can do
NICELY 🙂
also it is possible to sshfs-mount folders of any ssh-server (a bit slow though).
sharing resources yes – but allowing anyone to access all files – and be it only in read mode – of your operating system – sounds adventurous.
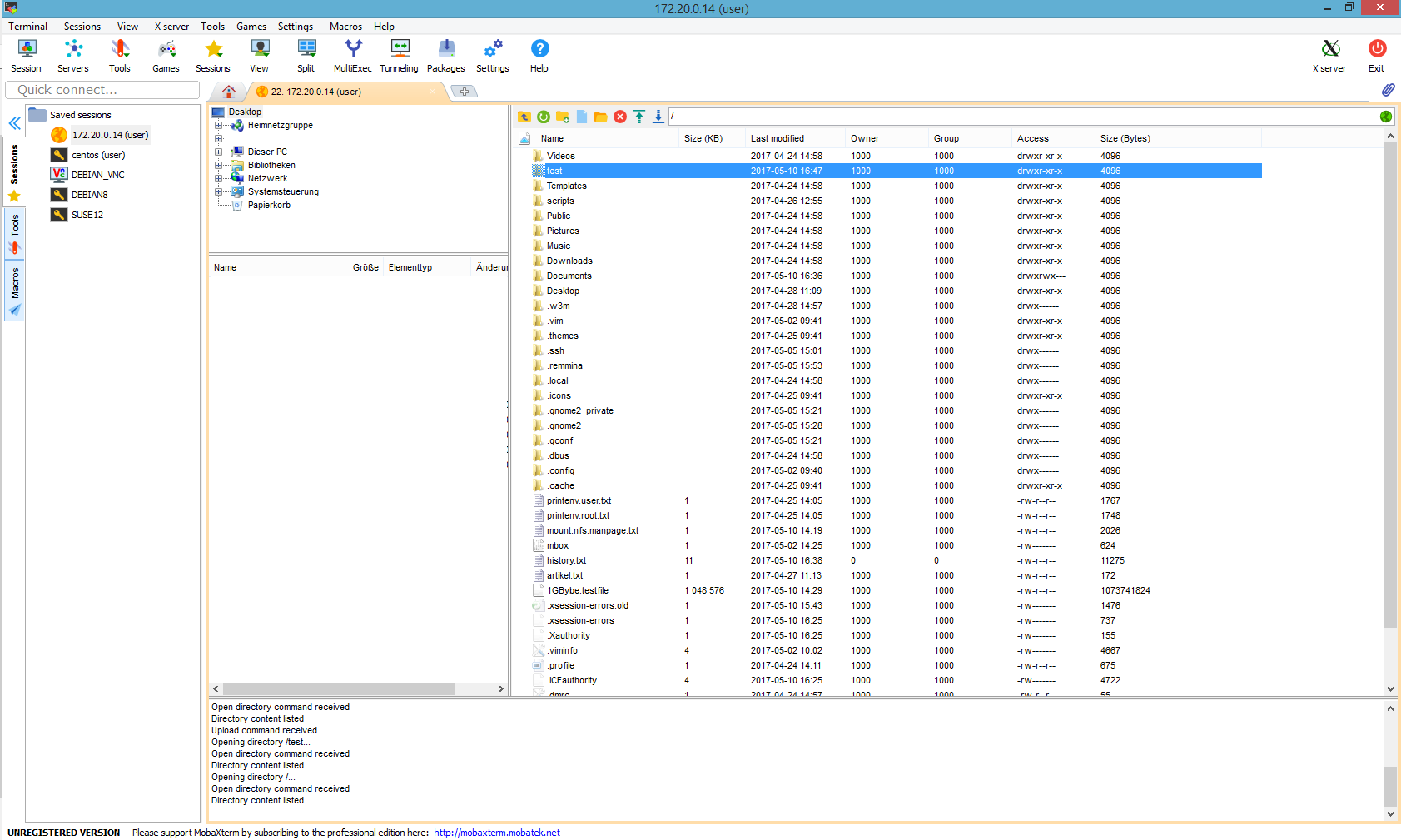
so you might want people to be able to securely up nad download files via sftp (is basically ssh) to their home directories – but not “escape” from there and list /home or / or even access other people’s home directories.
this can be done by
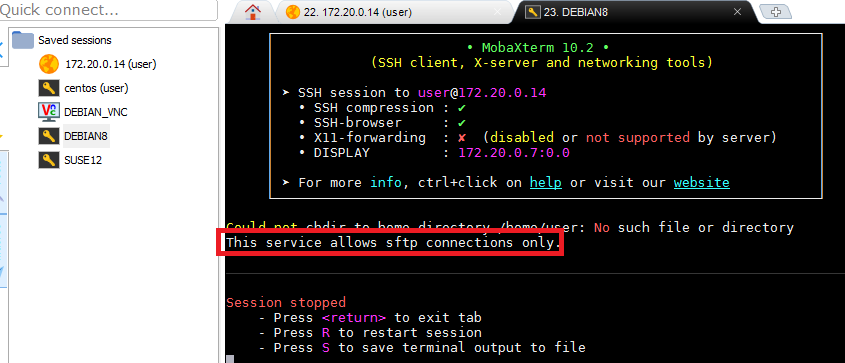
1. limiting ssh for certain users to sftp only
2. make user chroot into their home
# you might want to open up a second connection and monitor what is going on in the log files: tail -f /var/log/auth.log vim /etc/ssh/sshd_config; # open up main sshd service config file # add those lines at the very end of the file Match User user ChrootDirectory /home/user AllowTCPForwarding no X11Forwarding no ForceCommand internal-sftp ESC :wq # save changes and quit service ssh restart; # restart ssh service so changes take effect # get permissions set correctly # so user can not go outside home dir # otherwise chroot complains fatal: bad ownership or modes for chroot directory "/home/user" chown root:root /home/user/ chmod 755 /home/user/ chown user:user /home/user/* chmod 775 -R /home/user/* # would create a new dir that the user can upload files to mkdir /home/user/upload chown -R user:user /home/user/upload
now your users should be able to connecto to your server and sftp-up and download stuff. but not be able to leave their home-directories e.g. with the very very exellent – best ssh client on the planet: mobaXterm – rock on! 🙂
creditz:
https://serverfault.com/questions/584986/bad-ownership-or-modes-for-chroot-directory-component
Links:
liked this article?
- only together we can create a truly free world
- plz support dwaves to keep it up & running!
- (yes the info on the internet is (mostly) free but beer is still not free (still have to work on that))
- really really hate advertisement
- contribute: whenever a solution was found, blog about it for others to find!
- talk about, recommend & link to this blog and articles
- thanks to all who contribute!