What devices lurk in the user’s network? What computers are online what offline?
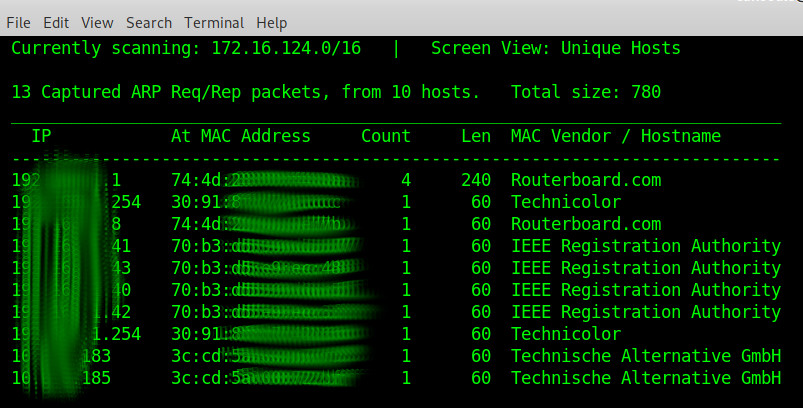
quick arp scan with
netdiscover (manpage: netdiscover.man.txt
scanning with nmap
What services/ports in what versions are online/open?  over poorly or not so poorly documented LANs the user-admin can get an fast overview by using nmap.
over poorly or not so poorly documented LANs the user-admin can get an fast overview by using nmap.
what is neat: (usually) every vendor has it’s own mac address, so just by looking at the manufacturers devices (sometimes) can be identified properly. (BROTHER should probably always be a printer or scanner)
hostnamectl; # tested with this version
Operating System: Debian GNU/Linux 10 (buster)
Kernel: Linux 4.19.0-6-amd64
Architecture: x86-64
# become root (setup and run nmap as root to use all it's full capabilities)
su - root
# check out this most basic ping based network discovery script
# CentOS7: no root required for arp and ping
# Debian11: root required for arp, not ping
scan_network_device_simple_ping.sh.txt
# it will scan a subnet with ping (try to discover if host is alive (ping))
# and try to discover ip -> hostname (host) mac address (arp -n -a)
# it will output to current directory
# follow the log change
tail -f scan_network_device_simple_ping.192.168.0.log
# filter the output for dead hosts
cat scan_network_device_simple_ping.192.168.0.log |grep -v "(unkown) (unkown)"
# install nmap network scanner
# plus a xml to html conversion tool called xsltproc
# under fedora/centos/redhat/rpm
yum install nmap libxslt.x86_64;
# under debian/mint/ubuntu
apt-get install nmap xsltproc;
# get a quick overview
# via netdiscover (creditz)
# show what network interfaces are what
ip -c a
# modify so it fits the nic that shall be used
netdiscover -i eth0
# via nmap
nmap -r -sn -PR 192.168.0.1/24 # over the LAN-network (this is pretty fast, 2seconds even on wifi)
# what it does:
# -r: Scan ports consecutively - don't randomize
# -sn (No port scan)
This option tells Nmap not to do a port scan after host discovery,
and only print out the available hosts that responded to the host
discovery probes.
This is often known as a “ping scan”, but you can also request that traceroute and NSE host scripts be run.
This is by default one step more intrusive than the list scan, and can often be used for the same purposes.
It allows light reconnaissance of a target network without attracting much attention.
Knowing how many hosts are up is more valuable to attackers than the list provided by list scan of every single IP and host name.
Systems administrators often find this option valuable as well.
It can easily be used to count available machines on a network or monitor server availability.
This is often called a ping sweep, and is more reliable than pinging the broadcast address because many hosts do not reply to broadcast queries.
The default host discovery done with -sn consists of an ICMP echo request, TCP SYN to port 443, TCP ACK to port 80, and an ICMP timestamp request by default.
When executed by an unprivileged user, only SYN packets are sent (using a connect call) to ports 80 and 443 on the target.
When a privileged user tries to scan targets on a local ethernet network, ARP requests are used unless –send-ip was specified.
The -sn option can be combined with any of the discovery probe types (the -P* options, excluding -Pn) for greater flexibility.
If any of those probe type and port number options are used, the default probes are overridden.
When strict firewalls are in place between the source host running Nmap and the target network, using those advanced techniques is recommended.
Otherwise hosts could be missed when the firewall drops probes or their responses.
In previous releases of Nmap, -sn was known as -sP.
-PR (ARP Ping)
One of the most common Nmap usage scenarios is to scan an ethernet LAN.
On most LANs, especially those using private address ranges specified by RFC 1918[5], the vast majority of IP addresses are unused at any given time.
When Nmap tries to send a raw IP packet such as an ICMP echo request, the operating system must determine the destination hardware (ARP) address corresponding to the target IP so that it can properly address the ethernet frame.
This is often slow and problematic, since operating systems weren’t written with the expectation that they would need to do millions of ARP requests against unavailable hosts in a short time period.
ARP scan puts Nmap and its optimized algorithms in charge of ARP requests.
And if it gets a response back, Nmap doesn’t even need to worry about the IP-based ping packets since it already knows the host is up.
This makes ARP scan much faster and more reliable than IP-based scans.
So it is done by default when scanning ethernet hosts that Nmap detects are on a local ethernet network.
Even if different ping types (such as -PE or -PS) are specified, Nmap uses ARP instead for any of the targets which are on the same LAN.
If you absolutely don’t want to do an ARP scan, specify –disable-arp-ping.
For IPv6 (-6 option), -PR uses ICMPv6 Neighbor Discovery instead of ARP.
Neighbor Discovery, defined in RFC 4861, can be seen as the IPv6 equivalent of ARP.
nmap -sP -n 192.168.0.0/24 nmap -sP -PA21,22,25,3389 192.168.0.* # find all network printers, output printer vendor and MAC and IP nmap -p 9100,515,631 192.168.0.* --open # this is the detailed scan nmap -sS -p- -PE -PP -PS80,443 -PA3389 -PU40125 -A -T4 -oA networkscan-result-nmap-%D 192.168.0.0-255 # it takes a lot of time... so please be patient and come back later (3 cups coffee kind of later X-D) also: the resulting xml is not well viewable inside a browser, you need to convert: xsltproc networkscan-result-nmap-030118.xml -o networkscan-result-nmap-030118.html
# more examples
# arp scan local network (for mac addresses) nmap -sP -n 192.168.0.0/24 nmap -sS -O 192.168.0.123 (OS Detection) nmap -sO 192.168.0.123 (Protocoll Scan) nmap -sU -p1-1024 192.168.0.123 (UDP Scan)
# find all printers on the network
nmap -p 9100,515,631 192.168.0.0/24 -oX printers.xml
# convert the results into a format humans can read
xsltproc printers.xml -o printers.html
# show the results
firefox printers.html
# find all snmp enabled devices
nmap -sU -p 161 --script default,snmp-sysdescr 192.168.0.0/24
root or non-root?
short answer: use nmap as root or some systems mide be able to hide from your scan. long answer: “Nmap adapts its techniques to use the best available methods using the current privilege level, unless you explicitly request something different. The things that Nmap needs root (or sudo) privilege for on Linux are: Sniffing network traffic with libpcap Sending raw network traffic You can use the -d option to see what Nmap is doing in the background, but the short answer is that with root privilege on an Ethernet LAN (like you are using, based on the IP addresses you listed), Nmap will send raw ARP packets and sniff for results. Responding to ARP requests is a prerequisite to IP communication on such a network, so it’s nearly impossible to block or hide from this type of scan. If you do not have root privilege, Nmap falls back to trying to connect to 2 TCP ports (80 and 443), considering the host “up” if the connection succeeds or is reset. A system with a drop-all firewall and no services on 80 or 443 will not show up with this scan. You can read more about Nmap’s host discovery techniques in the host discovery section of the man page.” (src)
Example Results: for nmap detailed scan fritzbox 7170
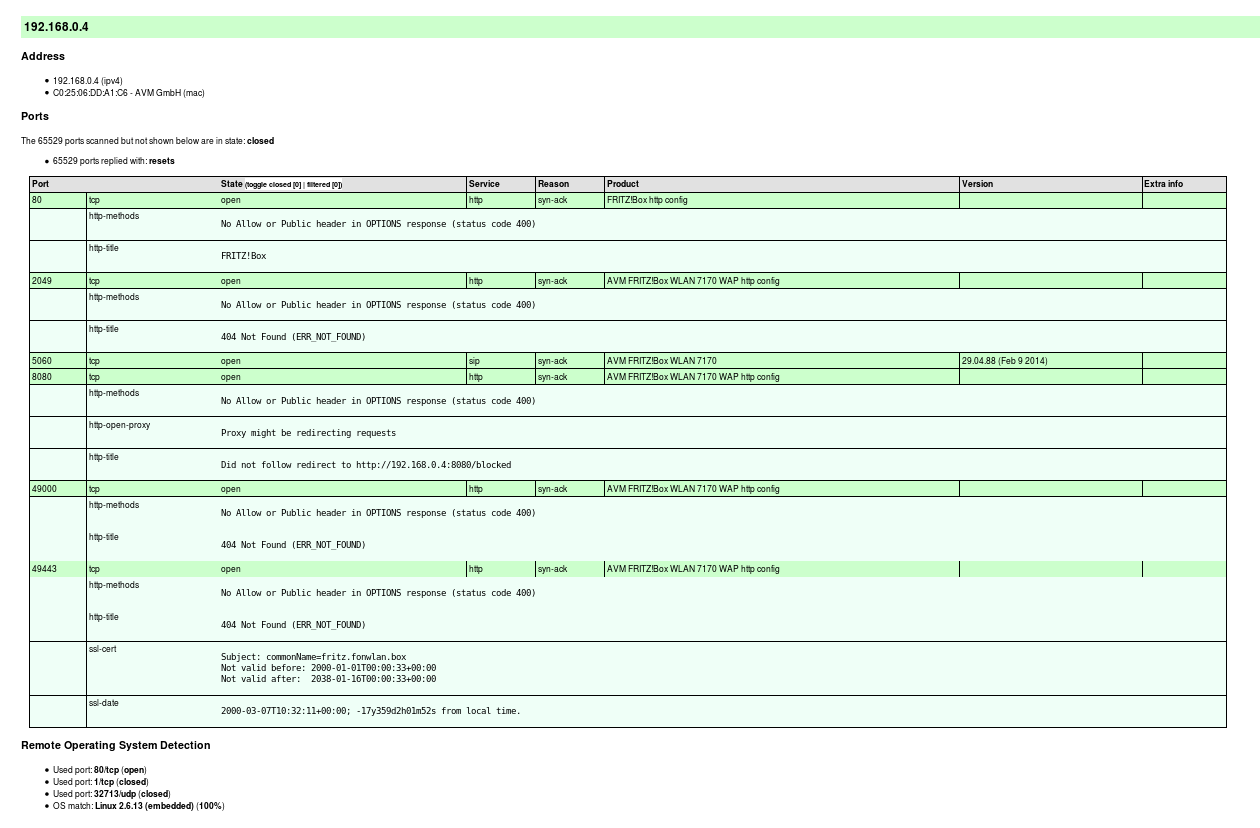 nmap detailed scan fritzbox 7170[/caption] These options are described in later chapters, but here is a quick summary of them. -sS Enables the efficient TCP port scanning technique known as SYN scan. Felix would have added a U at the end if he also wanted to do a UDP scan, but he is saving that for later. SYN scan is the default scan type, but stating it explicitly does not hurt.
nmap detailed scan fritzbox 7170[/caption] These options are described in later chapters, but here is a quick summary of them. -sS Enables the efficient TCP port scanning technique known as SYN scan. Felix would have added a U at the end if he also wanted to do a UDP scan, but he is saving that for later. SYN scan is the default scan type, but stating it explicitly does not hurt.
-p- Requests that Nmap scan every port from 1-65535. This is more comprehensive than the default, which is to scan only the 1,000 ports which we’ve found to be most commonly accessible in large-scale Internet testing. This option format is simply a short cut for -p1-65535. Felix could have specified -p0-65535 if he wanted to scan the rather illegitimate port zero as well. The -p option has a very flexible syntax, even allowing the specification of a differing set of UDP and TCP ports.
-PE -PP -PS80,443 -PA3389 -PU40125 These are all host discovery techniques (ping types) used in combination to determine which targets on a network really available and avoid wasting a lot of time scanning IP addresses that are not in use. This particular incantation sends ICMP echo request and timestamp request packets; TCP SYN packet to ports 80 and 443; TCP ACK packets to port 3389; and a UDP packet to port 40,125. If Nmap receives a response from a target host to any of these probes, it considers the host to be up and available for scanning. This is the most effective six-probe combination that we’ve found in large-scale empirical testing for host discovery against targets over the Internet. It is more extensive than the Nmap default, which is -PE -PS443 -PA80 -PP. In a pen-testing situation, you often want to scan every host even if they do not seem to be up. After all, they could just be heavily filtered in such a way that the probes you selected are ignored but some other obscure port may be available. To scan every IP whether it shows an available host or not, specify the -Pn option instead of all of the above. Felix starts such a scan in the background, though it may take many hours to complete.
-A This shortcut option turns on Advanced and Aggressive features such as OS and service detection. At the time of this writing it is equivalent to -sV -sC -O –traceroute (version detection, Nmap Scripting Engine with the default set of scripts, remote OS detection, and traceroute). More features may be added to -A later.
-T4 Adjusts timing to the aggressive level (#4 of 5). This is the same as specifying -T aggressive, but is easier to type and spell. In general, the -T4 option is recommended if the connection between you and the target networks id reasonably fast and reliable.
-oA avatartcpscan-%D Outputs results in every format (normal, XML, grepable) to files named avatartcpscan-. where the extensions are .nmap, .xml, and .gnmap respectively. The gives the month, day, and year in a format like 073010. All of the output formats include the start date and time, but Felix likes to note the date explicitly in the filename. Normal output and errors are still sent to stdout[4] as well.
6.209.24.0/24 6.207.0.0/22 These are the Avatar Online netblocks discussed above. They are given in CIDR notation, but Nmap allows them to be specified in many other formats. For example, 6.209.24.0/24 could instead be specified as 6.209.24.0-255. Since such a comprehensive scan against more than a thousand IP addresses could take a while, Felix simply starts it executing and resumes work on his Yagi antenna. An couple hours later he notices that it has finished and takes a peek at the results. Example 1.2 shows one of the machines discovered. https://nmap.org/book/nmap-overview-and-demos.html
liked this article?
- only together we can create a truly free world
- plz support dwaves to keep it up & running!
- (yes the info on the internet is (mostly) free but beer is still not free (still have to work on that))
- really really hate advertisement
- contribute: whenever a solution was found, blog about it for others to find!
- talk about, recommend & link to this blog and articles
- thanks to all who contribute!