Pwn2Own 2020: opening a pdf can be enough to compromise system!
https://youtu.be/u1udr7j9MQA?t=359
thank you ccc you are doing a lovely work – make this planet more interesting by creativity and more informed about security 🙂 keep it up 🙂
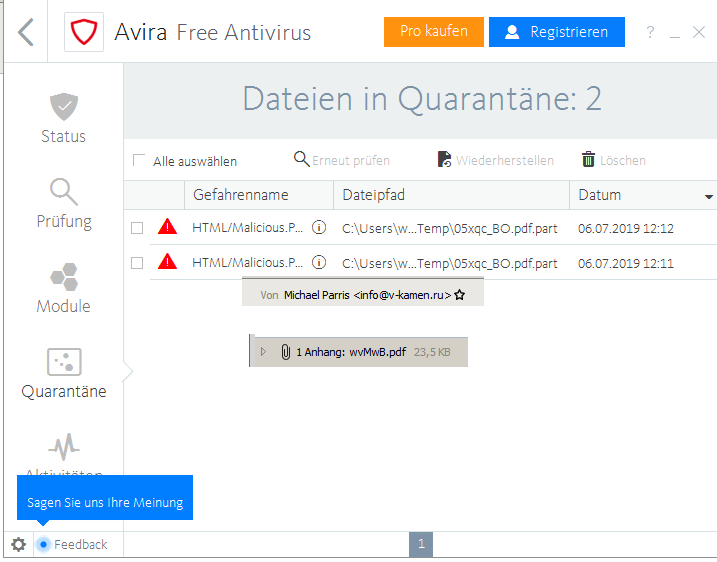
today i discovered a mail at my client from domain v-kamen.ru with ip 185.143.173.176 (St Petersburg, Russia… but who knows who controls this server/computer? maybe the Russians maybe the Chinese maybe the Americans… we don’t know and no fast finger pointing here please)
which did not contain a lot of text, just a wvMwB.pdf
you can have the original file here: pwd for encrypted.rar is: evil
https://dwaves.de/software/evil/2019-07-06-evil.pdf.rar
sha512sum is: 5f2e55464a2af6fcb5e59ac8eb068b869118b4e2ead62247ed9c7358497bf38bfb5da452df50cb880b38e7773aea406cd6eb36bd7f07f67fa5e1f6a1ef75eebe
screenshot:
this time i was lucky, the virus scanner detected evil in the PDF before it could trigger / cause any problems.
also it is a virtual machine that i just took a powered down snapshot off, so i can reset to this state.
it just shows…. if vendors implement too much features (that probably 99% of all users never use) they increase the attack surface for hackers and put everyone at risk that uses their products.
SaneSecurity names this virus: Sanesecurity.Malware.27643.PDFHeur.IP.UNOFFICIAL
which means it’s heuristic detected something bad… but there is no signature? GREAT.
This will happen more often in the future, because virus-spammers will just generate an “unique” virus for every mail they send.
Simply relying on AntiVirus IS NOT ENOUGH ANYMORE (since about 10 years).
is PDF a save format/a format you can (still) trust?
can you trust PDF files?
no, but PDFs are “generally” more trusted than any other attachments and a lot of people use it as a default format to exchange documents – because – unlike word-stupid.doc(x) and excel.xls(x) they can not contain makros BUT it is said (thanks Adobe) PDF can contain JAVASCRIPT!
But what else can they contain? Can evil code/runnable binaries be embedded into PDF?
PDFs SHOULD consist of xml-style text and pictures.
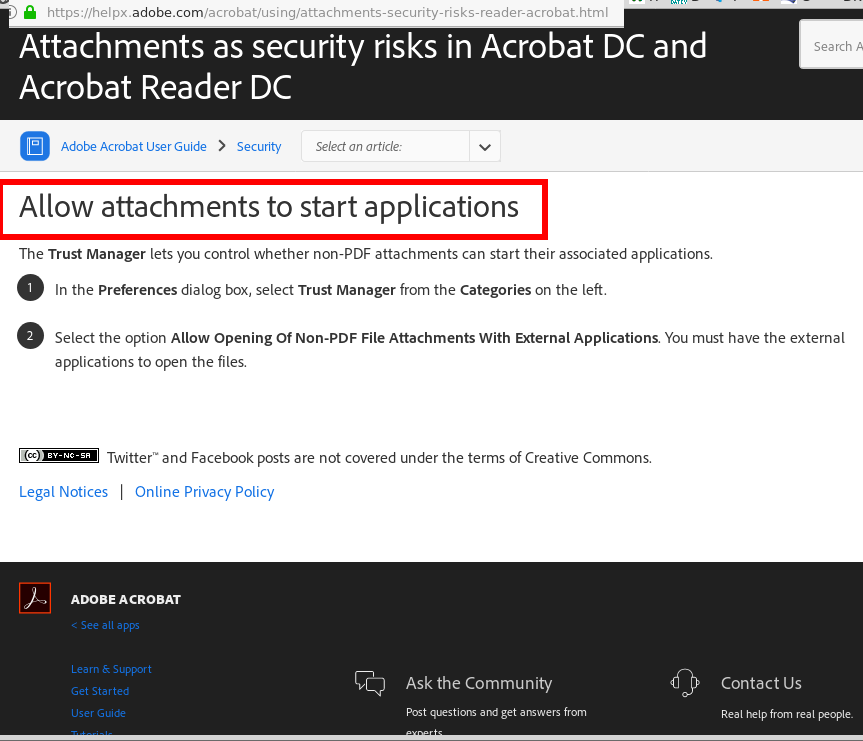
that might be a mistake, because Adobe allows to include other formats / files to be included into their PDFs. (BIG MISTAKE!)
“The Portable Document Format (PDF) (redundantly: PDF format) is a file format developed by Adobe in the 1990s to present documents, including text formatting and images, in a manner independent of application software, hardware, and operating systems.[2][3] Based on the PostScript language, each PDF file encapsulates a complete description of a fixed-layout flat document, including the text, fonts, vector graphics, raster images and other information needed to display it. PDF was standardized as an open format, ISO 32000, in 2008, and no longer requires any royalties for its implementation.[4]
Today, PDF files may contain a variety of content besides flat text and graphics including logical structuring elements, interactive elements such as annotations and form-fields, layers, rich media (including video content) and three dimensional objects using U3D or PRC, and various other data formats.”
What besides udpates that nobody installs on time – does Adobe do to mitigate the threat?
Adobe is a respected company – and i loved the AS 3.0 Flex Builder (not the later versions) BUT Shockwave Flash Browser plugin (almost like Java Virtual Machine) introduces a lot of security problems to your system to the point that you simply CAN NOT trust Flash.swf files from any source – basically making it necessary to while-list your internet access to the only trusted IPs. (and if those get hacked you are screwed)
WHY ON EARTH WOULD A PRINTER (PostScript PDF was designed for PRINTERS!) WOULD WANT TO START AN EXTERNAL APPLICATIONS?
SERIOUSLY? (unless it is a corrupt and evil one… or it has developed AI of it’s own and gone rogue)
NO SERIOUSLY ADOBE WITH ALLOWING SUCH NON SENSE YOU PUT THE WHOLE WORLD THAT USES YOUR FORMATS AT RISK!
LESS FEATURES!
MORE SECURITY PLEASE!
THANK YOU!
https://helpx.adobe.com/acrobat/using/attachments-security-risks-reader-acrobat.html
complete mail source:
Return-path: <SRS0=wJveLSrJ=QF=v-kamen.ru=mail@receiver.com> Envelope-to: mail@receiver.com Delivery-date: Tue, 29 Jan 2019 02:40:37 +0100 Received: from [185.143.173.176] (helo=v-kamen.ru) by www314.your-server.de (envelope-from <info@v-kamen.ru>) id 1goIO7-0001t7-RT for mail@receiver.com; Tue, 29 Jan 2019 02:40:37 +0100 DKIM-Signature: v=1; a=rsa-sha1; c=relaxed/relaxed; s=mail; d=v-kamen.ru; h=Message-ID:From:To:Subject:Date:MIME-Version:Content-Type; bh=IOMPXUQiGPg8SauCb5SSycecNQY=; b=uJ/MdgtWVD3uikR+x+04KD2eDlvVyem12xJSVeATUvpTXQQa7vKga2i8JA8LxhI7Po6LaB/BjYqU MTBvAiBFE7jYHPQa6CgKpS08PWXv9fOkcKpBuRXFi4Rs9pXq2AN4kDjy6UDzV5JKS7uwH7arMDRd GwgSsGA7PVOlMKTDYwsjmxRYIZdzo6HzHIs4nqttrOVxRLcUxnyrnVKPxzR/Ava44zccwuJthJqp rVFZ/ng0Q6a1iH6K6Rj7Djzx6Y3yv46sWnxhEh2wiHOCAPlE0aoFsDhvDCf3oCy6U3ythYNCZ19z Pq+Z8+tiDEGMpxDPLipRYuiOwdCvwDd9YN3ECQ== Message-ID: <825d1498bac9e3ea5653e549afab8195eb612f@v-kamen.ru> From: "Michael Parris" <info@v-kamen.ru> To: <mail@receiver.com> Subject: Nguyen Manh Thang Date: Tue, 29 Jan 2019 04:40:19 +0300 MIME-Version: 1.0 Content-Type: multipart/mixed; boundary="8b71186231e5ca598580c9775387b57def7f" X-DKIM-Status: pass [(v-kamen.ru) - 185.143.173.176] X-Virus-Scanned: Clear (ClamAV 0.100.2/25339/Mon Jan 28 19:32:47 2019) X-Spam-Score: 0.9 (/) Delivered-To: mail@receiver.com --8b71186231e5ca598580c9775387b57def7f Content-Type: multipart/alternative; boundary="aa723bb795e6ccc5797cca668084aebabce733" --aa723bb795e6ccc5797cca668084aebabce733 Content-Type: text/plain; charset="utf-8" Content-Transfer-Encoding: quoted-printable MD Shahjahan Mallick --aa723bb795e6ccc5797cca668084aebabce733 Content-Type: text/html; charset="utf-8" Content-Transfer-Encoding: quoted-printable
--aa723bb795e6ccc5797cca668084aebabce733-- --8b71186231e5ca598580c9775387b57def7f Content-Type: application/octet-stream; name="wvMwB.pdf" Content-Transfer-Encoding: base64 Content-Disposition: attachment; filename="wvMwB.pdf".... MDAwMDE3MTUgMDAwMDAgbiAKMDAwMDAwMTg2MiAwMDAwMCBuIAowMDAwMDAyMDgzIDAwMDAwIG4g CjAwMDAwMDI0MzQgMDAwMDAgbiAKMDAwMDAwMjY5NCAwMDAwMCBuIAowMDAwMDAyODQ4IDAwMDAw IG4gCjAwMDAwMDMwNzQgMDAwMDAgbiAKMDAwMDAxMTQwOCAwMDAwMCBuIAp0cmFpbGVyCjw8Ci9J RFs8MTlERTgyNDMwRDE1NDk0RjkxNUVDQkQyNjJBQjBGQzQ+PDE5REU4MjQzMEQxNTQ5NEY5MTVF Q0JEMjYyQUIwRkM0Pl0KL0luZm8gMSAwIFIKL1Jvb3QgMiAwIFIKL1NpemUgMTgKPj4Kc3RhcnR4 cmVmCjIzNTU3CiUlRU9GCg== --8b71186231e5ca598580c9775387b57def7f--
whois 185.143.173.176 % This is the RIPE Database query service. % The objects are in RPSL format. % % The RIPE Database is subject to Terms and Conditions. % See http://www.ripe.net/db/support/db-terms-conditions.pdf % Note: this output has been filtered. % To receive output for a database update, use the "-B" flag. % Information related to '185.143.172.0 - 185.143.173.255' % Abuse contact for '185.143.172.0 - 185.143.173.255' is 'abuse@selectel.ru' inetnum: 185.143.172.0 - 185.143.173.255 netname: SELECTEL-NET descr: Selectel MSK country: RU admin-c: CMH-RIPE admin-c: KS9134-RIPE tech-c: SA32710-RIPE status: ASSIGNED PA remarks: mnt-by: MNT-SELECTEL created: 2016-05-23T13:16:19Z last-modified: 2017-04-17T17:13:30Z source: RIPE role: SELECTEL-NOC address: Russia, Saint-Petersburg, Cvetochnaya st. 21 admin-c: CMH-RIPE admin-c: KS9134-RIPE tech-c: CMH-RIPE tech-c: KS9134-RIPE nic-hdl: SA32710-RIPE mnt-by: mnt-selectel created: 2015-01-19T15:40:16Z last-modified: 2019-04-15T10:47:55Z source: RIPE # Filtered person: Cyrill Malevanov address: Selectel Ltd address: Cvetochnaya st. 21 address: 190000, Saint-Petersburg address: Russia phone: +78126778036 fax-no: +78126778036 nic-hdl: CMH-RIPE mnt-by: mnt-selectel created: 2005-10-24T12:00:08Z last-modified: 2015-01-19T15:37:28Z source: RIPE # Filtered person: Kirill Sizov address: 190000, Russia, Saint-Petersburg, Tsvetochnaya 21A phone: +78126778036 org: ORG-SL223-RIPE nic-hdl: KS9134-RIPE mnt-by: MNT-SELECTEL created: 2017-04-17T17:07:36Z last-modified: 2017-04-17T17:07:36Z source: RIPE # Filtered % Information related to '185.143.173.0/24AS50340' route: 185.143.173.0/24 descr: SELECTEL-NET-MSK origin: AS50340 mnt-by: MNT-SELECTEL created: 2018-07-03T09:20:01Z last-modified: 2018-07-03T09:20:01Z source: RIPE % This query was served by the RIPE Database Query Service version 1.94 (HEREFORD)
liked this article?
- only together we can create a truly free world
- plz support dwaves to keep it up & running!
- (yes the info on the internet is (mostly) free but beer is still not free (still have to work on that))
- really really hate advertisement
- contribute: whenever a solution was found, blog about it for others to find!
- talk about, recommend & link to this blog and articles
- thanks to all who contribute!