SecurityLab, [22.12.20 10:00]
Google has explained the reasons for the massive failure of its services that took place last week.
Recall that on December 14 of this year, users around the world for 47 minutes could not access Gmail, YouTube and other Google services.
https://www.securitylab.ru/news/515032.php
SecurityLab, [22.12.20 14:35]
The owner of the BitGrail cryptocurrency exchange, which was declared bankrupt last year, is suspected of involvement in a series of hacks that led to losses of 120 million euros.
https://www.securitylab.ru/news/515039.php
SecurityLab, [22.12.20 15:45]
A former information security consultant for SolarWinds, a company that produces software for monitoring and managing IT resources, warned management about security threats and even offered a plan to eliminate them, but was never heard from.
https://www.securitylab.ru/news/515041.php
SecurityLab, [23.12.20 07:50]
Tech giants Microsoft and Google have joined Facebook’s legal battle against Israeli hacker company NSO.
The filing, which was filed in the U.S. Court of Appeals for the Ninth Circuit, opens a new front in Facebook’s lawsuit against NSO, which was filed in 2019.
The NSO argues that because it sells digital hacking tools to police and spy agencies, it should enjoy “sovereign immunity.”
The reason for filing the lawsuit last year was the findings of analysts of the WhatsApp messenger (part of Facebook, Inc.) that approximately 1,400 of their customers received malware sent by the defendant firm.
There have also been reports in the media that the Israeli company’s spyware is being used to harass journalists in India, politicians in Spain and human rights activists in Morocco.
https://www.securitylab.ru/news/515045.php
SecurityLab, [23.12.20 08:30]
In the early 2010s, Chinese intelligence agencies hacked the CIA’s online platform, which is used by operatives to secretly exchange information with their agents, and revealed the identities of American intelligence officers operating in China.
This event marked the beginning of a decade-long war for global control over data between Beijing and Washington, writes the international news agency Foreign Policy, which devoted a series of articles to this issue.
https://www.securitylab.ru/news/515058.php
SecurityLab, [23.12.20 08:40]
Cybersecurity researchers at Flashpoint have reported rising prices for access to RDP servers, stolen payment card data, and a “DDoS-as-a-service” business model on underground forums and trading platforms.
https://www.securitylab.ru/news/515059.php
SecurityLab, [23.12.20 10:35]
On Tuesday, December 22, the State Duma of the Russian Federation adopted and approved two draft laws in the field of information technology.
https://www.securitylab.ru/news/515062.php
SecurityLab, [23.12.20 15:10]
Microsoft’s digital certificate expires at the end of December, but the company is urging not to remove it, as it could cause the operating system to malfunction.
https://www.securitylab.ru/news/515060.php
SecurityLab, [23.12.20 15:15]
In July of this year, Apple announced the launch of a new program called Security Research Device (SRD),
designed to provide experts with specially configured iPhones that are equipped with unique code execution policies to support security research.
https://www.securitylab.ru/news/515061.php
SecurityLab, [23.12.20 16:05]
Facebook has informed the US authorities that it is ready to offer assistance in developing an alternative social network.
Thus, the tech giant is trying to show that it does not violate antitrust laws and is not against competition, but the authorities refused this offer.
This was reported by The Washington Post.
https://www.securitylab.ru/news/515069.php
SecurityLab, [23.12.20 16:10]
Millions of devices are open to potential CyberAttacks using vulnerabilities that can be exploited using tools stolen recently from the information security company FireEye.
Details: FireEye tools exploit 16 vulnerabilities in products from Pulse Secure, Microsoft, Fortinet, Atlassian, Citrix, Zoho, and Adobe.
However, according to Qualys, the majority of vulnerable installations (99.84%) are open to attacks through eight critical and highly dangerous vulnerabilities in Microsoft products.
Fixing these vulnerabilities will significantly reduce the attack surface.
https://www.securitylab.ru/news/515070.php
SecurityLab, [23.12.20 19:30]
The State Duma in the first reading approved a government bill to improve the legislation on state genomic registration.
https://www.securitylab.ru/news/515074.php
SecurityLab, [24.12.20 00:20]
Students want to learn the rules of behavior on the Internet.
Children will also gain skills in working with personal data.
Classes will be held within the framework of computer science classes.
Deputy Chairman of the Federation Council Committee on constitutional Legislation Irina Rukavishnikova believes that the new subject should be introduced into the curriculum, and not hold individual actions.
They will begin to study the norms of literacy in the Network in the lower grades.
https://www.securitylab.ru/news/515075.php
SecurityLab, [24.12.20 08:35]
The company Nintendo once again this year was the victim of a data leak.
Like previous leaks, information regarding the Nintendo Switch game console was published on the 4chan form.
In particular, the attackers posted data on the development of Switch, including the 2015 SDK and documentation related to the security of the console.
https://www.securitylab.ru/news/515077.php
SecurityLab, [24.12.20 08:40]
Representatives of the American Civil Liberties Union (ACLU) announced their intentions to obtain information through the court regarding the hidden and relatively new ability of the FBI to hack encrypted devices.
https://www.securitylab.ru/news/515078.php
SecurityLab, [24.12.20 09:30]
In June of this year, Microsoft released a fix for a vulnerability in Windows that allows attackers to increase their rights on a compromised system to the kernel level.
However, the patch did not work.
The problem that skilled hackers exploited back in May, before the release of the fix, can still be used in attacks (though in a slightly different way) with the help of a new PoC exploit.
https://www.securitylab.ru/news/515079.php
SecurityLab, [24.12.20 10:40]
Apple had another reason to abandon Intel processors and start developing its own M1 chips, and it’s not just about improving performance.
According to former Intel engineer Zheng Li in an interview with Apple analyst and Loup Ventures co-founder Gene Munster, Intel sold processor technologies intended for the 2006 Apple MacBook Air (Apple’s first ultra-thin laptop) to its direct competitors.
https://www.securitylab.ru/news/515081.php
SecurityLab, [24.12.20 15:20]
Experts from Kaspersky Lab and Yandex have discovered a large-scale potentially malicious campaign in which attackers inject malicious code into browser extensions.
Experts have identified more than twenty modified extensions, including the popular Frigate Light, Frigate CDN and SaveFrom.
https://www.securitylab.ru/news/515085.php
SecurityLab, [24.12.20 17:40]
The spread of military confrontation to cyberspace and outer space increases the risks of interference in control systems and the use of nuclear weapons, said the Chief of the General Staff of the Armed Forces.
First Deputy Defense Minister of the Russian Federation, Army General Valery Gerasimov at a briefing for foreign attaches.
https://www.securitylab.ru/news/515093.php
SecurityLab, [24.12.20 23:40]
In Belarus, hackers broke into the internal information network of the enforcement departments of the Belarusian Ministry of Justice.
Hackers began to broadcast a video of a political nature on employees ‘ computers.
https://www.securitylab.ru/news/515094.php
SecurityLab, [25.12.20 08:05]
The US Financial Crimes Enforcement Network (FinCEN) has proposed new rules that will make it easier for the authorities to track cryptocurrency transactions.
And although 15 days are allotted for the discussion of the initiative, the cryptocurrency exchange Coinbase and the Electronic Frontier Fund are sounding the alarm, since the discussion period falls on the winter holidays, and taking into account the weekends, it is significantly reduced.
https://www.securitylab.ru/news/515102.php
SecurityLab, [25.12.20 09:15]
The period before the winter holidays is a favorite time for fishers.
In this regard, GoDaddy decided to check whether its own employees could fall for the bait of scammers, and conducted secret testing, which caused a mixed reaction from the public.
https://www.securitylab.ru/news/515104.php
SecurityLab, [25.12.20 10:05]
Russian cryptocurrency exchange Livecoin reported that its computer systems were hacked and it lost control of some servers.
https://www.securitylab.ru/news/515105.php
SecurityLab, [25.12.20 11:30]
Allegedly, Russian hackers broke into the computer systems of Microsoft’s corporate partner and stole the emails of users of Microsoft cloud services, as well as the correspondence of one of the private companies.
This was reported by The Washington Post.
https://www.securitylab.ru/news/515106.php
SecurityLab, [25.12.20 15:55]
The cybercrime group REvil has stolen the data of a large network of cosmetic clinics and is threatening to publish photos of patients before and after operations.
https://www.securitylab.ru/news/515111.php
SecurityLab, [25.12.20 16:00]
The malware campaign, in which attackers hacked into a number of government agencies and technology companies through a malicious update for SolarWinds Orion software, also affected dozens of critical infrastructure enterprises.
According to the company, which is investigating the hacking of some organizations, among the victims are electric power, oil and manufacturing companies that use the Orion software, writes The Intercept.
https://www.securitylab.ru/news/515112.php
SecurityLab, [26.12.20 10:50]
Web servers on GNU Linux and millions of Android devices are at risk due to a vulnerability in the Linux kernel that affects the pseudo-random number generator and allows for cross-level attacks due to the fact that the UDP, IPv6 and IPv4 generation algorithms running on some Linux systems use a vulnerable RNG.
Details: The issue allows tracking Linux and Android devices even when the browser has private mode enabled or a VPN is used.
As explained by the author of the study, information security expert Amit Klein (Bar-Ilan University, Israel), an attacker can determine the internal state of the PRNG at one OSI level and use this data to predict a random numeric value at another OSI level.
Thus, an attacker can perform a DNS cache poisoning attack on GNU Linux systems both locally and remotely.
The condition is that the DNS server must be located outside the network.
DNS spoofing can be used for various malicious actions, such as intercepting email and HTTP traffic, bypassing anti-spam mechanisms and email blacklists, conducting a local DoS attack, tracking the NTP client, and so on.
Moreover, the problem discovered by Klein also allows you to track GNU Linux and Android devices even when the browser has private mode enabled or a VPN is used.
According to the expert, the most vulnerable to these attacks are servers running on Ubuntu.
About 13.4% of web servers run on Ubuntu, 3-5% of servers use Ubuntu and a public DNS service, meeting the conditions for a potential attack.
However, this indicator may be higher, Klein believes, since servers that use external private DNS servers (for example, those managed by Internet insiders) are also at risk.
The expert notified the GNU Linux development team about the vulnerability (CVE-2020-16166) in March of this year.
The problem was fixed with the release of a patch that implements a more reliable PRNG that uses SipHash (fixed versions 5.10-rc1, 5.9.2, 5.4.78, 4.19.158, 4.14.207, 4.9.244 and 4.4.244).
In Android, the problem was fixed in October, and an alternative method of protecting against this attack is using a proxy or Tor.
The DNS-over-HTTPS Protocol also blocks DNS spoofing, but does not protect against tracking.
https://www.securitylab.ru/news/515113.php
SecurityLab, [27.12.20 12:35]
In the Kaluga region, the Obninsk City Court on December 24 granted the claim of Roskomnadzor to the local local historian Artem Mainas.
He was found guilty of violating the law “On personal Data” because of the publication of photos of the tombstone of scientist Felix Kashin on a website dedicated to the history and attractions of the region.
https://www.securitylab.ru/news/515115.php
SecurityLab, [28.12.20 08:15]
SolarWinds has published an updated security notice about additional SUPERNOVA malware spreading through its Orion IT resource management platform.
https://www.securitylab.ru/news/515116.php
SecurityLab, [28.12.20 08:30]
U.S. officials and cybersecurity experts investigating the major hacks of the U.S. Treasury Department and FireEye believe the cyberattacks were eventually discovered thanks to a mistake made by hackers while advancing on the compromised network. This was reported by the CNN website.
https://www.securitylab.ru/news/515117.php
SecurityLab, [28.12.20 09:40]
The HarmonyOS mobile operating system is the first OS from Huawei.
It is supposed to replace Android on the company’s smartphones, since the current version of Android without Google services (Google Mobile Services, GMS) is not enough for Huawei mobile devices.
https://www.securitylab.ru/news/515118.php
SecurityLab, [28.12.20 10:15]
Eleven months after Microsoft officially ended technical support for the Windows 7 operating system, Google has finally called on Chromium developers to stop using this OS.
https://www.securitylab.ru/news/515119.php
SecurityLab, [28.12.20 10:40]
According to a new notification from the US-CERT Coordination Center, hackers took advantage of a zero-day vulnerability to deploy the SUPERNOVA backdoor in the SolarWinds Orion platform.
The CVE-2020-10148 vulnerability affects the SolarWinds Orion API and allows attackers to execute unauthorized API commands and thereby compromise SolarWinds installations.
https://www.securitylab.ru/news/515121.php
SecurityLab, [28.12.20 11:40]
A group of cryptography experts has offered a theory as to why law enforcement still manages to crack the iPhone, despite constant iOS fixes and the mobile device’s security levels.
Details: According to Matthew Green, a cybersecurity researcher and Professor of cryptography at Johns Hopkins University, hackers and intelligence agencies do not need to break into Apple’s Secure Enclave hardware component, which is responsible for secure data storage, because it is too difficult.
Instead, they use not just a vulnerability, but a system feature of iOS that does not protect all types of user data on the device.
The iPhone can be in one of two States:
- before first unlock (BFU) and
- after first unlock (AFU)
When a user turns on their device for the first time and enters the password, it enters the AFU state.
When a user enters their code, the iPhone uses it to obtain various sets of cryptographic keys that remain in memory and are used to encrypt files.
When the user locks their device again, it does not go into BFU, but remains in the AFU state and stays in it for about 95% of the time.
Green notes that only one set of cryptographic keys is retrieved from memory.
This set is saved until the user unlocks their iPhone again, and is used to decrypt many iPhone files that fall under a certain security class.
Other sets of keys that remain in memory are used to decrypt all other files.
To crack a single set of encryption keys, intelligence agencies and hackers can resort to using relatively simple software exploits that allow them to bypass the lock screen and decrypt most of the files.
According to Apple’s documentation, the highest security class in the AFU state applies only to mail and app launch data.
It is noteworthy that prior to 2012, encryption covered much more data.
It remains unknown why Apple has weakened security, but green believes that the company has abandoned maximum security to ensure the operation of certain applications and system functions related to geolocation and other technologies.
https://www.securitylab.ru/news/515122.php
SecurityLab, [29.12.20 08:10]
According to the Finnish parliament, hackers gained access to its internal IT system and hacked the e-mail of some deputies.
The incident took place in the autumn of this year, but was discovered by IT specialists of the parliament only this month.
The hacking is currently being investigated by the Central Criminal Police (Keskusrikospoliisi, KRP).
https://www.securitylab.ru/news/515145.php
SecurityLab, [29.12.20 08:35]
One of the world’s largest manufacturers of home appliances, Whirlpool, was the victim of a cyberattack using the Nefilim ransomware, in which hackers stole data before encrypting the devices.
https://www.securitylab.ru/news/515146.php
SecurityLab, [29.12.20 09:40]
On June 26, 2017, the body of an elderly auto mechanic, Ronald French, was found in a cornfield in Kalamazoo County, Michigan, killed with extreme cruelty.
For more than two years, the police could not gather enough evidence to identify the suspect, until one of the investigating detectives learned about a new, increasingly popular field of criminology: the collection and analysis of data stored on the onboard computers of cars.
https://www.securitylab.ru/news/515148.php
SecurityLab, [29.12.20 10:10]
The State Fund of Funds “RVC” reported on the development of the draft national standard GOST R “Information Technologies. Internet of Things. Wireless data transmission protocol based on narrow-band radio signal modulation (NB-Fi)”.
https://www.securitylab.ru/news/515149.php
SecurityLab, [29.12.20 10:30]
According to the research of the Scientific and Technical Center of the Federal State Unitary Enterprise “Main Radio Frequency Center of Russia”, along with the residents of four other countries, Russians are least dependent on global Internet platforms.
https://www.securitylab.ru/news/515150.php
SecurityLab, [29.12.20 15:00]
Participants of the public project “RosKomSvoboda” conducted a study and told about the main tools for surveillance that were introduced by governments of different countries under the pretext of containing the spread of the coronavirus pandemic.
https://www.securitylab.ru/news/515159.php
SecurityLab, [30.12.20 08:05]
Draft law No. 1087071-7, which obliges Internet service providers to provide their subscribers with free access to socially significant sites, has been submitted to the State Duma of the Russian Federation.
According to the explanatory note, the initiative was introduced by the Cabinet of Ministers as part of the implementation of the address of Russian President Vladimir Putin to the Federal Assembly.
https://www.securitylab.ru/news/515177.php
SecurityLab, [30.12.20 08:35]
Specialists of the Central Bank of the Russian Federation conducted a review of reporting on information security incidents when transferring funds for the 3rd quarter of 2019 and 2020.
https://www.securitylab.ru/news/515178.php
SecurityLab, [30.12.20 10:25]
Japanese corporation Kawasaki Heavy Industries reported a security incident and a possible data leak after attackers gained unauthorized access to its server from several foreign offices.
https://www.securitylab.ru/news/515181.php
SecurityLab, [30.12.20 11:20]Teleportation Systems Toward a
The cloud storage provider Wasabi suffered a system failure after the domain used for storage endpoints was disabled due to the placement of malware by one of the users.
https://www.securitylab.ru/news/515182.php
SecurityLab, [30.12.20 14:20]
IB startup Corellium has won a lawsuit against Apple, and the ruling will have far-reaching implications for iPhone security research and copyright law.
https://www.securitylab.ru/news/515184.php
SecurityLab, [30.12.20 16:10]
Wednesday, December 30, Russian President Vladimir Putin signed a number of laws relating to anti-censorship by foreign Internet platforms, libel on the Internet, recognition of Internet resources, social networks and combat grey SIM cards.
https://www.securitylab.ru/news/515187.php
SecurityLab, [30.12.20 17:20]
Roskomnadzor (The Federal Service for Supervision of Communications, Information Technology, and Mass Media (Roskomnadzor) is a Federal Executive Authority of the Russian Federation, performing the following functions: control and supervision of mass media (including electronic mass media), mass communications, information technology, and telecommunications (src: Wiki)) has started using AI (artificial intelligence) technologies to improve the speed and accuracy of detecting illegal information on the Internet.
https://www.securitylab.ru/news/515188.php
SecurityLab, [31.12.20 00:20]
Early last year, police responded to a call in Woodbridge, Virginia, where they were told a black man had stolen several items from a gift shop.
Details: When the police stopped the alleged criminal, he showed them a license issued in Tennessee, apologized and said that he wanted to pay for the goods.
The police quickly determined that the document was fake and tried to detain the man.
But he rushed to the car, losing his Shoe in the process,and then drove it straight at the police. Fortunately, none of them were injured.
Later, the man found out that the police identified him using Clearview AI, a controversial artificial intelligence – based software for facial recognition.
The use of the system was banned in January 2020 after a re-evaluation of its operation (a year after parks ‘ arrest).
https://www.securitylab.ru/news/515189.php
SecurityLab, [31.12.20 09:50]
In Vats, a schoolboy was charged with hacking the website of the Ministry of Education of the Novosibirsk region.
Studying remotely, a student of the final class of a secondary school decided to please his classmates by disrupting the lessons by blocking the school resource.
https://www.securitylab.ru/news/515197.php
SecurityLab, [31.12.20 13:48]
The year 2020 has become a real test for the whole world, the consequences of which will remain with us for a long time.
Nevertheless, everything tends to end, and very soon we will meet the new year, 2021, which, we hope, will become more calm both in the field of information security and in other aspects of our lives.
Happy New Year and Merry Christmas, take care of yourself!
https://www.securitylab.ru/news/515196.php
SecurityLab, [31.12.20 19:45]
The leadership of the Special Purpose Center for Traffic Safety of the Ministry of Internal Affairs for three years collected secret data on the routes of the first persons of Russia through WhatsApp chats.
This was told to the BBC by two former and one current employee of the Center.
Among the objects of state security, which are accompanied by a special battalion, are the president, Prime Minister, Chairman of the Federation Council, the leadership of the Security Council, the FSB, and leaders of foreign states.
https://www.securitylab.ru/news/515198.php
SecurityLab, [01.01.21 08:40]
“Solorigate” Fallout: Microsoft has accused Russian hackers of seizing the source code of its programs.
The American company announced this in its blog on Thursday, December 31.
“Our investigation into our own environment has found no evidence of access to production services or customer data. The investigation, which is ongoing, has also found no indications that our systems were used to attack others… This activity has not put at risk the security of our services or any customer data, but we want to be transparent and share what we’re learning as we combat what we believe is a very sophisticated nation-state actor.” (src: blog.microsoft.com)
Details: The company is one of the clients of SolarWinds, whose systems were hacked by hackers at the end of 2020. On December 17, Microsoft representatives admitted that malicious SolarWinds code was detected in its ecosystem, which was then isolated and deleted.
On December 31, Microsoft clarified that an ongoing investigation revealed unusual activity related to a small number of internal accounts. The company’s experts reported that one account was used to view program code in a number of repositories.
“This account did not have permission to change any code or technical systems, and during the investigation, we found out that there were no changes,” Microsoft explained. In addition, there is no evidence of unauthorized access to personal data of customers.
https://www.securitylab.ru/news/515199.php
“A key action is implementing a Zero Trust architecture. In this approach, companies must assume all activity—
related links: https://docs.microsoft.com/en-us/security/compass/compass (M$ per default blocks access from tor networks)
SecurityLab, [02.01.21 10:01]
“The Spying Power Bank” – illegal in Russia!
The spy device contains a GPS module with a SIM card.
Thanks to this, you can also track the movement of the owner of the battery.
The device also has a sensitive microphone.
On such a portable battery, you can call at any time and hear the conversations around it.
The devices have the function of automatically enabling the recording of conversations with noise above 50 dB, which corresponds to the average volume of a person’s conversation.
After recording, the device automatically sends the data to the attackers via the built – in cellular modem.
Details: Chinese police conducted several raids, during which about 2 thousand portable chargers were seized. It is still unknown how many such “spy gadgets” are still on sale, as they cannot be distinguished from conventional external batteries.
Although such devices are available for free sale, in the territory of the Russian Federation, the purchase or use of such devices may result in a penalty under 138.1 of the criminal code of the Russian Federation.
A year ago, the state Duma of the Russian Federation made it clear to detect spyware devices. Articles of the criminal code and administrative Code exclude ” freely available devices, systems, complexes, devices, and household appliances that have the functions of audio recording, video recording, photo recording, and / or geolocation, with openly located controls on them.”
https://www.securitylab.ru/news/515200.php
SecurityLab, [02.01.21 15:10]
More than 100,000 ZyXEL firewalls and VPN gateways contain a built-in backdoor
The devices have a hardwired zyfwp account with an immutable password.
A remote attacker who is not authenticated can access the affected system via ssh or a web interface using hard-coded credentials and gain administrator privileges.
The vulnerability received a maximum of 10 points on the CVSS hazard rating scale.
$ ssh zyfwp@192.168.1.252
Password: Pr*******Xp
Router> show users current
No: 1
Name: zyfwp
Type: admin
(…)
Router>
Details: According To a ZyXEL representative, the account is not associated with any malicious activity, but was only used to deliver automatic firmware updates via FTP
Zyxel recommends that you install the appropriate updates immediately.
The vulnerability affects many popular Zyxel products from the line of business-class devices that are usually deployed in private corporate and public networks.
This includes the following devices:
- a series of Advanced Threat Protection (ATP) is used mainly as a firewall
- unified Security Gateway (USG) series-used as a hybrid firewall and VPN gateway
- USG FLEX series-used as a hybrid firewall and VPN gateway
- VPN series – used as a VPN gateway
- NXC series – used as a WLAN access point controller
Zyxel was informed of the issue at the end of November and partially fixed the vulnerability on December 18.
The vulnerability is fixed in the ZLD V4.60 Patch1 firmware, and for the nxc2500 and NXC5500 access point controllers, a fix will be released in April 2021.
Security experts warn that any attacker, from DDoS botnet operators to state-sponsored hacker groups and ransomware gangs, can use this built-in account to access vulnerable devices and further break into internal networks.
The problem is compounded by the fact that the VPN service and the web interface for managing the device use port 443 by default, which is why many users left port 443 open for external requests and, thus, in addition to the VPN connection point, left the ability to log in to the web interface.
According to preliminary estimates, more than 100,000 vulnerable devices with an open port 443 are available on the network.
Last year, Zyxel fixed a critical vulnerability in its network attached storage (NAS) systems that is already being exploited by cybercriminals in real-world attacks.
Vulnerability CVE-2020-9054 allowed an unauthorized attacker to remotely execute arbitrary code.
This allows an attacker to exploit the vulnerability by including certain characters in the user name and embed commands with web server privileges.
Then, using the device’s built-in setuid utility, it can run commands with superuser privileges.
https://www.securitylab.ru/news/515201.php
SecurityLab, [03.01.21 16:45]
The cyberattack by “Russian hackers ” on the resources of the US government, which was first reported in mid-December, affected at least 250 federal agents and businesses, the NYT reports, citing sources in US intelligence.
According to the publication, the recent series of hacks turned out to be more extensive than expected.
https://www.securitylab.ru/news/515204.php
SecurityLab, [04.01.21 13:29]
A London court on Monday, January 4, rejected a US request for the extradition of Wikileaks founder Julian Assange.
This decision can be appealed by the lawyers of the American side.
The US extradition request was rejected due to concerns about Assange’s mental health, the court said.
https://www.securitylab.ru/news/515228.php
SecurityLab, [04.01.21 16:55]
The browser will constantly check the information with databases of information about declassified usernames and passwords.
Continuous monitoring of passwords will allow users to receive information in case of detection of activity by cyber-scammers.
Following this, device owners will receive tips to change sensitive data in order to maintain a high level of security.
The passwords in this case must be synchronized with the Microsoft account.
https://www.securitylab.ru/news/515233.php
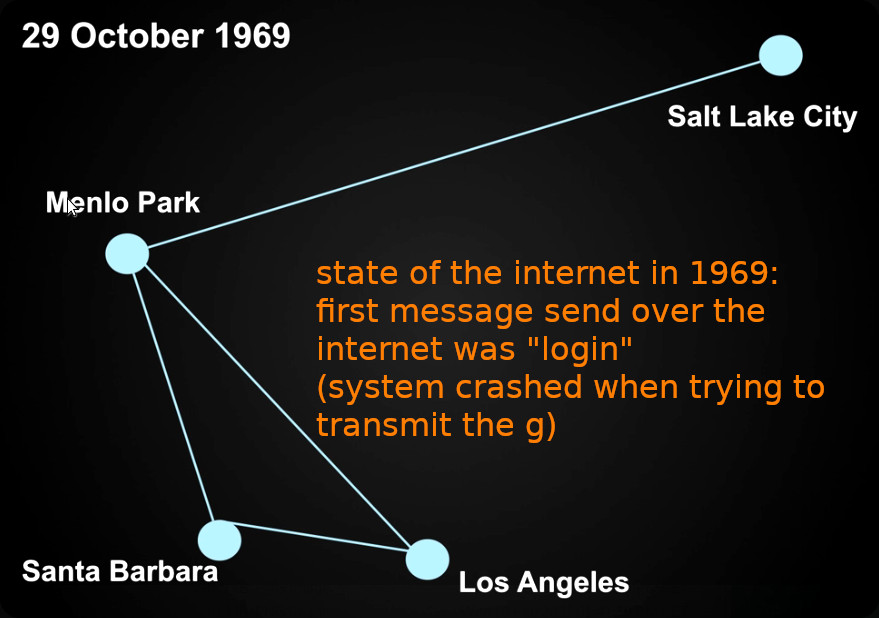
history of the internet
SecurityLab, [05.01.21 08:55]
Sending a simple letter will cost 0.42 Belarusian rubles (12 Russian rubles), and a registered one 1.5 rubles (43 rubles), the official website of the Ministry of Communications of Belarus says.
https://www.securitylab.ru/news/515241.php
“Teleportation Systems Toward a Quantum Internet”
https://authors.library.caltech.edu/106299/
“will bring incredible and unexpected benefits much as todays internet has already done” (src: Youtube)
SecurityLab, [05.01.21 15:30]
Scientists at the Fermi National Accelerator Laboratory – a U.S. Department of Energy national laboratory affiliated with the University of Chicago, together with partners from five institutions, have taken a significant step toward implementing the quantum Internet.
Scientists are moving closer to making an ultra-secure and ultra-fast quantum Internet possible: they can now “teleport” quantum information with high accuracy over a total distance of 44 kilometers.
“We are thrilled with these results. This is a key achievement on the way to creating a technology that will redefine the development of global communication, ” says physicist Panagiotis Spentsouris of the Fermilab particle physics and accelerator laboratory, based at the California Institute of technology (Caltech).
Both data transmission accuracy and transmission distance are critical when it comes to creating a real, working quantum Internet. Making progress in any of these areas is a cause for rejoicing.
https://www.securitylab.ru/news/515254.php
“We are very proud to have achieved this milestone on sustainable, high-performing, and scalable quantum teleportation systems,” says Maria Spiropulu, the Shang-Yi Ch’en Professor of Physics at Caltech and director of the research program. “The results will be further improved with system upgrades we are expecting to complete by Q2 [second quarter of] 2021.”
In a quantum internet, information stored in qubits (the quantum equivalent of computer bits) is shuttled, or teleported, over long distances through entanglement, a phenomenon in which particles become intrinsically linked to each other even when separated by vast distances. A key feature of quantum networks is their fidelity, or the quality of teleportation, which characterizes how close the teleported qubit is to the original. In the new study, quantum teleportation was performed with a fidelity of more than 90 percent.
“This high fidelity is important especially in the case of quantum networks designed to connect advanced quantum devices, including quantum sensors,” explains Spiropulu.
src: https://www.caltech.edu/about/news/quantum-internet-tested-caltech-and-fermilab
related links: https://inqnet.caltech.edu/Press-PRXQ-dec142020.html
comment: Except for Elon Musk & Starlink, if the Quantum-internet-access-point becomes available, it could render it’s Stalink sattelite constellation (that already started beta operations and will be available also in Europe at the end of 2021) worthless.
China’s Social Credit System
SecurityLab, [06.01.21 07:32]
Law-abiding, honesty, even consumer behavior – the most different aspects of a citizen’s life are tracked by the Chinese Social rating System.
In China, since 01.01.2021, a new civil code has been adopted, officially legalizing the “Social Credit System”.
The essence of the idea of Chinese specialists, who carefully studied foreign experience in this field, was to give the inhabitants of the conditional city N a certain amount of points.
This initial amount, which guaranteed all residents equal starting conditions, could either grow or decrease – depending on what the owner of a kind of “wallet” did useful or harmful.
A similar system applies in respect of legal entities of the company to check on compliance with environmental legal requirements.
The conditions and safety of work at enterprises and their financial statements are also evaluated.
Now every citizen has a starting rating of 1000 points.
A single information center analyzes each of 160,000 different parameters from 142 institutions.
If the rating is more than 1050 points, then you are an exemplary citizen and are marked with the AAA index.
With 1000 points, you can count on A+, and with 900 on B.
If the rating has fallen below 849 – you are already a suspicious carrier of category C,
which can easily be dismissed from state and municipal structures.
Those with 599 points and below fall into group D, this is comparable to a ”black mark”, since they will not be hired even as a taxi driver.
https://www.securitylab.ru/news/515268.php
SecurityLab, [06.01.21 09:30]
The Federal Bureau of Investigation (FBI), the US-Cybersecurity and Infrastructure Protection Agency (CISA) and the US-Intelligence Community (ODNI) have admitted Russia’s involvement in a hacker attack on US federal agencies.
The conclusions are given in a joint statement of the special services.
https://www.securitylab.ru/news/515269.php
SecurityLab, [06.01.21 16:55]
On February 8, the popular WhatsApp messenger will enter into force new Terms of Use.
Developers are already preparing for the transition and will soon start collecting permissions from users.
https://www.securitylab.ru/news/515279.php
SecurityLab, [06.01.21 17:20]
The Telegram messenger provides users with the “People nearby” function, thanks to which you can determine the location of the client of the social network with an accuracy of several tens of meters.
https://www.securitylab.ru/news/515280.php
SecurityLab, [07.01.21 09:05]
The researchers calculated that there was no Internet access in Belarus for 218 hours.
The outages affected 7.9 million users to one degree or another.
https://www.securitylab.ru/news/515286.php
SecurityLab, [07.01.21 12:10]
The current President of the United States, Donald Trump, posted on social networks an appeal to the nation and a statement that the storming of the Capitol was the result of the “theft” of his election victory.
Immediately after the publication, Twitter froze the account of the US president for 12 hours and threatened to permanently block it if it does not delete messages that violate the rules of the resource.
Currently, Trump has eliminated violations on his Twitter page, because of which his account was blocked, according to Bloomberg journalist Kurt Wagner.
https://www.securitylab.ru/news/515288.php
SecurityLab, [08.01.21 03:05]
According to preliminary information, hackers gained access to 3% of electronic mailboxes.
Details: The US Department of justice (DOJ) believes that part of the email correspondence of its employees received unauthorized access by hackers who previously attacked us government departments and companies.
This is stated in the statement of the Ministry.
“This activity included getting access to Microsoft Office 365 mail.
Upon learning of the malicious activity, the Office of the Director of information technology eliminated the established method by which the subject obtained access to Office 365 mail…
the Number of mailboxes that were potentially accessed is limited to approximately 3%, and we have no evidence that any secret systems were affected,” the statement notes.
https://www.securitylab.ru/news/515320.php
SecurityLab, [08.01.21 08:55]
“A Russian who admitted carrying out one of the largest known cyberattacks against a U.S. bank is a “brazen and prolific” hacker who should serve as long as almost two decades in prison, U.S. prosecutors told a federal judge in advance of his sentencing.
Andrei Tyurin pleaded guilty in September 2019 to charges that he stole data on more than 80 million clients of JPMorgan Chase & Co. and other institutions as part of a scheme that netted hundreds of millions of dollars in ill-gotten gains.”
(src: Bloomberg)
(Andrei) Tyurin was found guilty on several counts.
Ultimately, Judge Laura Swain, who handled the case, upheld the prosecution and handed down a sentence that would see Tyurin spend 144 months in an American prison.
As she believes, Tyurin was involved in”large-scale criminal activity of a financial nature.”
He is allegedly involved in cyber attacks on large American companies in order to obtain “customer data”.
In addition, the Russian must pay the United States $19,214,956, which is exactly the profit that the court believes he was able to extract during his criminal activities.
A separate hearing on damages is scheduled for April 6, 2021.
“The conditions of the Russian’s detention were difficult in the context of the COVID-19 pandemic, which A. Tyurin contracted in an American prison.
The Russian Consulate General in New York is monitoring the Tyurin case and is in contact with US law enforcement agencies,” the consulate said.
https://www.securitylab.ru/news/515321.php
SecurityLab, [08.01.21 11:36]
The manufacturer of tools for the development of JetBrains was interested in the FBI, The New York Times (NYT) reported.
The security services have not yet made specific charges.
A company with Russian roots is being tested for whether its products could have been used in the hacking of the American SolarWinds.
It is now considered the “entry point” of a large-scale hacker attack.
According to the NYT, the FBI and private cybersecurity researchers have begun looking into the role of JetBrains in a major hack of SolarWinds.
The article says that among the clients of JetBrains, 79 companies from the Fortune 100 list, and in general, 300 thousand organizations use the company’s software.
Among them was SolarWinds, with which the hacking began.
https://www.securitylab.ru/news/515319.php
SecurityLab, [08.01.21 15:25]
The storming of the US Congress building in Washington, among other things, may pose a threat to cybersecurity, experts say.
On Wednesday, January 6, supporters of Donald Trump broke into the Capitol building, where the US Congress is located, in order to disrupt the confirmation of Joe Biden as the 46th US president.
At least 50 people were arrested after using Molotov cocktails, improvised explosives and weapons.
As a result of the storming of the Capitol, at least five people were killed.
According to The Independent, the protesters gained access to at least one computer system in the office of Congressional Speaker Nancy Pelosi.
There are serious concerns about the fact that the attackers were able to compromise the entire digital infrastructure of Congress.
As reported in a tweet (now deleted), The Blaze employee Elijah Schaffer (Elijah Schaffer), he managed to get into Pelosi’s office along with other protesters who broke into the building.
The image he posted shows a computer monitor with an email client open on the screen and emails dated 2019.
Since Capitol employees left their computers, laptops, and mobile devices unattended during the emergency evacuation, attackers could also gain access to them.
https://www.securitylab.ru/news/515322.php
comment: so next time use GNU Linux OS with encrypted partitions and instruct the IT-team to remote-shutdown all systems before the next wave of Trump-rioters attacks with bootable USB-sticks (who knows).
SecurityLab, [08.01.21 15:50]
The text of the document is divided into three parts: applications for smartphones, programs for laptops and desktop computers, and services for SMART TV-enabled TVs.
https://www.securitylab.ru/news/515327.php
SecurityLab, [09.01.21 08:10]
Pavel Durov spoke about the flight of users from the WhatsApp messenger to Telegram, which he founded.
In his opinion, this was caused by the new policy of the WhatsApp service regarding Facebook, he wrote in his Telegram channel.
https://www.securitylab.ru/news/515335.php
SecurityLab, [09.01.21 10:40]
This article will explain how to configure a GNU Linux server with the vulnerabilities discussed in the previous four parts of this series, so that you can work out all the proposed techniques at home.
As usual, the article is intended for those who are just starting to learn penetration testing.
In addition, I hope that everyone else will be able to learn something new for themselves.
https://www.securitylab.ru/analytics/515337.php
SecurityLab, [09.01.21 11:15]
Shadow on the forum there was an announcement about the sale of a database containing the data of 1.3 million registered users hyundai.ru.
According to the seller, the database contains full information: full name, phone numbers (home, work, mobile), address, email. e-mail the data of the car (make, VIN number), etc. the Base is available in SQL-format dump.
https://www.securitylab.ru/news/515340.php
SecurityLab, [10.01.21 06:30]
In the statement, which was distributed by a Google representative, in particular, it is stated that Parler (social network) was previously warned about the inadmissibility of posting content that provokes violence, and that the application will not be allowed in Google Play until it changes the moderation policy.
The social network is accused of being used by supporters of Donald Trump to coordinate the protests that ended with the storming of the Capitol building.
During the riots, five people were killed, including a police officer.
SecurityLab, [10.01.21 14:14]
The source code of the ChastityLock ransomware, which is used to carry out attacks on users of the “smart” Bluetooth lock of male chastity, is now published in the public domain for research purposes.
We are talking about the Cellmate Chastity Cage device from the Chinese company Qiui, which is a modern analogue of the medieval chastity belt, which can be controlled (blocked and unlocked) using a mobile application.
However, as experts from Pen Test Partners found out, the application has vulnerabilities that allow anyone to remotely block the gadget.
Users of Qiui Cellmate men’s chastity belts last year fell victim to cyberattacks using the ChastityLock malware after security researchers discovered a vulnerability in the device that allowed it to be blocked remotely.
https://www.securitylab.ru/news/515347.php
SecurityLab, [10.01.21 17:37]
Wi-Fi 6E will be the largest improvement to the Wi-Fi standard in recent decades.
Some devices with its support can be presented at the virtual event CES 2021.
The publication writes that “the upcoming Wi-Fi update, in fact, is similar to the transition from a two-lane road to an eight-lane highway.”
https://www.securitylab.ru/news/515348.php
SecurityLab, [11.01.21 09:01]
US Secretary of State Mike Pompeo announced plans to create a new structure within the State Department that will deal with cybersecurity issues in the framework of US foreign policy.
The new structure will be called the Bureau of Cyberspace Security and Emerging Technologies (CSET).
“The CSET Office will lead the U.S. government’s diplomatic efforts to address a wide range of international cyberspace security issues and regulatory challenges to emerging new technologies affecting U.S. foreign policy and national security, including securing cyberspace and critical technologies, reducing the likelihood of cyber conflicts, and prevailing in strategic cyber competition,” the U.S. State Department said in a statement.
https://www.securitylab.ru/news/515350.php
SecurityLab, [11.01.21 09:45]
In 2021, Microsoft plans to add a number of new interesting features to Windows 10 and its other products.
Details:
Microsoft does not intend to release Windows 11, but instead will add new features, improvements, and fixes to Windows 10.
the company will continue to develop Surface products running Windows 10, as well as Windows on ARM and Windows 10X.
- Windows 10 21H1
This year’s first update for Windows 10 was codenamed Windows 10 21H1.
Build 19043 is expected to be released in the spring.
Unlike last year’s may update, Windows 10 21H1 will be a minor release with quality improvements, bug fixes, and enhanced security for enterprise customers.
- Windows 10X
After Windows 10 21H1, the company plans to release the long-awaited modular Windows 10x operating system, originally designed for dual-screen devices.
While the release of an optimized version of Windows 10X for dual-screen products is currently on hold, Microsoft is trying to get Windows 10X to work on single-screen devices.
The OS is expected to be released in spring 2021.
- Windows 10 21H2 «Sun Valley»
After Windows 10 21H1 and 10X, the 21H2 update for Windows 10 will be released.
In accordance with the standard Microsoft release schedule, the update should be released in the fall of 2021.
The novelty will receive an updated user interface codenamed “Sun Valley”. The update will be full-fledged, with many improvements to the start menu, taskbar, and so on.
- Cloud PC
Microsoft is currently developing a new virtualization product called Cloud PC, which allows business customers to run their personal PCs in the cloud and access them remotely from other devices.
Most likely, Cloud PC will become part of Microsoft’s advertised “Windows as a Service” experience.
Cloud PC will not replace any existing services and will be offered as a paid service for enterprise customers who want to access their Windows PC from anywhere at any time.
- Support for Android apps
There are reports Online that Microsoft is working on creating an Android subsystem for Windows 10 in order to provide support for Android applications.
In addition, the company is creating a new development tool that allows you to distribute Android applications as MSIX packages through the Microsoft app store.
- Microsoft Surface Products
Microsoft intends to expand its Surface line by adding two new products-Surface Pro 8 and Surface Laptop 4.
The Surface Pro 8 (2021) will use an Intel Tiger Lake processor, while the Surface Laptop 4 will use both Intel and AMD processors (Intel Tiger Lake – U and AMD Ryzen 4000).
Surface Pro 8 will get 32 GB of RAM and 1 TB of internal SSD storage.
According to a survey conducted by the British organization Which?
https://www.which.co.uk/news/2021/01/1-in-10-computer-users-windows-7/
13% of users still work with Windows 7 and do not want to switch to Windows 10.
The main reasons for not wanting to upgrade to the new OS are as follows:
- unwillingness to pay for an upgrade (30%)
- ease of use of Windows 7 (22%)
- incompatibility of Windows 10 with devices (16%)
https://www.securitylab.ru/news/515354.php
SecurityLab, [11.01.21 10:40]
As a result of the hacking of SolarWinds, classified US court documents were leaked, which can have a huge impact on the sanctions imposed by the US against so-called “state” hackers.
https://www.securitylab.ru/news/515357.php
SecurityLab, [11.01.21 12:10]
Apple and Google pose a much greater threat to user freedoms than Twitter.
And Apple is more dangerous than Google, “because it has complete control” over which apps users can install and which they can’t.
Unlike Apple, you can install apps on Android via apk files.
They retain access to the free flow of information.
https://www.securitylab.ru/news/515368.php
SecurityLab, [11.01.21 19:40]
Hackers broke into the IT systems of US government agencies using tools used by the Russian cybercrime group Turla.
This is stated in a study by Kaspersky Lab.
The Estonian Foreign Intelligence Service believes that the members of this group work for the FSB of the Russian Federation.
Details: Hackers broke into the IT systems of US government agencies using tools used by the Russian cybercrime group Turla.
This is stated in a study by Kaspersky lab.
The Estonian foreign intelligence service believes that members of this group work for the FSB of the Russian Federation.
Kaspersky Lab analysts compared the Sunburst hacking tool used during this attack with the already well-known Kazuar tool used by the Turla hacker group, which many experts associate with Russia, and found similarities in their code.
The tools used to make both parts of the Sunburst malware invisible were similar, as well as methods for detecting potential victims.
The formulas used by attackers to calculate the time when viruses were in “sleep” mode in order to avoid detection were almost identical.
“One such conclusion could be rejected. Two coincidences make me raise an eyebrow. Three is more than a coincidence,” said one of the authors of the study, Kostin raiu.
The cyberattack, dubbed Sunburst, became known in late December.
Malicious code was hidden in software updates of the it company SolarWinds.
According to reports, the attack lasted several months and was the longest and largest in the history of the United States.
https://www.securitylab.ru/news/515385.php
SecurityLab, [12.01.21 06:55]
The Telegram messenger was downloaded more than 545,000 times from Wednesday to Sunday, which is three times more than the number of downloads for the same period in the previous week.
The increase in popularity is associated with the blocking of Donald Trump’s accounts in social networks and the shutdown of the social network Parler, which is popular among supporters of the US president.
Another reason for the growth of the messenger’s popularity was the new WhatsApp privacy policy, according to which the application will collect user data for the Facebook family of applications.
Durov, after changing the privacy policy of WhatsApp, said about the accelerated “flight” of users to Telegram.
According to him, at the same time, paid bots appeared, which began to publish fakes about Telegram and “biased information” about WhatsApp.
https://www.securitylab.ru/news/515387.php
SecurityLab, [12.01.21 09:35]
Microsoft has released the next version of its Sysmon 13 utility, which has received a new security feature that detects interference in Windows processes using the process hollowing and process herpaderping methods.
https://www.securitylab.ru/news/515390.php
SecurityLab, [12.01.21 10:15]
Intel Corporation announced at CES 2021 the introduction of hardware detection of ransomware in the recently announced Core vPro business class processors of the 11th generation.
https://www.securitylab.ru/news/515391.php
Google’s “Gaming as a Service”
about: https://sharestadia.com/what-is-google-stadia/
“gaming in the cloud” not gonna happen without fast internet:
The internet speed requirements for the different types of picture quality from Stadia’s service is as follows:[15][16]
| Bandwidth required | Video quality | Audio quality |
|---|---|---|
| 10 Mbit/s | 720p, 60 FPS | Stereo |
| 20 Mbit/s | 1080p HDR Video, 60 FPS | 5.1 Surround |
| 35 Mbit/s | 4K HDR Video, 60 FPS | 5.1 Surround |
(src: Wiki)
SecurityLab, [12.01.21 10:25]
Google’s new Stadia service uses the Chrome ecosystem to deliver streaming PC games to mobile devices, TVs, and web browsers.
Although not mandatory, the company even offers a dedicated Stadia controller that connects directly to streaming servers over Wi-Fi to reduce system latency.
The controller is equipped with a tiny microphone to interact with the voice assistant.
https://www.securitylab.ru/news/515392.php
Stadia is built on Debian Linux servers and Vulkan is their graphics API.[20][21]
“This [Stadia] starts with our platform foundations of GNU Linux and Vulkan and shows in our selection of GPUs that have open-source drivers and tools. We’re integrating LLVM and DirectX Shader Compiler to ensure you get great features and performance from our compilers and debuggers.”[20]
— Dov Zimring, Stadia Developer Platform Lead
liked this article?
- only together we can create a truly free world
- plz support dwaves to keep it up & running!
- (yes the info on the internet is (mostly) free but beer is still not free (still have to work on that))
- really really hate advertisement
- contribute: whenever a solution was found, blog about it for others to find!
- talk about, recommend & link to this blog and articles
- thanks to all who contribute!