if there are problems… run this one-liner… and ESPECIALLY with let’s encrypt… watch CAREFULLY…
- as not all errors might show up in a nice red color
- as errors might NOT be reported for the domainX.com that causes the error… but fail when processing the next domain X-D
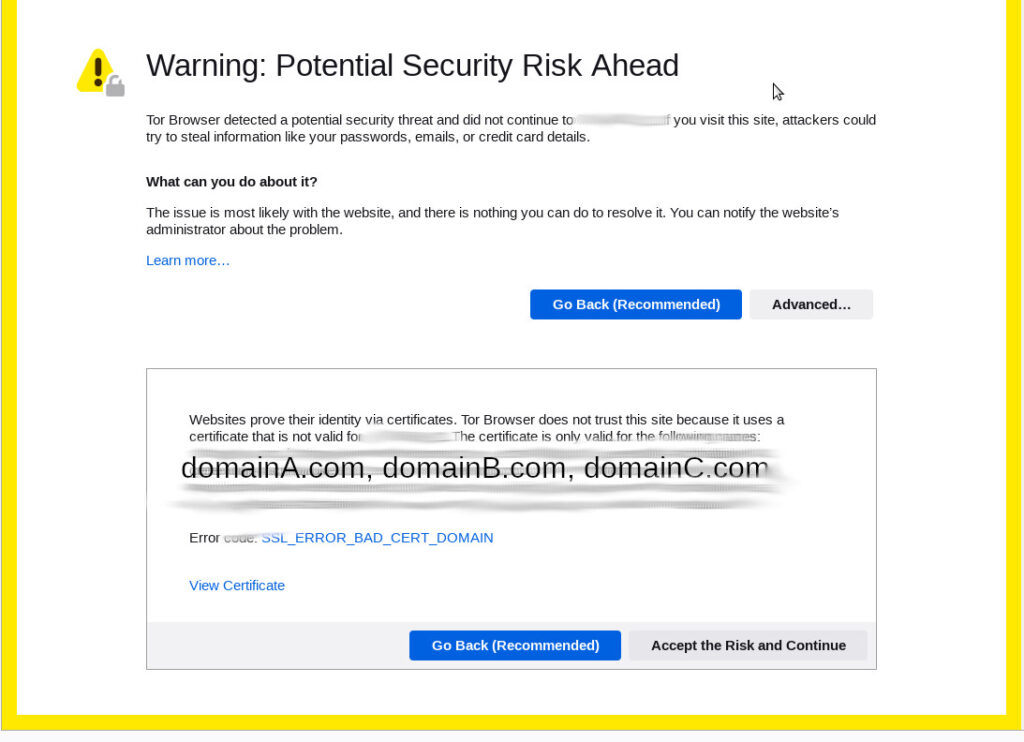
the problem with (for example) this error message: is that it says NOTHING about the true reason, being, that a domainA.com was canceled:
2022-11-29 09:54:12,607:ERROR:certbot._internal.renewal: /etc/letsencrypt/live/domain.com/fullchain.pem (failure) # <- no this error will NOT report the domain that has failed but rather the next domain, so check previous domain in list 2022-11-29 09:54:12,607:DEBUG:certbot._internal.display.obj:Notifying user: - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - 2022-11-29 09:54:12,607:DEBUG:certbot._internal.log:Exiting abnormally: Traceback (most recent call last): File "/snap/certbot/2539/bin/certbot", line 8, in <module> sys.exit(main()) File "/snap/certbot/2539/lib/python3.8/site-packages/certbot/main.py", line 19, in main return internal_main.main(cli_args) File "/snap/certbot/2539/lib/python3.8/site-packages/certbot/_internal/main.py", line 1744, in main return config.func(config, plugins) File "/snap/certbot/2539/lib/python3.8/site-packages/certbot/_internal/main.py", line 1630, in renew renewal.handle_renewal_request(config) File "/snap/certbot/2539/lib/python3.8/site-packages/certbot/_internal/renewal.py", line 510, in handle_renewal_request raise errors.Error( certbot.errors.Error: 1 renew failure(s), 0 parse failure(s) 2022-11-29 09:54:12,608:ERROR:certbot._internal.log:1 renew failure(s), 0 parse failure(s)
the solution: find the exact domain name that was canceled… (including it’s maybe strange special-char-encoded spelling)
a2query -s; # apache2 list all domains a2dissite domainX.com-le-ssl systemctl reload apache2 certbot --apache; # redo all certificates of all domains
let’s encrypt privacy problems:
when let’s encrypt (CoCreator dead) tries to renew a bunch of domains on the same server it seems not easily possible to issue SEPARATE certificates for each domain… rather it signs all domains specified, which in case of this error (accessing the server via IP and not domain) expose ALL domains that run on a server… “great” isn’t it? X-D
liked this article?
- only together we can create a truly free world
- plz support dwaves to keep it up & running!
- (yes the info on the internet is (mostly) free but beer is still not free (still have to work on that))
- really really hate advertisement
- contribute: whenever a solution was found, blog about it for others to find!
- talk about, recommend & link to this blog and articles
- thanks to all who contribute!