SecurityLab, [21.04.20 15:35]
Bitdefender experts have reported a malicious campaign against oil and gas companies.
Attackers use targeted phishing and send emails to victims on behalf of logistics companies and engineering contractors.
The goal of the campaign is to infect target systems with the Agent Tesla infostiler. ( a powerful password stealing program)
Infostiler Agent Tesla attacks the oil and gas industry (https://www.securitylab.ru/news/506931.php)
SecurityLab, [21.04.20 15:55]
Scientists and researchers from more than 25 countries have published an open letter calling on governments not to misuse COVID-19 infection tracking apps to track citizens.
backup / mirror of the open letter here: Joint Statement against Contact Tracing Apps Date 19th April 2020.pdf
Scientists have proposed to decentralize data on infected COVID-19 (https://www.securitylab.ru/news/506932.php)
SecurityLab, [22.04.20 08: 00]
A specialist of the Agile Information Security company, Pedro Ribeiro, revealed details about four uncorrected vulnerabilities in IBM data Risk Manager (IDRM) enterprise-class SOFTWARE designed to analyze an organization’s assets and related risks.
The researcher decided to make public information about vulnerabilities and PoC exploits for them after IBM did not accept his report, submitted by all the rules through CERT/CC.
PoC exploits have been published for four uncorrected vulnerabilities in IBM IDRM (https://www.securitylab.ru/news/506935.php)
SecurityLab, [22.04.20 08: 15]
The French government has asked Apple to remove some technical restrictions that prevent the development of the “StopCovid mobile app” for tracking the spread of coronavirus infection (COVID-19).
France will not be able to launch the StopCovid app without Apple’s help (https://www.securitylab.ru/news/506936.php)
“Apple’s iPhones normally block access to Bluetooth unless the user is actively running an app. French officials want Apple to change the settings to let their app access Bluetooth in the background, so it is always on. So far, they say, Apple has refused.
“Apple could have helped us make the application work even better on the iPhone. They have not wished to do so,” France’s minister for digital technology, Cedric O, told BFM Business TV.
“I regret this, given that we are in a period where everyone is mobilised to fight against the epidemic, and given that a large company that is doing so well economically is not helping out a government in this crisis.”
“We will remember that when time comes,” the minister added.
A spokesman for Apple in France declined to comment.
The issue of Bluetooth access on iPhones is one of several security-related questions that have arisen as countries try to roll out smartphone apps to fight the coronavirus.
France, along with some other countries, wants to keep contact data in a central database, arguing this would make it easier for the authorities to track suspected coronavirus cases.” (src)
SecurityLab, [22.04.20 09:10]
Rack911 Labs specialists demonstrated how using symbolic links (directory junction on Windows and symlink on macOS and Linux) can turn almost any antivirus solution into a tool for self-destruction.
A method for turning antivirus software into a tool for self-destruction is presented (https://www.securitylab.ru/news/506939.php)
SecurityLab, [22.04.20 10: 15]
OpenSSL developers have released a security update for the OpenSSL cryptographic library that addresses a dangerous DoS vulnerability (CVE-2020-1967).
Exploiting the vulnerability allows an attacker to carry out denial-of-service (DoS) attacks.
This is the first problem discovered in OpenSSL in 2020.
A dangerous DoS vulnerability has been fixed in OpenSSL (https://www.securitylab.ru/news/506943.php)
SecurityLab, [22.04.20 10:25]
Over the past month, the network has received many complaints from Nintendo users about account hacks and in some cases, money theft.
Hackers massively hack Nintendo accounts and buy game currency (https://www.securitylab.ru/news/506945.php)
SecurityLab, [22.04.20 10: 45]
The topic of today’s issue is startups and investments in the field of information security.
Guests of our Studio will tell you how to become an attractive project for investors, and identify niches where you should wait for the emergence of breakthrough technologies.
Positive Technologies presents the program of the new ether “Ibshnik on udalenka”. (https://www.securitylab.ru/news/506947.php)
SecurityLab, [22.04.20 11:20]
The Ministry of digital development, communications and mass communications of the Russian Federation has published a list of 79 system-forming organizations that can receive additional state support in the context of the coronavirus pandemic (COVID-19).
The list includes the largest Russian Internet companies Yandex and Mail.ru Group, as well as Kaspersky Lab.
Yandex and Mail.ru Group entered the list of system-forming organizations (https://www.securitylab.ru/news/506948.php)
SecurityLab, [22.04.20 14:35]
Cybercriminals are attacking military organizations in the United States with phishing emails exploiting the threat of a coronavirus pandemic.
According to a report From the center for combating cybercrime at the us Department of defense, attackers targeted not only defense companies – their main target is the Pentagon.
Hackers attack the Pentagon with phishing emails on the subject of COVID-19 (https://www.securitylab.ru/news/506956.php)
SecurityLab, [22.04.20 14:35]
The developers of the Zoom video conferencing service have known for several months about the existence of dangerous vulnerabilities in their product, but have not been in a hurry to fix them.
Zoom ignored reports of vulnerabilities in its service for several months (https://www.securitylab.ru/news/506957.php)
SecurityLab, [22.04.20 15: 50]
Microsoft has released important security updates for Office, Office 365 ProPlus, and Paint 3D that fix recently discovered vulnerabilities in the Autodesk 3D library for FBX files.
The vulnerabilities affect Microsoft products with the integrated Autodesk FBX library, in particular Microsoft Office 2016 Click-to-Run (C2R), Microsoft Office 2019 and Office 365 ProPlus for 32 – and 64-bit versions, as well as Paint 3D.
Microsoft has released unscheduled updates for vulnerabilities in Office and Paint 3D (https://www.securitylab.ru/news/507673.php)
SecurityLab, [22.04.20 16: 40]
Experts from ESET found critical vulnerabilities in three different smart home controllers:
- Fibaro Home Center Lite
- eQ-3 Homeatic Central Control Unit (CCU2)
- and ElkoEP eLAN-RF-003.
Exploiting problems allows an attacker to remotely execute code, steal data, and perform MitM attacks.
Vulnerabilities in smart hubs expose homes to remote attacks (https://www.securitylab.ru/news/507674.php)
SecurityLab, [23.04.20 08: 15]
Specialists from Cisco Talos discovered a vulnerability in the Zoom video conferencing service.
Its operation allows an attacker to identify all registered Zoom users within a specific organization.
The vulnerability in Zoom allowed identifying company employees (https://www.securitylab.ru/news/507746.php)
SecurityLab, [23.04.20 08: 20]
Specialists of the IB startup ZecOps discovered two zero-day vulnerabilities in iOS at once, which Apple will fix in the next release of its iOS 13 mobile operating system.
Problems affect iOS, starting with iOS 6.0, released in September 2012 with the release of the iPhone 5, and ending with the current iOS 13.4.1.
Zero-day vulnerabilities found in iOS (https://www.securitylab.ru/news/507747.php)
SecurityLab, [23.04.20 09:25]
For the second time in a row, the Internet Assigned Numbers Authority (IANA) is experiencing difficulties with the root zone key signing ceremony (KSK).
If the last time the problem was caused by a physical safe where the materials needed for the ceremony were stored, now the coronavirus got in the way of IANA.
Because of the coronavirus, IANA changed the KSK key signing procedure for the first time in history (https://www.securitylab.ru/news/507752.php)
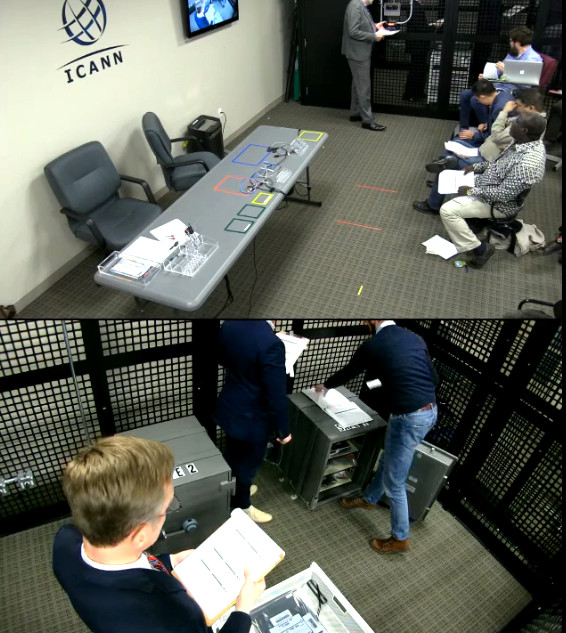
before corona: https://www.iana.org/dnssec/ceremonies
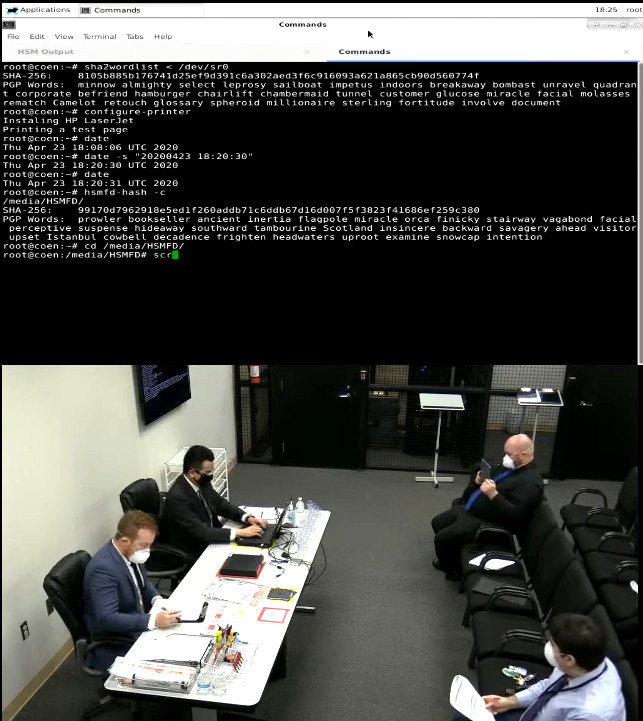
during corona: https://www.iana.org/dnssec/ceremonies
SecurityLab, [23.04.20 10:10]
A new version of the Hoaxcalls DDoS botnet, which can be used for large-scale malicious campaigns, is distributed through an uncorrected vulnerability affecting the management of the ZyXEL Cloud CNM SecuManager network infrastructure.
The new version of the Hoaxcalls botnet exploits an RCE vulnerability in ZyXel (https://www.securitylab.ru/news/507757.php)
SecurityLab, [23.04.20 10: 15]
As practice shows, physically isolated computers are not an impregnable fortress, and they can be hacked if desired (a striking example is the Stuxnet attacks).
However, infecting a computer that is disconnected from the Internet (for example, by connecting a malicious device to it) is one thing, but extracting data from it is quite another.
A method for extracting data from isolated systems using radio is presented (https://www.securitylab.ru/news/507758.php)
Details: “As practice shows, physically isolated computers are by no means an impregnable fortress, and if desired, they can be hacked (a Prime example is the Stuxnet attacks ).
However, infecting a computer that is disconnected from the Internet (for example, by connecting a malicious device to it) is one thing, but extracting data from it is quite another.
One of the theoretical methods for obtaining data from isolated networks involves the use of radio waves.
Mikhail Davydov, a specialist of Duo Labs, showed how using an antenna and a computer script, you can steal data through the signals of a computer’s video card.
In his Seattle lab, Davidov set up the Dell workstation and got to work.
Being at a distance of 15m from the attacked system, the researcher used a radio antenna to study the radio signals coming from the video card, and then wrote a script that allows them to be controlled.
By controlling the duration of each radio transmission from a video card, using a software-defined radio (SDR), Davydov was able to receive the radio signals, then decode them and extract the data.
Recall, last week, specialists of the David Ben-Gurion University in the Negev (Israel) demonstrated a way to extract data from physically isolated computers using vibrations of the cooler.”
SecurityLab, [23.04.20 11: 00]
The Ministry of communications of the Russian Federation proposed to introduce remote identification of mobile subscribers through the Unified identification and authentication system (ESIA) and the unified biometric system (EBS) of Rostelecom created on its basis.
According to the Ministry, this will help doing business while the communication salons are closed, and in the future will contribute to the development of virtual eSIM, writes Kommersant.
The Ministry of communications has proposed remote identification of subscribers (https://www.securitylab.ru/news/507760.php)
SecurityLab, [23.04.20 11:25]
State Duma deputies from “Fair Russia” Fedot Tumusov and Dmitry Ionin proposed a bill to stop blocking Telegram.
According to the authors, unsuccessful attempts to block the messenger “damage the prestige of the state power”.
The state Duma proposed to stop trying to block Telegram (https://www.securitylab.ru/news/507775.php)
SecurityLab, [23.04.20 14: 40]
Security researcher James Forshaw (James Forshaw) from the Google Project Zero team spoke about a problem in the core of Windows 10 that allowed you to escape from the Google Chrome sandbox.
Windows 10 update has weakened the security of Google Chrome (https://www.securitylab.ru/news/507791.php)
SecurityLab, [23.04.20 15:45]
One of the users of the anonymous 4chan web forum published the source codes of two Valve video games-CS:GO and Team Fortress 2.
CS source codes are published Online:GO and Team Fortress 2 (https://www.securitylab.ru/news/507792.php)
liked this article?
- only together we can create a truly free world
- plz support dwaves to keep it up & running!
- (yes the info on the internet is (mostly) free but beer is still not free (still have to work on that))
- really really hate advertisement
- contribute: whenever a solution was found, blog about it for others to find!
- talk about, recommend & link to this blog and articles
- thanks to all who contribute!

