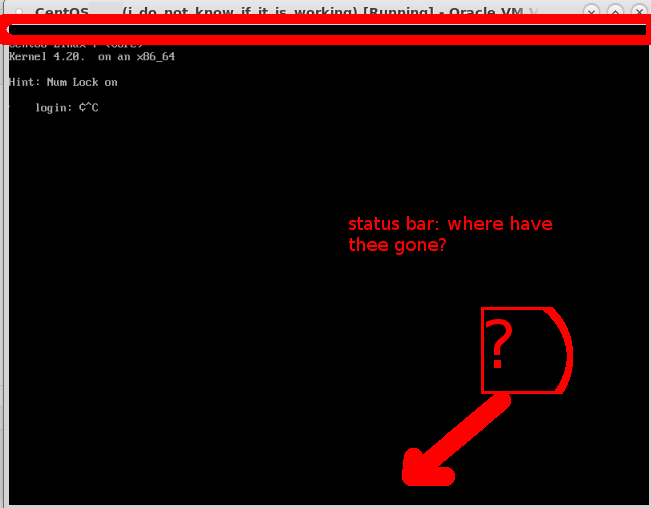
Short stoy: AltGr (HostKey) + C will quit “seamless (no menues) mode” really like the cross-os capabilties of virtualbox (possible to move vms between GNU Linux and Windows servers) and think it has great potential, what is not so great […]
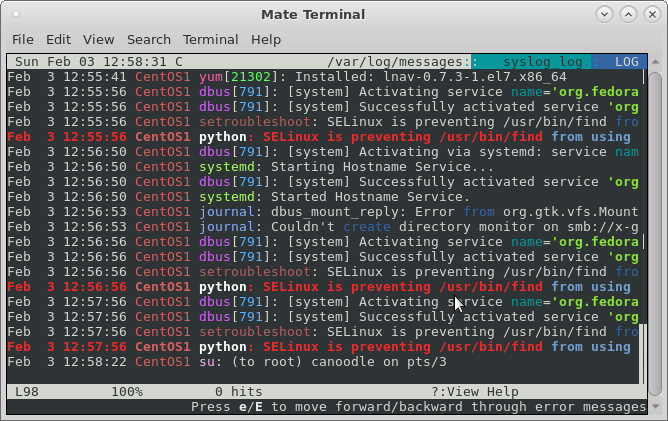
CentOS8: ccze author not willing to maintain ccze. no ccze and not even lnav available. how to monitor all logs… https://dwaves.de/2017/06/15/linux-monitor-all-logs-in-real-time-d-follow-all-show-changes-to-log-files-under-varlog/ as i was wondering what combination of less -R with or without ccze would allow me to view log […]
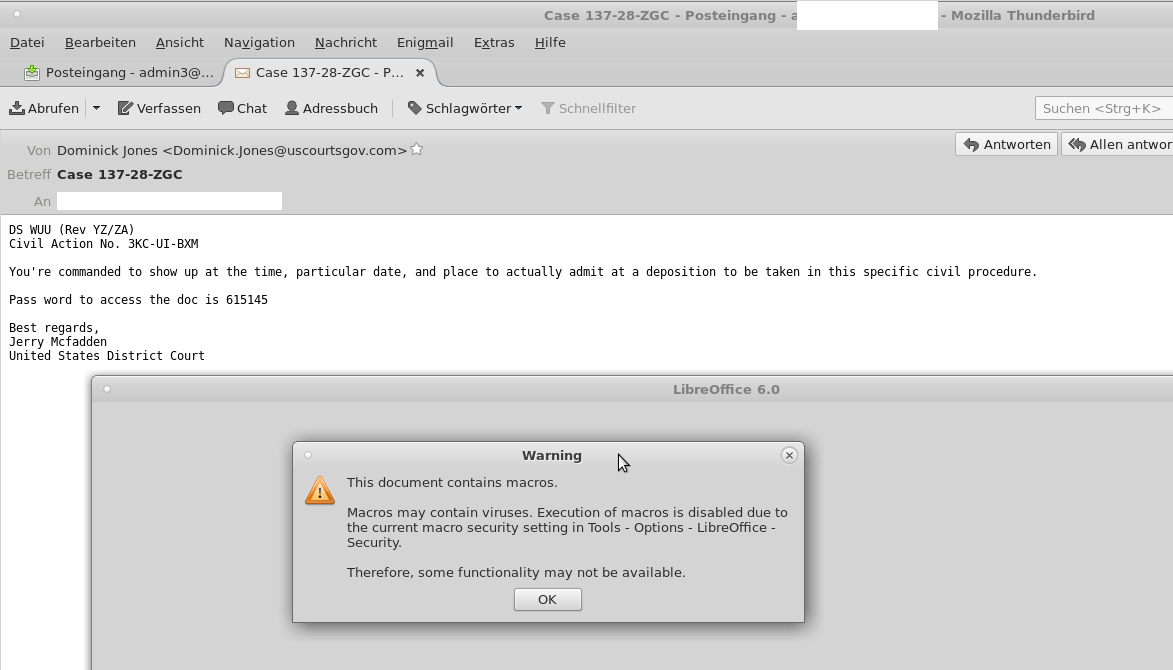
this mail looks so convincing… i bet it gets a high “return” rate. mail is fundamentally broken system – that’s why Google keeps cranking up requirements to send mail to Google and one day it will probably deny ALL […]
FTP->SFTP now! first things first: ABANDON FTP IT IS INSECURE AND WILL TRANSFER YOUR PASSWORDS AND FILES IN CLEAR TEXT OVER THE INTERNET! MOVE TO SFTP (FTP OVER SSH) with strong passwords! if you run your own server – disable […]
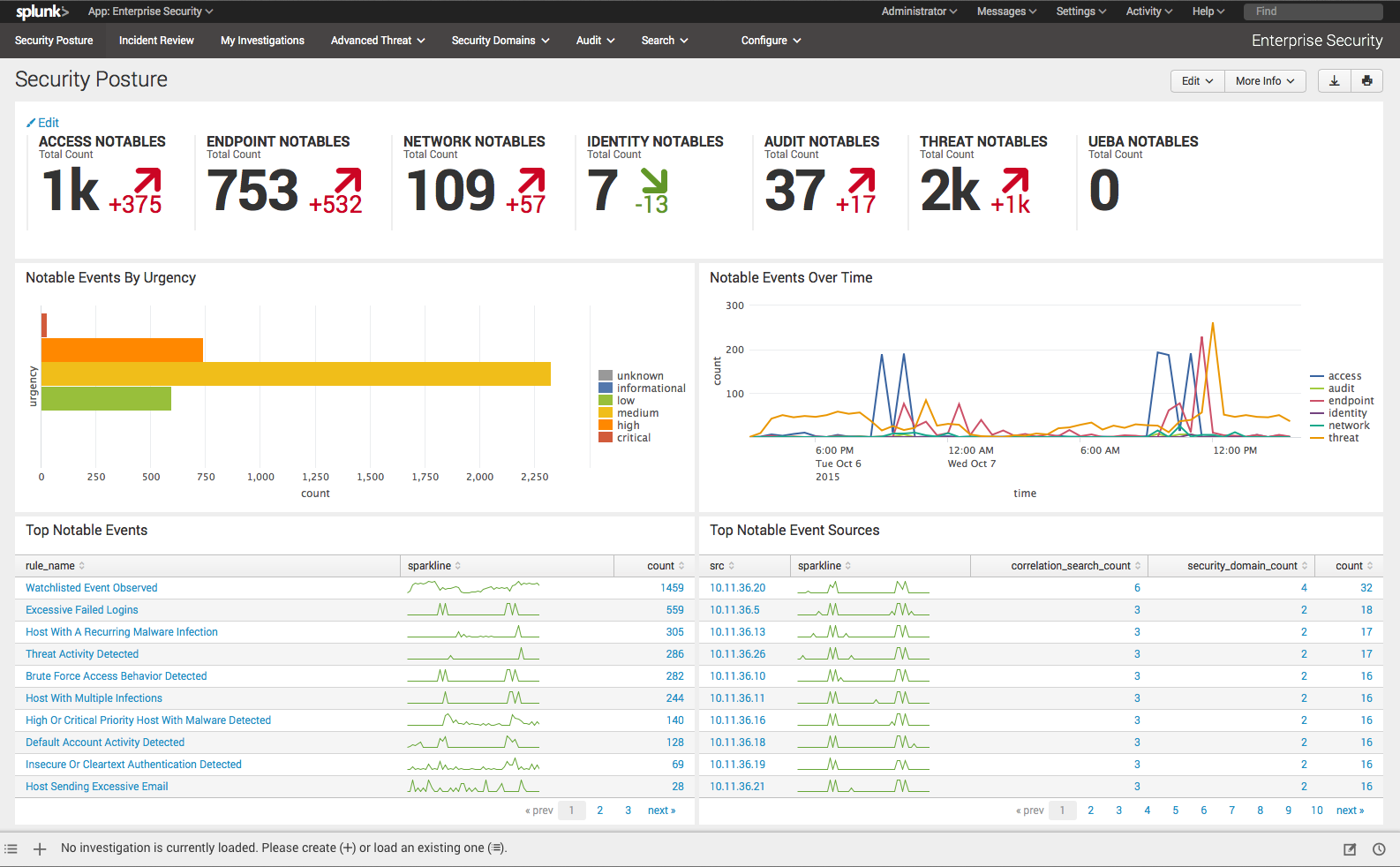
with security there is no “done” it can be clearly seen that: the amounts of it-security problems is increasing of course there is no 100% security with state-actors playing “hot” “cold war” in cyberspace private-spy-companies developing exploits that then leak […]
da! schon wieder! es wird nur kurz “Angeklingelt” und gehofft dass das Opfer zurückruft. Anruf um 14:08 von +79 40 76 9 30 53 – allein das ANNEHMEN des ANRUFS oder das ZURÜCKRUFEN kann 100€ kosten! HIER wären die NSA […]
https://youtu.be/70Blz9hyAz8 https://devtube.dev-wiki.de/videos/watch/f979469f-5fd1-4c40-a8c4-706c20c001f7 While “backdoors” in hardware sound like a good idea… you don’t know how hackers are using it to sabotage infrastructure or extort bitcoins of another country’s companies… see “backdoor in cisco router“. IT IS F**** DANGEROUS! ESPECIALLY if […]
it kills the (probably not existing) virus scanner “An associated security bypass is done as well — it will scam for processes running in memory that are associated with Linux-based anti-virus products. If such are found they are going to […]
checkout the space weather today 🙂 “Schwabe cycle, is a nearly periodic 11-year change in the Sun’s activity” (src) but the sun’s particles ALSO shield from even more outer space radiation BUT the sun is ALSO protecting Earth & Mars […]
please see: https://dwaves.de/2019/01/08/fail2ban-manually-ban-and-unban-ip/
Was in USA funktioniert ist bald auch bei uns. Kriminelle erbeuten/kaufen detailierte persönliche Informationen (Geburtsdatum, Mail-Passwörter, Kreditkartennummern) online und rufen das Opfer mit einer GEFÄLSCHTEN Telefonnummer an, die GENAU so aussieht wie die einer Bank und erzählen, “es hätte seltsame […]
At least seven soldiers were injured in Saturday’s incident [Xinhua via AP] “A little-known group called the National Movement of Soldiers in T-shirts claimed responsibility for the attack. In a series of posts on social media, the group said […]
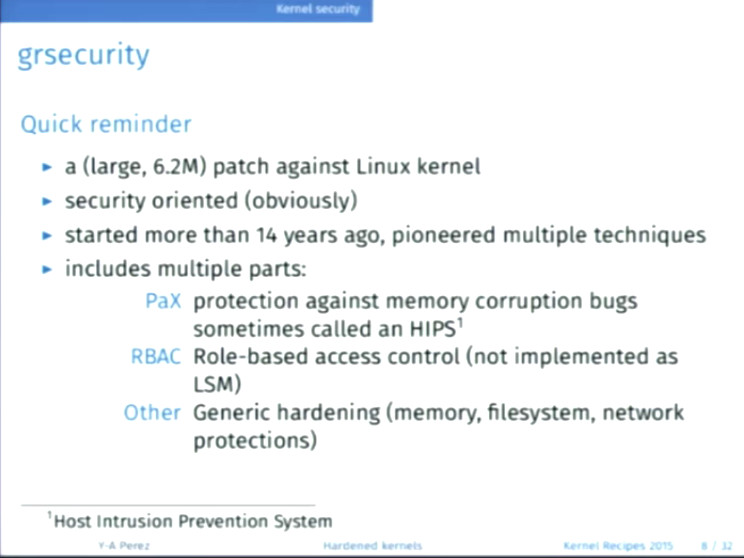
first of: A DRASTIC VIDEO: JM Porup reports for Ars Technica: The Linux kernel today faces an unprecedented safety crisis. Much like when Ralph Nader famously told the American public that their cars were “unsafe at any speed” back in […]
Elon Musk: 2018: “Ai is far more dangerous than nukes” and should be regulated. “We have to ensure that the advent of digital super intelligence is symbiotic with mankind” Update: Made in Israel killer Drone! killing people has never been […]
Bitcoin Gold hacked – 18 Million USD stolen https://www.heise.de/newsticker/meldung/Ende-der-Grafikkarten-Aera-8000-ASIC-Miner-fuer-Zcash-Bitcoin-Gold-Co-4091821.html https://www.heise.de/ct/ausgabe/2018-14-Wie-51-Prozent-Angriffe-Bitcoin-Co-bedrohen-4085333.html
“Thank you” i feel much safer now, that you know EVERYTHING about me, you, everybody. it is about influencing and directing the masses like a herd of cattle. https://en.wikipedia.org/wiki/Room_641A Room 641A is a telecommunication interception facility in the SBC Communications […]
sometimes if you know how to r-click… you are allready a HACKER! “Last month’s story about organizations exposing passwords and other sensitive data via collaborative online spaces at Trello.com only scratched the surface of the problem. A deeper dive suggests […]
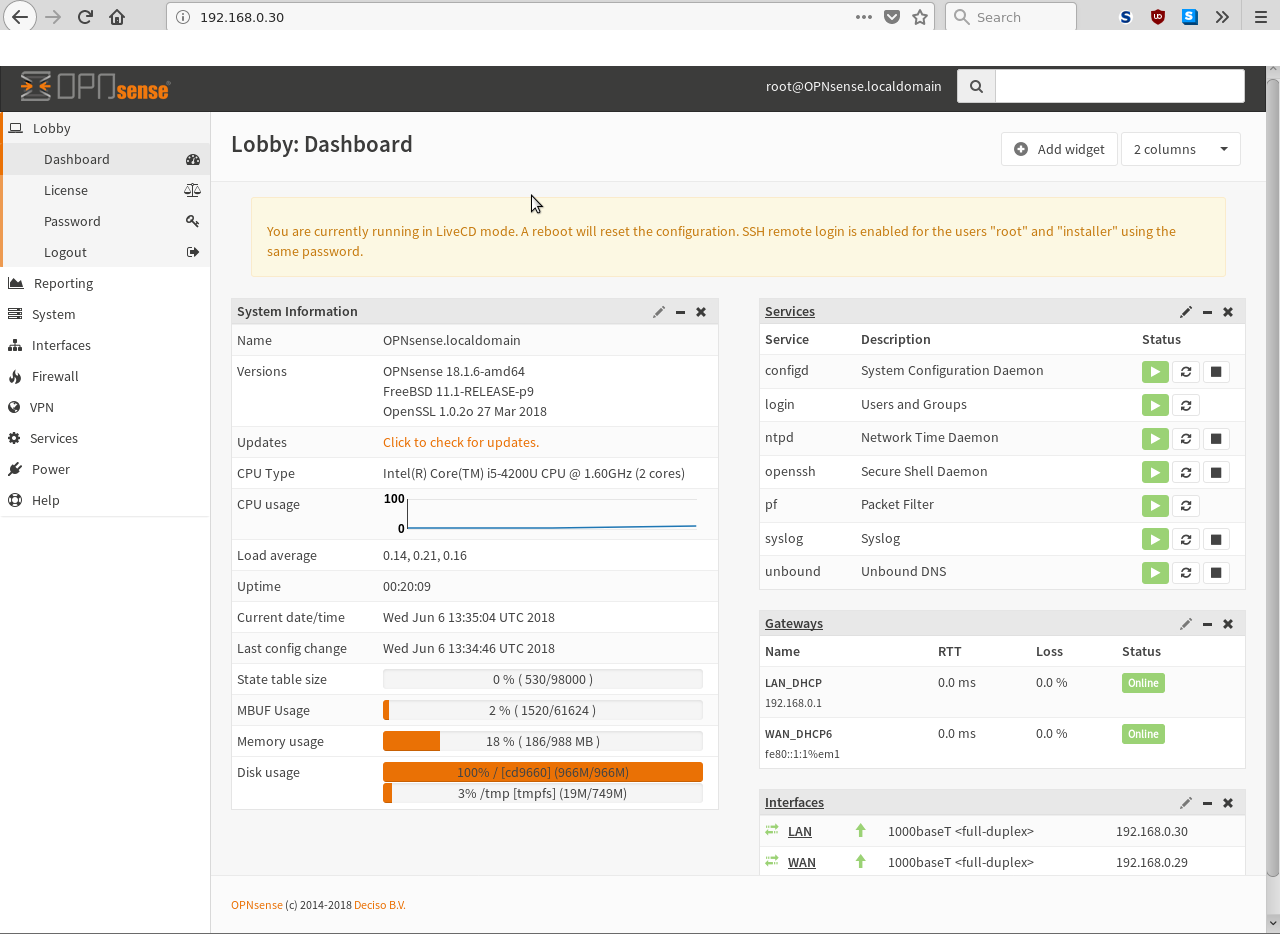
basically the advanced version of PiHole. WARNING! THIS IS not a complete OPNSense / PFSense tutorial it is rather just to get started. right now, one is (still) using iptables without any gui. there seems to be a lot of […]
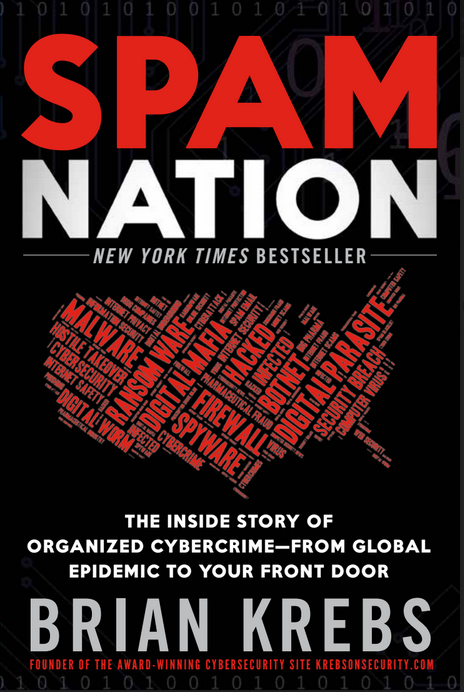
as you can see here every single day – spammers attach password encrypted word.doc to a mail and try to infect systems to extract ransome. This raises the question: How to handle this threat? Virus scanners are not enough anymore. […]
Update: 2024 unfortunately also some ARM CPUs are affected by Spectre v1 and v2. Update: 2020.03 “The newly developed Rowhammer- attack TRRespass can crack the RAM-a security mechanism by many DDR4-DRAM-modules as well as LPDDR4 Chips. Until now, these were […]
not a day passes by that spammers/crackers/evil money addicted people try to infect your system with an word.doc attached to some mail from “police” “government” “paypal” “facebook” “google” “apple” or whatever. here is the latest scam that: a password encrypted […]
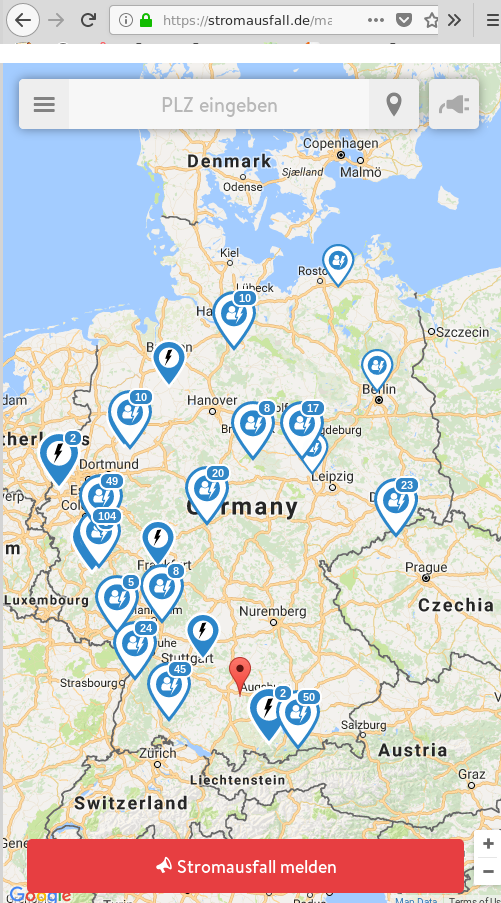
Effizienz ist nicht alles – weiß Bernard Lietaer – wer sich auf eine Monokultur verlässt – ist verlassen. Nach einem Stromausfall oder Hacker-Angriff können Internet basierte Kommunikationsdienste lahmgelegt sein. Aus eigener Erfahrung: An Weihnachten 2017 wurde ein Baum vom Biber […]
monitor (andoird) devices with bpf: https://www.socallinuxexpo.org/sites/default/files/presentations/bcc-scale.pdf so guess “monitoring” is about two things: availability and performance: detect performance bottlenecks get informed if parts (harddisks) / servers have failed / are about to fail security: detect, report and (if possible) automatically […]
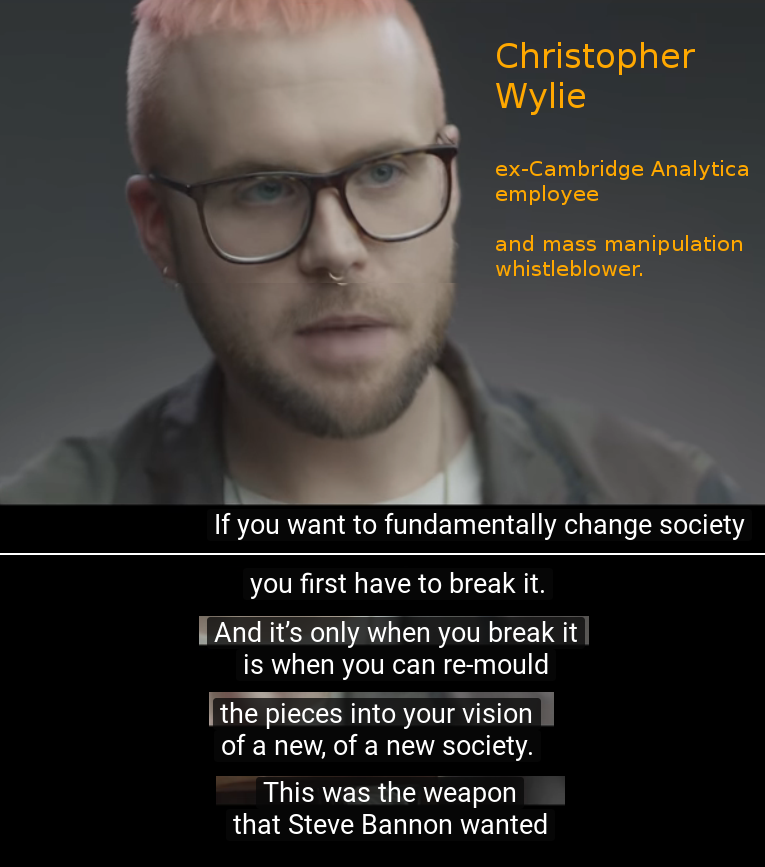
Is social media, facebook, twitter endangering democracy? Well if you bring in rich individuals such as Mr Mercer with the need to manipulate society: YES. “Cambridge Analytica is a Full Service Propaganda Machine” “In 2016 CA worked for Donald Trump’s […]
Update: 2018.04 the cameras could not see the lane’s properly because the lane paint has worn off… what algorithm is going to fix this? believe me or not – doing self driving car’s is almost as complex and difficult to […]
Here are 13 cryptocurrency breaches which took place from July 2017 to February 2018: 1: July 4th, 2017: Bithumb hacked and 1.2 billion South Korean Won stolen. 2: July 17th, 2017: CoinDash hacked and $7 million in Ethereum stolen. 3: July 24th, 2017: Veritaseum hacked and $8.4 […]
Update: 2020-05 Munich commits to “Public Money? Public Code!” The new coalition agreement in Munich commits to the principle of “Public Money? Public Code!”. The FSFE welcomes this decision by the new government and will closely monitor the progress of […]
mail is still THE most used communication service (even before WhatsApp), spam is a massive problem renders mail hard to use. Every once and a while websites and databases get hacked and spammers update their databases. Is your mail address […]