ssh next to https (TLS/SSL) is probably THE most essential building block of secure (unhacked) open source networked computing.
CVE-2023-48795 is a (wo)man-in-the-middle-attack, so an attacker would have to sit on the same network (LAN) or somewhere between ssh client and ssh server.
to test if the user’s ssh server is vulnerable donate to this volunteer: (or university)
hostnamectl; # tested on Operating System: Debian GNU/Linux 12 (bookworm) Kernel: Linux 6.1.0-17-amd64 sshd --version unknown option -- - # but still gives usefull infos OpenSSH_9.2p1 Debian-2+deb12u2, OpenSSL 3.0.11 19 Sep 2023 wget https://github.com/RUB-NDS/Terrapin-Scanner/releases/download/v1.1.2/Terrapin_Scanner_Linux_amd64 chmod +x ./Terrapin_Scanner_Linux_amd64 ./Terrapin_Scanner_Linux_amd64 --version Terrapin Vulnerability Scanner v1.1.2 ./Terrapin_Scanner_Linux_amd64 --connect 127.0.0.1 --json { "Banner": "SSH-2.0-OpenSSH_9.2p1 Debian-2+deb12u2", "SupportsChaCha20": true, "SupportsCbcEtm": false, "SupportsStrictKex": true, "Vulnerable": false <- THANKS G*D }
“The SSH transport protocol with certain OpenSSH extensions, found in OpenSSH before 9.6 and other products, allows remote attackers to bypass integrity checks such that some packets are omitted (from the extension negotiation message), and a client and server may consequently end up with a connection for which some security features have been downgraded or disabled, aka a Terrapin attack. This occurs because the SSH Binary Packet Protocol (BPP), implemented by these extensions, mishandles the handshake phase and mishandles use of sequence numbers. For example, there is an effective attack against SSH’s use of ChaCha20-Poly1305 (and CBC with Encrypt-then-MAC). The bypass occurs in chacha20-poly1305@openssh.com and (if CBC is used) the -etm@openssh.com MAC algorithms. This also affects Maverick Synergy Java SSH API before 3.1.0-SNAPSHOT, Dropbear through 2022.83, Ssh before 5.1.1 in Erlang/OTP, PuTTY before 0.80, AsyncSSH before 2.14.2, golang.org/x/crypto before 0.17.0, libssh before 0.10.6, libssh2 through 1.11.0, Thorn Tech SFTP Gateway before 3.4.6, Tera Term before 5.1, Paramiko before 3.4.0, jsch before 0.2.15, SFTPGo before 2.5.6, Netgate pfSense Plus through 23.09.1, Netgate pfSense CE through 2.7.2, HPN-SSH through 18.2.0, ProFTPD before 1.3.8b (and before 1.3.9rc2), ORYX CycloneSSH before 2.3.4, NetSarang XShell 7 before Build 0144, CrushFTP before 10.6.0, ConnectBot SSH library before 2.2.22, Apache MINA sshd through 2.11.0, sshj through 0.37.0, TinySSH through 20230101, trilead-ssh2 6401, LANCOM LCOS and LANconfig, FileZilla before 3.66.4, Nova before 11.8, PKIX-SSH before 14.4, SecureCRT before 9.4.3, Transmit5 before 5.10.4, Win32-OpenSSH before 9.5.0.0p1-Beta, WinSCP before 6.2.2, Bitvise SSH Server before 9.32, Bitvise SSH Client before 9.33, KiTTY through 0.76.1.13, the net-ssh gem 7.2.0 for Ruby, the mscdex ssh2 module before 1.15.0 for Node.js, the thrussh library before 0.35.1 for Rust, and the Russh crate before 0.40.2 for Rust.”
https://security-tracker.debian.org/tracker/CVE-2023-48795
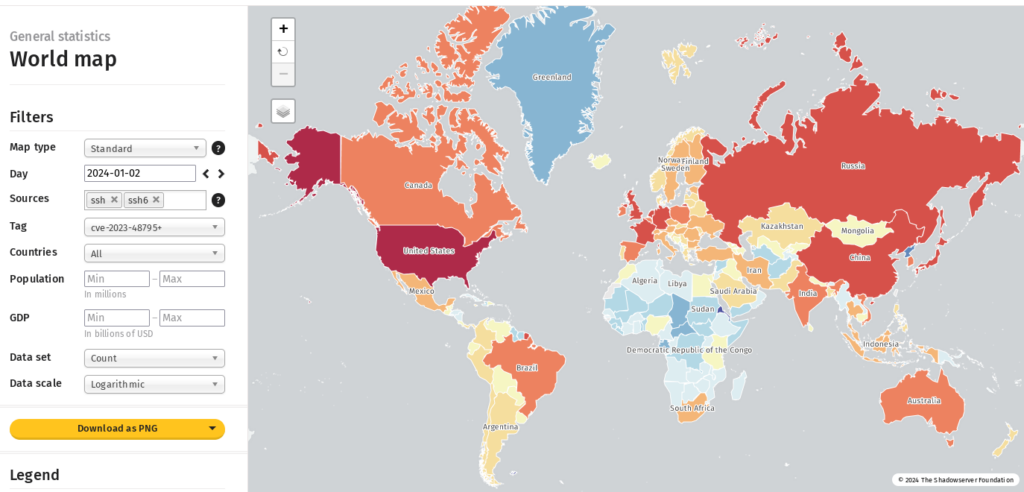
https://infosec.exchange/@shadowserver/ https://dashboard.shadowserver.org/statistics/combined/map/?map_type=std&day=2024-01-02&source=ssh&source=ssh6&tag=cve-2023-48795%2B&geo=all&data_set=count&scale=log
https://security-tracker.debian.org/tracker/source-package/openssh
https://nvd.nist.gov/vuln/detail/CVE-2023-48795
https://superuser.com/questions/744816/how-do-i-specify-the-key-exchange-method-in-openssh
AFAIK it is fixed in this version of ssh server, but to be on the safe side, firewall-disable ssh access until more updates are provided.
sshd --version unknown option -- - OpenSSH_9.2p1 Debian-2+deb12u2, OpenSSL 3.0.11 19 Sep 2023
| openssh (PTS) | buster | 1:7.9p1-10+deb10u2 | vulnerable |
| buster (security) | 1:7.9p1-10+deb10u4 | fixed | |
| bullseye | 1:8.4p1-5+deb11u2 | vulnerable | |
| bullseye (security) | 1:8.4p1-5+deb11u3 | fixed | |
| bookworm | 1:9.2p1-2+deb12u1 | vulnerable | |
| bookworm (security) | 1:9.2p1-2+deb12u2 | fixed | |
| sid, trixie | 1:9.6p1-2 | fixed |
liked this article?
- only together we can create a truly free world
- plz support dwaves to keep it up & running!
- (yes the info on the internet is (mostly) free but beer is still not free (still have to work on that))
- really really hate advertisement
- contribute: whenever a solution was found, blog about it for others to find!
- talk about, recommend & link to this blog and articles
- thanks to all who contribute!


