“Thank you” i feel much safer now, that you know EVERYTHING about me, you, everybody.
it is about influencing and directing the masses like a herd of cattle.
https://en.wikipedia.org/wiki/Room_641A
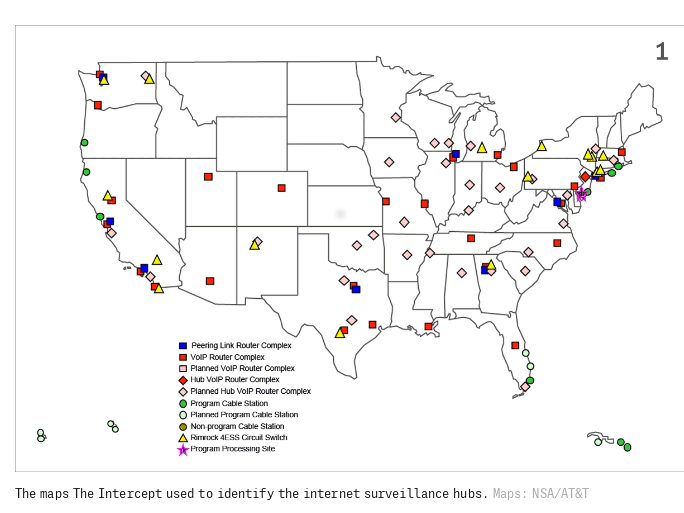
Room 641A is a telecommunication interception facility in the SBC Communications building at 611 Folsom Street, San Francisco, three floors of which were occupied by AT&T before SBC purchased AT&T.[1] operated by AT&T for the U.S. National Security Agency that commenced operations in 2003 and was exposed in 2006.[1][2]
“Because of AT&T’s position as one of the U.S.’s leading telecommunications companies, it has a large network that is frequently used by other providers to transport their customers’ data. Companies that “peer” with AT&T include the American telecommunications giants Sprint, Cogent Communications, and Level 3, as well as foreign companies such as Sweden’s Telia, India’s Tata Communications, Italy’s Telecom Italia, and Germany’s Deutsche Telekom.” (src: TheIntercept)
Devices used:
Narus STA 6400
People involved:
In 1997, Ori Cohen, Vice President of Business and Technology Development for VDONet, founded Narus with Stas Khirman in Israel.[1]
http://coat.ncf.ca/P4C/66/spy.pdf
mirror: israel_spy_companies.pdf 
http://www.svod.org/stas-khirman/
Presently, they are employed with Deutsche Telekom AG and are not members of Narus’ Executive Team.[2][3][4] In 2010, Narus became a subsidiary of Boeing, located in Sunnyvale, California.[5][6] In 2014, Narus was sold to Symantec.[7]
In 2004, Narus employed former Deputy Director of the National Security Agency, William Crowell as a director. From the Press Release announcing this:[8]
Crowell is an independent security consultant and holds several board positions with a variety of technology and technology-based security companies.
Since 11 September 2001, Crowell served on the Defense Advanced Research Projects Agency (DARPA) Task Force on Terrorism and Deterrence, the National Research Council Committee on Science and Technology for Countering Terrorism and the Markle Foundation Task Force on National Security in the Information Age.
NarusInsight
Narus is noted for having created NarusInsight, a supercomputer system, whose installation in AT&T‘s San Francisco Internet backbone gave rise to a 2006 class action lawsuit by the Electronic Frontier Foundation against AT&T, Hepting v. AT&T.[11]
System specification and capabilities
Some features of NarusInsight include:[12]
- Scalability to support surveillance of large, complex IP networks (such as the Internet).
- High-speed packet processing performance, which enables it to sift through the vast quantities of information that travel over the Internet.
- Normalization, correlation, aggregation and analysis provide a model of user, element, protocol, application and network behaviors, in real-time. That is it can track individual users, monitor which applications they are using (e.g., web browsers, instant messaging applications, e-mail) and what they are doing with those applications (e.g., which web sites they have visited, what they have written in their emails/IM conversations), and see how users’ activities are connected to each other (e.g., compiling lists of people who visit a certain type of web site or use certain words or phrases in their e-mail messages.
- High reliability from data collection to data processing and analysis.
- NarusInsight’s functionality can be configured to feed a particular activity or IP service such as security lawful intercept or even Skype detection and blocking.
- Compliance with CALEA and ETSI.
- Certified by Telecommunication Engineering Center (TEC) in India for lawful intercept and monitoring systems for ISPs.
The intercepted data flows into NarusInsight Intercept Suite.[13] This data is stored and analyzed for surveillance and forensic analysis.
Other capabilities include playback of streaming media (i.e., VoIP), rendering of web pages, examination of e-mail and the ability to analyze the payload/attachments of e-mail or file transfer protocols. Narus partner products, such as Pen-Link, offer the ability to quickly analyze information collected by the Directed Analysis or Lawful Intercept modules.
A single NarusInsight machine can monitor traffic equal to the maximum capacity (10 Gbit/s) of around 39,000 256k DSL lines or 195,000 56k telephone modems. But, in practical terms, since individual internet connections are not continually filled to capacity, the 10 Gbit/s capacity of one NarusInsight installation enables it to monitor the combined traffic of several million broadband users.
According to a year 2007 company press release, the latest version of NarusInsight Intercept Suite (NIS) is “the industry’s only network traffic intelligence system that supports real-time precision targeting, capturing and reconstruction of webmail traffic… including Google Gmail, MSN Hotmail and Yahoo! Mail“.[14] However, currently most webmail traffic can be HTTPS encrypted, so the content of messages can only be monitored with the consent of service providers.
NarusInsight can also perform semantic analysis of the same traffic as it is happening, in other words analyze the content, meaning, structure and significance of traffic in real time. The exact use of this data is not fully documented, as the public is not authorized to see what types of activities and ideas are being monitored. Ed Snowden‘s June 2013 releases about PRISM (surveillance program) have made clear however that Narus has played a central role.
https://en.wikipedia.org/wiki/Narus_(company)
Thanks!
to Snowden to provide proof for facts, that seem unlawful and unbelievable.
- Let’s Encrypt is super easy to use with Caddy-Webserver, all other webserver producers (apache, nginx) should support Let’s Encrypt built-in (soon also on this server).
- free-hardware with free-drivers – we won’t give up!
Links:
https://theintercept.com/2018/06/25/att-internet-nsa-spy-hubs/
https://electrospaces.blogspot.com/2015/08/fairview-collecting-foreign.html
https://www.eff.org/nsa-spying/timeline
liked this article?
- only together we can create a truly free world
- plz support dwaves to keep it up & running!
- (yes the info on the internet is (mostly) free but beer is still not free (still have to work on that))
- really really hate advertisement
- contribute: whenever a solution was found, blog about it for others to find!
- talk about, recommend & link to this blog and articles
- thanks to all who contribute!



