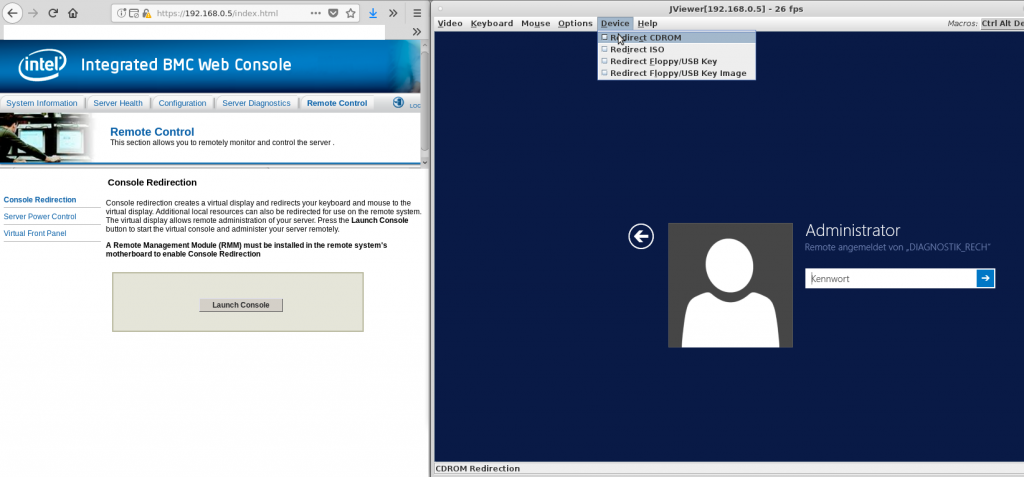
Intel BMC Java JViewer KVM Remote Control with Linux and Intel Mainboard S2600CWR
Hackers think so too.
Because a firmware is sometimes hard to update.
BIOS-UEFI updates need to be as easy to install than OS updates.
There are even parts of Intel ME that can not be updated at all (yet) because they are encrypted & signed and the system won’t start if they are missing (security by obscurity).
another dramatic way to put it:
“The biggest network security threat today is a remote code execution exploit for Intel’s Management Engine.”
“Every computer with an Intel chipset produced in the last decade would be vulnerable to this exploit, and RCE would give an attacker full control over every aspect of a system.
If you want a metaphor, we are dinosaurs and an Intel ME exploit is an asteroid hurtling towards the Yucatán peninsula.” (https://hackaday.com/tag/intel-me/)
solutions anyone?
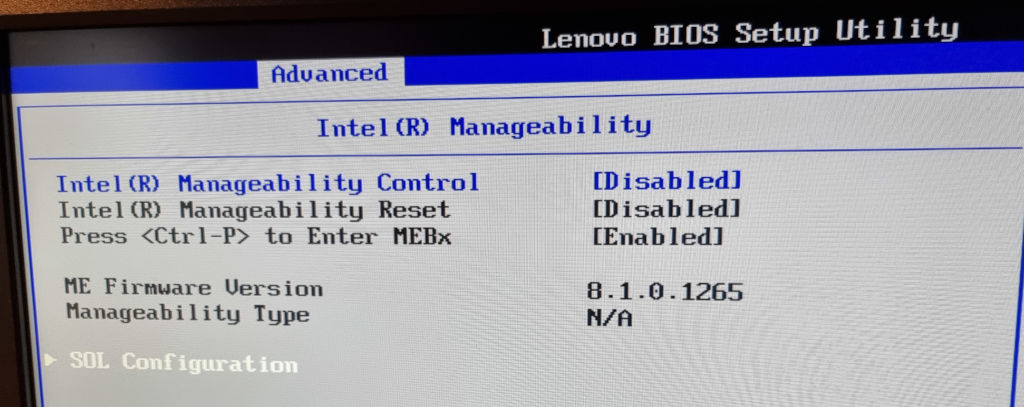
- try turning AMT BMC Intel ME off in the bios
- on some systems BMC can be disabled with a jumper on the motherboard
- Flash GNU Linux to the BIOS! (CoreBoot, LibreBoot with the Lenovo x60s no problem, with newer notebooks / PCs probably more effort)
- “Just use AMD”, yes better but according to this video only a partial solution?
intel needs to work with it’s damaged customers to fix this mess
Or be sued for every hack and every ransomware attack and every downtime and every destroyed motherboard.
seriously.
open source backdoors instead of closed source backdoors!
ok ideally no backdoors at all?
links:
https://www.rapid7.com/blog/post/2013/07/02/a-penetration-testers-guide-to-ipmi/
liked this article?
- only together we can create a truly free world
- plz support dwaves to keep it up & running!
- (yes the info on the internet is (mostly) free but beer is still not free (still have to work on that))
- really really hate advertisement
- contribute: whenever a solution was found, blog about it for others to find!
- talk about, recommend & link to this blog and articles
- thanks to all who contribute!


“The biggest network security threat today is a remote code execution exploit for Intel’s Management Engine.”
“Every computer with an Intel chipset produced in the last decade would be vulnerable to this exploit, and RCE would give an attacker full control over every aspect of a system.
If you want a metaphor, we are dinosaurs and an Intel ME exploit is an asteroid hurtling towards the Yucatán peninsula.” (https://hackaday.com/tag/intel-me/)