WARNING: use at own risk!
use a dedicated computer for shredding harddisk, that has no valuable data stored or attached (in case the operator enters the wrong drive letter = all data gone)
have been warned! WARNING!
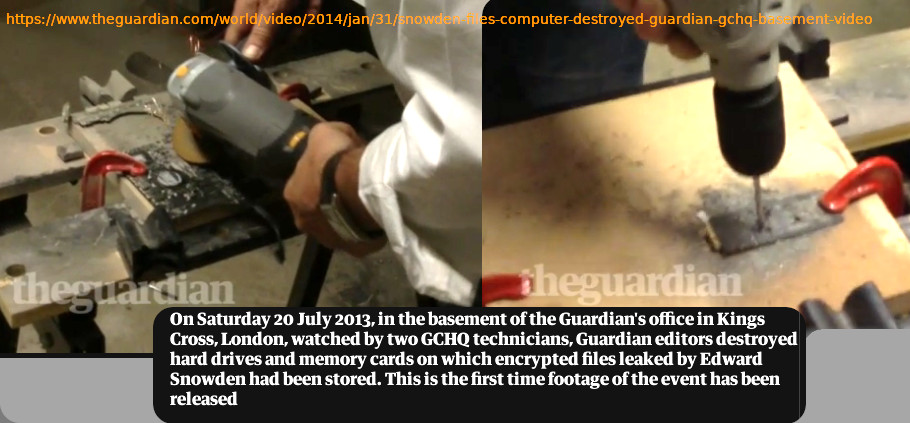
this method might not be good for state secrets or military and top secret data!
for top secret data it is better to physically destroy the device
some users (not the one) think it’s fun to shop on eBay for second hand harddisks and look at restoring the data on it and in many cases, this data scavenging actually is successfull (especially if the harddisks come from private sellers and not come from professional refurbishment companies that have to follow strict laws and regulations on wiping harddisks, and might even have specialized software for the job)
if the user wants to securely erase files and directories look at srm and this article.
if the user wants to wipe an entire harddisk (magnetic or ssd), this script will dd one’s harddisk with zeros and random numbers from /dev/random (checkout how /dev/random works, depending on the system it could be very slow)
the script(s) will ask the user if the drive letter entered is correct, and the user should double tripple check with this script.
hostnamectl; # tested with Operating System: Debian GNU/Linux 12 (bookworm) Kernel: Linux 6.1.0-13-amd64 # nice tool shred (shred.man.txt) su - root apt update apt install coreutils # WARNING! TRIPPLE DOUBLE CHECK THE DRIVE LETTER IS CORRECT # either by detach + attach then run dmesg # will show something like [13596.731126] sd 7:0:0:0: [sdc] 5860533168 512-byte logical blocks: (3.00 TB/2.73 TiB) [13596.731129] sd 7:0:0:0: [sdc] 4096-byte physical blocks [13596.731288] sd 7:0:0:0: [sdc] Write Protect is off [13596.731289] sd 7:0:0:0: [sdc] Mode Sense: 53 00 00 08 [13596.731598] sd 7:0:0:0: [sdc] Disabling FUA [13596.731600] sd 7:0:0:0: [sdc] Write cache: enabled, read cache: enabled, doesn't support DPO or FUA [13596.732058] sd 7:0:0:0: [sdc] Preferred minimum I/O size 4096 bytes [13596.732059] sd 7:0:0:0: [sdc] Optimal transfer size 33553920 bytes not a multiple of preferred minimum block size (4096 # so user knows it's sdc # start the process shred --verbose --random-source=/dev/urandom -n1 --zero /dev/sdX shred: /dev/sdX: pass 1/2 (random)... shred: /dev/sdX: pass 1/2 (random)...654MiB/2.8TiB 0% shred: /dev/sdX: pass 1/2 (random)...1.3GiB/2.8TiB 0% shred: /dev/sdX: pass 1/2 (random)...2.0GiB/2.8TiB 0% # or with a manual script that also can do logging # create a new script vim /scripts/shred_harddisk.sh # for personal use (no logs generated) # requirements: hdparm su - root apt update apt install hdparm #!/bin/bash # erase all data on harddisk by overwriting with /dev/random if [ -z "$1" ] then echo "please pass device like this: /dev/sdb TARGET THE WHOLE DEVICE (sdb) NOT A PARTITION! (sdb1) WARNING! THIS WILL ERASE ALL DATA BY OVERWRITING THE COMPLETE HARDDISK WITH RANDOM DATA THERE IS NO POSSIBILITY TO BRING BACK THE DATA!!! USER ONLY ON DEDICATED COMPUTER THAT HAS NO ACCESS TO ANY VALUABLE DATA USE AT YOUR OWN RISK!!! " else echo "========== does the user want to erase all data by overwriting device "$1" with random data?" echo " WARNING! THIS WILL ERASE ALL DATA OF $1 BY OVERWRITING THE COMPLETE HARDDISK WITH RANDOM DATA THERE IS NO POSSIBILITY TO BRING BACK THE DATA!!! (except for state actors with access to expensive tech such as using magnetic force microscopy (MFM) and scanning tunneling microscopy (STM) techniques) for the average user: overwriting one pass should be okay (large 2TB and more usb disks takes 3 days!!!) for users with sensitive data: overwrite with no less than 38x times (srm standard) so for top secret: it is better to take harddisk apart and destroy it physically with an angle grinder info on Harddisk: === model === $(hdparm -I $1|head)" read -p "Continue (y/n)?" choice case "$choice" in y|Y ) echo "yes";; n|N ) echo "no";; * ) echo "invalid";; esac sync; echo "=== umounting all partitions of" $1 umount $1*; echo "=== start process monitor" watch kill -USR1 $(pgrep ^dd) & echo "=== overwriting" dd if=/dev/urandom of=$1 bs=1M conv=notrunc; sync; fi # long version (for companies that do refurbishment and need the logs) #!/bin/bash echo "=================== secure & fast wipe harddisk script v1.0 by dwaves.org GPLv2 ===================" echo "it is recommended that you run this script inside a screen session, you can label the session according to the harddisk-3-letter-id, example: screen -S sdd" echo "please modify the script line 'operator=' to specify who is responsible for deleting the harddisk" # 4. operator of the machine operator="operator operator@domain.de"; # change into log dir cd /root/deleteLogs harddisk=$1 harddiskID=$2 # list all available harddisks val= if [[ -z "$harddisk" ]] then lsblk read -p "what harddisk would you like to wipe? (please enter the 3xletter id):" harddisk echo " =================== =================== ===================" fi val= if [[ -z "$harddiskID" ]] then read -p "my refurbish-workflow of harddisks works like this: 1. you buy second hand pcs 2. you label the pcs with permanent marker with a pcID-number 3. you label every harddisk with pcID:harddiskID number 4. you start this script and pass the pcID:harddiskID number, so you will know in the logs what harddisk was wiped please enter the harddiskID :" harddiskID echo " =================== =================== ===================" fi # 2. serial of harddisk # remove all whitespace: | tr -d ' ' # replace whitespace with underscore: safename="$(echo $filename | sed 's/ /_-_/g')" hdmodel=$(hdparm -I /dev/$harddisk|grep Model) hdserial=$(hdparm -I /dev/$harddisk|grep Serial) filename=$(date +%Y-%m-%d)_$(echo $hdmodel)_$(echo $hdserial)_delete.log filename="$(echo $filename | sed 's/ /_-_/g')" # 3. date of deletion touch "$filename" echo $(date "+DATE-%Y-%m-%d-TIME-%H-%M-%S")" Log datei angelegt." >> "$filename"; # 2. write serial of harddisk to file echo "=============== harddisk model & serial =============" >> "$filename"; echo "Self-Labeled-harddiskID:"$harddiskID >> "$filename"; echo $hdmodel >> "$filename"; echo $hdserial >> "$filename"; echo "=====================================================" >> "$filename"; # 4. who operated the machine echo $operator >> "$filename"; # 5. what way of deletion was taken echo "method of deletion: debian-dd one pass with zeros, one pass with random data - securely erase files from magnetic media" >> "$filename"; # 1. seriennummer von pc echo "================= system informations ============" >> "$filename"; dmidecode|grep -A 13 "System Information" >> "$filename"; echo "==================================================" >> "$filename"; # 6. wipe with zeros echo $(date "+DATE-%Y-%m-%d-TIME-%H-%M-%S")" wipe with zeros" >> "$filename"; dd if=/dev/zero of=/dev/$harddisk bs=4k conv=notrunc count=1024MB >> "$filename"; # 7. wipe again with random data echo $(date "+DATE-%Y-%m-%d-TIME-%H-%M-%S")" wipe again with random data" >> "$filename"; dd if=/dev/urandom of=/dev/$harddisk bs=4k conv=notrunc # shred -vfz -n 100 /dev/sda echo "WIPE "$harddisk" ?"; # wipe -fkq /dev/$harddisk # Assuming /dev/hda3 is the block device corresponding to the third partition of the master drive on the primary # IDE interface, it will be wiped in quick mode (option -q) i.e. with four random passes. The inode won't be # renamed or unlinked (option -k). Before starting, it will ask you to type ``yes''. echo $(date "+DATE-%Y-%m-%d-TIME-%H-%M-%S")" overwrite-shred harddisk finished: " >> "$filename";
# how to run
chmod u+x /scripts/*.sh /scripts/shred_harddisk.sh sdd 10.2
# example output:
DATE-2013-09-20-TIME-10-10-27 Log datei angelegt.
=============== harddisk model & serial =============
Self-Labeled-harddiskID:10.2
Model Number: ST34342A
Serial Number: VG561565
=====================================================
Operator Name operator@domain.com
Löschmethode: debian-dd one pass with zeros, one pass with random data - securely erase files from magnetic media
================= system informations ============
System Information
Manufacturer: FUJITSU SIEMENS
Product Name: A8NE-FM
Version: 1.XX
Serial Number: 123456789000
UUID: 11111111-1111-1111-1111-111111111111
Wake-up Type: Power Switch
Handle 0x0002, DMI type 2, 8 bytes
Base Board Information
Manufacturer: ASUSTek Computer INC.
Product Name: A8NE-FM
Version: 1.00
Serial Number: 123456789000
==================================================
DATE-2013-09-20-TIME-10-10-27 wipe with zeros
2013-09-20_Model_-_Number:_-_ST34342A_Serial_-_Number:_-_VG561565_delete.log (END)
comments:
it’s quiet a challenge… to find some good (not super expensive blancco) software that will help you with refurbishing your harddisks/pcs before selling them.
it is said, that if you overwrite your harddisk in alternating ways with 1 and 0 (first all 1 then all 0 then again 1) then random data from /dev/random that you have a pretty secure way of deleting/erasing.
The german VSIIR-Standard recommends a 7x Pass overwrite.
On a SATA-Harddisk with 250GB this could take you days.
So i said, okay, without wasting enormous amounts of energy, let’s do 3x passes.
one with zeros and one with random data from /dev/random (high cpu usage!) (there is frandom which is doing better but i did not test it yet)
what is also important: Logging!
this script will log the model number of your harddisk and the serial & the operator responsible.
1. before you sell your hardware
2. you label the pcs with permanent marker with a pcID-number
3. you label every harddisk with pcID:harddiskID number
4. you start this script and pass the pcID:harddiskID number, so you will know in the logs what harddisk was wiped
here is another interesting article about this problem:
Multipass Overwrite: One pass already pretty good
“The Urban Legend of Multipass Hard Disk Overwrite” and DoD 5220-22-M
In 1996, Peter Gutmann presented a paper [GUT96] at a USENIX Security Symposium in which he claimed that overwritten data could be recovered using magnetic force microscopy (MFM) and scanning tunneling microscopy (STM) techniques.
This seminal paper alerted many people to the possibility that data which had been overwritten on an HDD could be recovered using such techniques.
Lacking other research in this area, and despite a lack of corroboration, many of those people adopted Gutmann’s conclusions and recommendations and have ever since believed that multiple overwrites are required to effectively render remnant data irretrievable.
Gutmann’s ultimate recommendation was that no fewer than 35 (!) overwrite passes should be performed to ensure that the original data cannot be retrieved.
However, in the context of current HDD technology, there are several problems with Gutmann’s work:
- Gutmann focused on two disk technologies — modified frequency modulation and run-length-limited encoding — that rely on detection of a narrow range of analog signal values and have not been used for HDDs in the last 10-15 years. Modern HDDs use various kinds of partial-response maximum-likelihood (PRML) sequence detection that uses statistical techniques to determine the maximum likelihood value associated with multiple signal detections [WRIG08].
- Further, areal density (density of data per square unit of area, the product of bit-per-inch linear density and track-per-inch track density) has increase by at least three orders of magnitude [SOBE04] [WIKI08] since the publication the Gutmann paper. To achieve such densities, head positioning actuators have become significantly more accurate and repeatable.
- Moreover, Gutmann’s work paper was theoretical, and I am not aware of any practical validation that data could be recovered using the techniques he described.
Gutmann’s work has resulted in the formation of an urban legend: that the US government requires a 3-pass overwrite and specifies it in DoD 5220-22-M.
What about those often-cited US Government standards?
There are many HDD overwrite standards from which to choose [BLAN08]. Among those that are often cited in both procurement and product specifications are DoD 5220.22-M and NSA 130-1. Less often cited, but more current, is NIST SP 800-88.
DoD 5220-22-M
DoD 5220-22-M is the National Industrial Security Program Operating Manual (NISPOM), which a broad manual of procedures and requirements for government contractors handling classified information.
The 1997 version of this document [DOD_97] specified that rigid magnetic disks should be sanitized by writing some character, its complement, and then a random character. However, this “algorithm” was removed from subsequent issues of the NISPOM.
Indeed, the entire table of clearing and sanitization methods is no longer present in the current issue of NISPOM [DOD_06].
NSA 130-1
NSA 130-1 may well have specified a clearing or sanitization procedure by writing a random character, another random character, and then a known value. However, I am not able to find a copy of NSA Manual 130-1 or 130-2 (perhaps they were classified documents).
However, the current issue of the NSA/CSS Storage Device Declassification Manual [NSA_07] (Manual 9-12, which supersedes Manual 130-2) does not specify any overwriting methods for HDDs, and instead requires degaussing or physical destruction.
It is not clear to me if the DoD and NSA no longer recommend overwrite methods because they are ineffective or because their effectiveness as a single technique is uncertain when applied to a variety of HDD technologies.
NIST Special Publication 800-88
The National Institute of Standards and Technology has a special publication “Guidelines for Media Sanitization” that allows HDD clearing by overwriting media “using agency-approved and validated overwriting technologies/methods/tools”.
For purging, it specifies the Secure Erase [UCSD10] function (for ATA-based devices), degaussing, destruction, or the rather vague “purge media by using agency-approved and validated purge technologies/tools”.
The original issue of SP 800-88 [NIST06-1] claimed that “Encryption is not a generally accepted means of sanitization. The increasing power of computers decreases the time needed to crack cipher text and therefore the inability to recover the encrypted data can not be assured”, but that text was removed from SP 800-88 Revision 1 which was issued one month later.
Most interestingly, SP 800-88 states that “NSA has researched that one overwrite is good enough to sanitize most drives”. Unfortunately, the NSA’s research does not appear to have been published for public consumption.
view online: http://www.fylrr.com/archives.php?doc=NISTSP800-88_rev1.pdf
mirror: NISTSP800-88_with-errata
Current Research
Fortunately, several security researchers presented a paper [WRIG08] at the Fourth International Conference on Information Systems Security (ICISS 2008) that declares the “great wiping controversy” about how many passes of overwriting with various data values to be settled: their research demonstrates that a single overwrite using an arbitrary data value will render the original data irretrievable even if MFM and STM techniques are employed.
The researchers found that the probability of recovering a single bit from a previously used HDD was only slightly better than a coin toss, and that the probability of recovering more bits decreases exponentially so that it quickly becomes close to zero.
Therefore, a single pass overwrite with any arbitrary value (randomly chosen or not) is sufficient to render the original HDD data effectively irretrievable.”
References
- [BLAN08] Blannco Certified Data Erasure Software. “Recognized Overwriting Standards” (http://www.dataerasure.com/recognized_overwriting_standards.htm).
- [DOD_06] Department of Defense – Department of Energy – Nuclear Regulatory Commission – Central Intelligence Agency (February 2006). “DoD 5220.22-M National Industrial Security Program Operating Manual (NISPOM)” (http://www.dss.mil/isp/odaa/documents/nispom2006-5220.pdf).
- [DOD_97] Department of Defense – Department of Energy – Nuclear Regulatory Commission – Central Intelligence Agency (July 1997). Obsolete version of “DoD 5220.22-M National Industrial Security Program Operating Manual (NISPOM)” (http://www.usaid.gov/policy/ads/500/d522022m.pdf).
- [FEEN07] Daniel Feenberg (2007?). “Can Intelligence Agencies Recover Overwritten Data?” (http://www.nber.org/sys-admin/overwritten-data-guttman.html).
- [GUTM96] Peter Gutmann (July 1996). “Secure Deletion of Data from Magnetic and Solid-State Memory” (http://www.cs.auckland.ac.nz/~pgut001/pubs/secure_del.html).
- [NIST06-1] NIST (August 2006). “Special Publication 800-88: Guidelines for Media Sanitization” (http://web.archive.org/web/20060902043637/csrc.nist.gov/publications/nistpubs/800-88/SP800-88_Aug2006.pdf).
- [NIST06-2] NIST (September 2006). “Special Publication 800-88: Guidelines for Media Sanitization, Revision 1” (http://www.fylrr.com/archives.php?doc=NISTSP800-88_rev1.pdf).
- [NSA_07] National Security Agency – Central Security Service (December, 2007) “NSA/CSS STORAGE DEVICE DECLASSIFICATION MANUAL” (http://www.nsa.gov/ia/_files/Government/MDG/NSA_CSS_Storage_Device_Declassification_Manual.pdf).
- [SOBE04] Charles Sobey (April 2004). Recovering Unrecoverable Data — The Need for Drive-Independent Data Recovery (http://www.actionfront.com/whitepaper/Drive-Independent%20Data%20Recovery%20Ver14Alrs.pdf).
- [UCSD10] UC San Diego Center for Magnetic Recording Research, 2010. “Secure Erase” (http://cmrr.ucsd.edu/people/Hughes/SecureErase.shtml).
- [WIKI08] Wikipedia (2008). “Hard drive capacity over time.png” (http://en.wikipedia.org/wiki/File:Hard_drive_capacity_over_time.png).
- [WRIG08] Craig Wright; Dave Kleiman; R.S. Shyaam Sundhar (December 2008). “Overwriting Hard Drive Data: The Great Wiping Controversy” Lecture Notes in Computer Science (Springer Berlin / Heidelberg); ISBN 978-3-540-89861-0 (http://www.springerlink.com/content/408263ql11460147/). Some pages available for preview in Google Books.
so…
when deleting data from disk or stick, it is best to use wipe and srm and if rm -rf was used.
zero-out the device (create a file that is very very big and contains random data or zeroes) like this:
/scripts/zero_out.sh
time dd if=/dev/zero of=./zero_out_space bs=1M; rm -rf ./zero_out_space;
links:
https://wiki.archlinux.org/title/Securely_wipe_disk
liked this article?
- only together we can create a truly free world
- plz support dwaves to keep it up & running!
- (yes the info on the internet is (mostly) free but beer is still not free (still have to work on that))
- really really hate advertisement
- contribute: whenever a solution was found, blog about it for others to find!
- talk about, recommend & link to this blog and articles
- thanks to all who contribute!