IPv6 is great for everything that is (more or less) DIRECTLY connected to the internet (needs a public accessible address):
- firewalls / routers
- modems
- servers (using firewalls / routers and modems to connect)
but it seems completely “overkill” and even dangerous to assign internet-clients such as laptops, SmartPhones and IoT-toasters with a public (!) accessible address.
it is NOT needed.
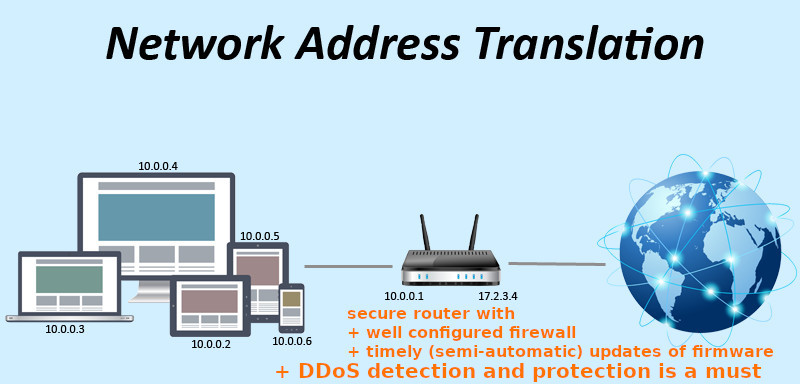
the user’s NAT-service of internet-router does it for the user (send and receive the traffic) while at the same time firewall-shielding the maybe not so-up-to-date SmartPhone firmware against direct-access and direct-attacks from the wild wild west public inet (of course does not protect against user downloading an malicious App or clicking a malicious link or downloading a malicious file, but a well configured firewall-router COULD to some extend protect even against that by whitelisting only trusted IPs/known-to-be-secure-servers).
the SmartHome case:
NAT works perfectly to multiply IPv4 address space into the billions, so ipv6 actually is not needed by IoT-Toaster if the user-admin is running them behind a NAT router, because: why would a IoT-Toaster need a globally unique ip address?
NAT has clear security advantages too, because
- the IoT-Toaster is shielded by the NAT-router’s security (firewall and timely updates)
- if the NAT-router’s security is bad (backdoors, outdated firmware), then it is probably best to not use the internet at all
- who on Earth (and other planets) would want their IoT-Toaster to be publicly accessible?
- (to remote control toaster?)
so it is probably security wise better to establish an (hopefully) very secure VPN or SSH tunnel with the NAT-router first, and then access all IoT-Toasters inside that network, than to let the non-existing firewall and non-existing updates of the IoT-Toasters try to survive in the digital public wild wild inet.
(can remember times… when internet-accessible directly to inet connected (via modem) Windows XP PCs would be Virus infected in less than 10 seconds)
IPv6 can and will be used to uniquely identify devices and users of devices even behind NAT aka mass surveillance, building perfect records of user’s lifes in order to manipulate.
the pro: less centralized? more scale and more speed?
“The IPv6 enabled nodes don’t need a central authority similar to IPv4 DHCP servers to configure their addresses.”
“They discover the networks they are in and complete the addresses themselves by generating the host part.”
“This makes the network configuration simpler and scales better to larger networks.”
“node needs to ensure that its address doesn’t collide.. other node on the network”
“Secondly, if the node uses the same host part of the address in every network it enters then its movement can be tracked and the privacy is at risk.”
“Internet Engineering Task Force (IETF), the organization behind the Internet standards, acknowledged this problem and recommends against use of hardware serial numbers to identify the node in the network.” (src)
so the ONLY advantage of IPv6 over IPv4 is speed of connection by eliminating routing hops.
has IPv6 build-in mechanisms to protect against DDoS?
no, IPv6 makes DDoS even worsse: why? more devices with outdated firmware and unique addresses = more DDoS bots = more powerful DDoS attacks
“With the growing popularity of IPv6 (Internet Protocol Version 6), so the possibility of this protocol providing a gateway for Distributed Denial of Service (DDoS) attacks has also increased.” (src)
What about that Security Extensions thingy build into GNU Linux? well look for it, it is hard to find X-D
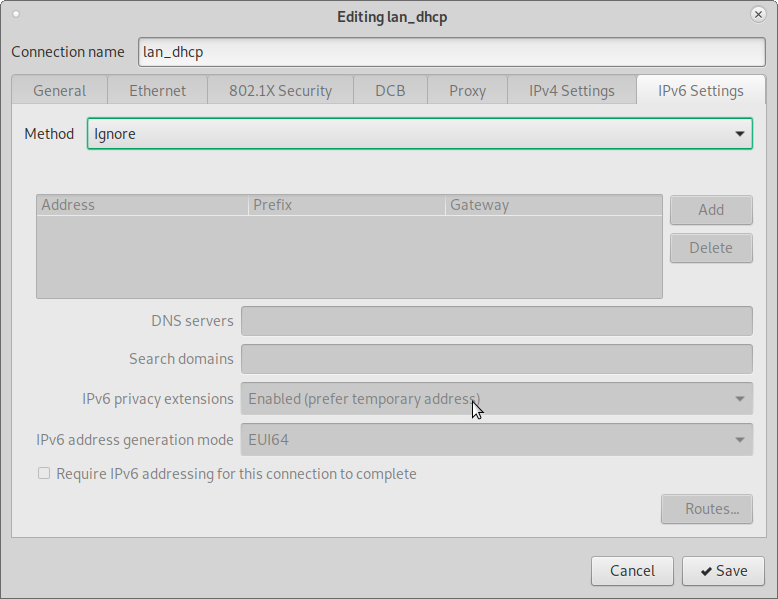
“With privacy extensions enabled, as defined by RFC4941, a new address with a random host part is generated every now and then.” (src)
gnome network manager SHOULD respect the user’s privacy per default and have privacy extension enabled per default: (double check!)
how to manually enable it: https://tldp.org/HOWTO/Linux+IPv6-HOWTO/ch06s05.html
How to turn off IPv6:
tested on GNU Linux Debian various versions:
# Append ipv6.disable=1 to the GRUB_CMDLINE_LINUX variable in vim /etc/default/grub GRUB_DEFAULT=0 GRUB_TIMEOUT=2 GRUB_DISTRIBUTOR=`lsb_release -i -s 2> /dev/null || echo Debian` # quiet can be removed to have more verbose output during boot GRUB_CMDLINE_LINUX_DEFAULT="quiet" GRUB_CMDLINE_LINUX="ipv6.disable=1" update-grub; # run Debian 8 and later update-grub2; # rpm based Fedora/CentOS/Redhat grub2-mkconfig -o /boot/grub2/grub.cfg # and reboot shutdown -r now # check if ipv4 only address is assigned su - root ifconfig
alternative:
edit
vim /etc/sysctl.conf
and add those parameters to kernel. Also be sure to add extra lines for other network interfaces you want to disable IPv6.
net.ipv6.conf.all.disable_ipv6 = 1 net.ipv6.conf.default.disable_ipv6 = 1 net.ipv6.conf.lo.disable_ipv6 = 1 net.ipv6.conf.eth0.disable_ipv6 = 1
After editing sysctl.conf, you should run
sysctl -p
to activate changes or reboot system.
BigBrother v6: “You’re being followed
“MAC addresses are unique, as in globally unique, as in the Ethernet interface in your computer has a MAC address that doesn’t exist anywhere else in the world.
If you have a wired and a wireless connection in your computer, your computer has two unique MAC addresses. This is partly why SLAAC works. By using an interface’s MAC address as part of its IPv6 address we ensure a unique IPv6 address is generated every time.
However, the problem with uniqueness is that it can also work as an identifier. When IPv6 was conceived in the mid-90s the Internet wasn’t composed of so many mobile devices like it is today. Also, the combination of the words ‘privacy’ and ‘computer’ weren’t as salient nor contentious as they are today.
Your mobile phone most likely has a MAC address, and will need an IPv6 address if it doesn’t already have one. If your operator is using SLAAC then you can be tracked using the last 48 bits of your IPv6 address because it’s unique. Websites that you visit can see that you have a new IP address, because you have roamed to a new operator, they can also see that the last 48 bits of the address stay the same every time. Hence, every website you visit will know your device regardless of what network you’re on. You can be easily tracked across providers.”
src: https://www.internetsociety.org/resources/deploy360/2014/privacy-extensions-for-ipv6-slaac/
liked this article?
- only together we can create a truly free world
- plz support dwaves to keep it up & running!
- (yes the info on the internet is (mostly) free but beer is still not free (still have to work on that))
- really really hate advertisement
- contribute: whenever a solution was found, blog about it for others to find!
- talk about, recommend & link to this blog and articles
- thanks to all who contribute!